sudo (su 'do')
What is sudo (su 'do')?
Sudo is a command-line utility for Unix and Unix-based operating systems such as Linux and macOS. The utility provides an efficient way to temporarily grant users or user groups privileged access to system resources so that they can run commands that they cannot run under their regular accounts. Users can even be granted permissions to run commands under the root account -- the most powerful account on Unix-like systems. Sudo also logs all commands and arguments so that administrators can track the behavior of sudo users.
Many sources state that sudo stands for superuser do, which was true in the past. However, the group that develops sudo stopped using that description more than 10 years ago. According to the group's website, sudo now means su "do," which suggests a tool that delivers su-like capabilities.
Su is a command-line utility and stands for switch user or substitute user. Like sudo, the utility enables a user to run commands under a different account. However, sudo has some important advantages over su.
How does the sudo command work?
With sudo, when a user runs a command, they are prompted for the password of their own account, not the privileged account. The user can then run other commands without providing a password each time, but there's a limit to how long.
By default, a session ends after five minutes of inactivity, and the user must again enter a password. However, administrators can set the time to something other than five minutes when configuring sudo.
With su, the user can manually switch to root or another privileged account using the name and password for that account. The account remains active until the user specifically changes back to the original account. This approach works fine, but it can be risky.

For example, an administrator might use su to switch to the root account, run a few system commands and then go do something else, forgetting about the privileged connection. If the administrator were to then return to the console and inadvertently run a bad command, there could be an inordinate amount of damage, not to mention the increased security risk.

Sudo helps to minimize such risks, while providing system administrators with greater control. An administrator can do the following:
- Configure the sudoers file to grant specific users or groups the ability to run some or all commands under the root account or another privileged account.
- Maintain granular control over which commands a user can run on each host, based on command names and their directory locations.
- View logged activity that shows which sudo users ran which commands and when they ran them.
- Control how long users can run commands at a privileged level after they've entered their passwords.
- Configure settings related to sudo plugins, file paths, debugging and the front-end interface.
- Maintain a single sudoers file that controls access for multiple users across multiple systems.
How to run sudo at the privileged level
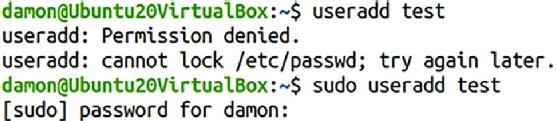
To use sudo to run a command at a privileged level, the user simply precedes the command with the sudo keyword, assuming an administrator has granted them the necessary privileges in the sudoers file. For example, a user might run the following command to edit a system's host file.
sudo vi /etc/hosts
If the user tries to run this command without including sudo and does not have the necessary permissions, the host system will return a message stating that access is denied. By including sudo, the user can now retrieve and edit the file's contents at the privileged level.
Learn more about the differences between su and sudo commands.






