The importance of data security in the enterprise
Three industry experts discuss the criticality of data security in the enterprise, including the significance of data breaches and compliance regulations.
Data is valuable to all organizations. Some companies base their entire business model on their strategic use of data -- making it their most precious asset.
Protecting and securing data is, therefore, a top priority for executives. CEOs identified cyber-risk as their top concern for 2022, with 49% of chief executives listing it as the threat they're most worried about -- ahead of pandemic-related concerns and macroeconomic volatility -- in PwC's "25th Annual Global CEO Survey."
"All businesses have data that's valuable and that has to be protected," said Candy Alexander, international president at Information Systems Security Association, a nonprofit organization for information security professionals and practitioners.
What is data security?
Data security is all about safeguarding an organization's data from unauthorized access, use or changes, as well as theft and tampering throughout the data's lifecycle, from collection to deletion.
This article is part of
What is data security? The ultimate guide
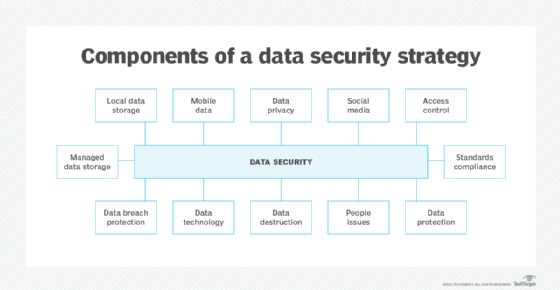
That straightforward objective, however, is underpinned by a complex discipline, which involves the following:
- identifying the data assets held by the organization;
- determining the level of protection each data element warrants based on its value to the enterprise, regulations that could govern it and other factors;
- identifying data security threats; and
- deciding how best to protect data based on its classification and cost.
The data security discipline relies on the implementation and management of complex layers of policies, procedures and technologies.
Organizations that fail to effectively secure their valuable or regulated data expose themselves to significant risks, ranging from reputational damage and regulatory fines to operational interruptions and bankruptcy.
"There are companies that cease to exist because of a data breach," said Alex Holden, CISO at consulting firm Hold Security and member of the ISACA Emerging Trends Working Group.
Impact of a data breach
The PwC survey identified how executives believe a cyber incident, such as a data breach, would affect their business, with 62% saying it would inhibit their ability to sell products and services, 19% saying it would inhibit their ability to raise capital, and 17% agreeing that it would negatively affect their employee recruitment and retention efforts.
"I've seen organizations have to revert back to paper and pen as they deal with the incident," said Tim Rawlins, senior advisor and director of security at IT security firm NCC Group.
Executives can also expect big bills should a data breach occur. The average total cost for a data breach in 2021 was $4.24 million, up from $3.86 million in 2020, according to Ponemon Institute and IBM Security's 2021 "Cost of a Data Breach" report.
Organizational leaders will face multiple breach-related expenses, according to both experts and reports. First are immediate remediation costs, which typically include paying for technical and security personnel to identify how the breach occurred, close security gaps and determine the extent of the damage.
Immediate costs could also include paying a ransom, in the case of a ransomware attack where organizational data and systems are held hostage, Rawlins said. Subsequent bills could ensue, such as paying to restore damaged systems or paying to monitor credit reports for individuals whose sensitive data was exposed. Organizations will likely have regulatory fines and legal expenses as well.
Costs associated with lost opportunities will also arise. Teams focusing on investigations, repairs and other fallout from the breach won't have time to work on initiatives to move the company forward.
"We've seen organizations take over a year to get back up and running," Rawlins said.
The human impact is another consequence, experts said. Employees are often tasked with working long hours in the aftermath of an incident, leading to stress, burnout and resignations. Many executives will feel the fallout, too, as they're often blamed for the incident and, consequently, have their tenures cut short.
The impact doesn't end there. Data breaches often affect a range of stakeholders, too. "It's far more than most people think. It's suppliers, shareholders, your board and customers," Rawlins said.
A data breach also affects an organization's reputation as stakeholders lose trust -- a consequence that carries long-term costs and is difficult to address. "Cyber insurance won't restore the trust of your customer," Holden said.
Why data security is more important now than ever
Organizations and their executives have been required to protect certain information and data points -- by law and for business survival -- since well before the digital age. Banks, for example, have long safeguarded their customers' account information. Computers and digital systems, however, have compounded the issue, creating more data, as well as more types of data and varying value amounts associated with data.
Enterprise leaders have evolved their views on how they secure the data they collect, store and use, Holden said. They typically recognize some data -- such as an individual's name -- as public information that does not require protection. They classify other data and combinations of data -- such as personally identifiable information -- as nonpublic, with varying levels of sensitivity and value. Thus, this type of data needs varying levels of protection and regulatory requirements.
In recent decades, governments have also stepped up their efforts to ensure organizations are appropriately safeguarding personal data. One of the most sweeping laws to go into effect is 2016's GDPR. It was followed by CCPA, enacted in California in 2018. Since then, four other states -- Colorado, Connecticut, Virginia and Utah -- passed data protection regulation laws, all of which are set to go into effect in 2023. Five additional states have data privacy and security bills under active consideration as of summer 2022, according to the International Association of Privacy Professionals' Legislation Tracker.
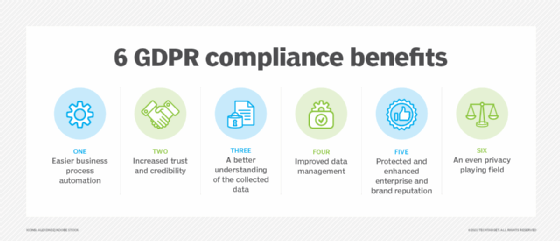
Some industries have set standards and policies for data security as well. The Payment Card Industry Security Standards Council, for example, established PCI DSS for all companies that collect, store, processes or transmit credit card data.
The U.S. federal government has also passed industry-specific laws that address data security requirements. HIPAA mandates for securing individual medical information is a prominent example.
Moving forward, Alexander said enterprise security teams and other organizational leaders are likewise evolving their data security strategies to meet regulations amid increasing public demand for good data stewardship.
"We've already begun the shift," she said. "The old model of security, of building a wall [around systems and data], isn't working because the data is so fluid now and it's everywhere. We need to focus on protecting that data element at the most minute level. And we're seeing that now in new classes of solutions and around the data-centric security model."







