
Getty Images
5 ways to overcome multifactor authentication vulnerabilities
Improve the resiliency of multifactor authentication by giving users more information, making default settings more secure, hiding secrets and more.
Multifactor authentication boosts the safety of usernames and passwords, but depending on the MFA method used, it may not offer as much protection as you might think.
To better secure user accounts and data, it's time to make MFA more resilient.
At Authenticate 2022, Roger Grimes, data-driven defense evangelist at security awareness company KnowBe4, presented how vendors can improve their MFA products.
MFA can still be hacked
MFA provides more protection than just a username/password combo, but it is still hackable and phishable. A report from identity and access management provider Auth0 found MFA bypass attacks are at their highest levels ever -- and far higher than in 2021 -- with 113 million attacks recorded in the first three months of 2022.
To make things more difficult, attackers use automated toolkits, such as EvilProxy, to bypass MFA.
The level of protection offered by MFA depends on the type of MFA used. Text messaging and email are particularly weak. In 2016, NIST recommended text not be used as an account recovery option.
Other MFA methods, such as biometrics and push-based notifications, are more resilient to attackers, but even these aren't perfect. For example, attackers often annoy users into approving an authentication notification via an attack known as MFA bombing. Lapsus$ attackers MFA bombed an Uber contractor with repeated requests until one was approved.
How to make MFA more resilient
Vendors offering MFA products should make them as resilient to attacks as possible. In his presentation, Grimes outlined five options vendors should consider implementing.
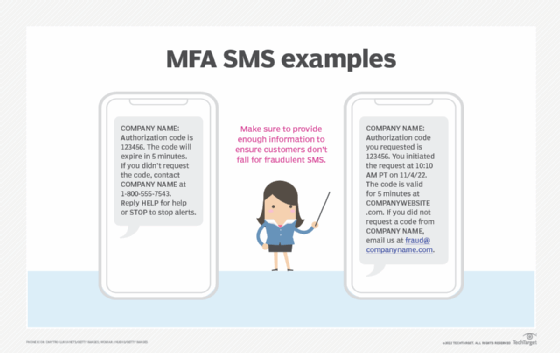
1. Provide enough information to customers
The first option is the simplest to implement. Provide users with enough information to make a decision before they approve a push notification or click a link in a text/email message. Grimes suggested that MFA notifications be more than just a code. Instead, provide users with the who, what, where and why so they can make a reasonable decision before acting. Vendors should also include information on how to report abuse.
2. Embrace secure programming
When designing MFA methods, vendors should use the secure development lifecycle. This includes having an in-house code review and internal penetration test, as well as hiring external pen testers, participating in bug bounties and investigating relevant hacking reports. Vendors should also create and share a threat model on how MFA methods could be attacked, from social engineering to man-in-the-middle attacks to a reliance on third parties -- for example, DNS, Active Directory, etc.
3. Set secure defaults
Customers don't always pay attention to security or other settings, leaving them at the mercy of default settings. Vendors should make defaults as secure as possible. For example, set an application to fail-close instead of fail-open if an error or exception occurs during authentication. Vendors must also disable older, vulnerable, legacy protocols.
4. Hide or transform secrets
Organizations should never save secrets in plaintext. Numerous data breaches have shown why this is a security fail. Rather, organizations should hide or transform secrets to prevent attackers from using them in the wake of a successful breach. Options to do this include the following:
- Use tokens to store secrets in a nonreversible state.
- Transform secrets using Dynamic Symmetric Key Provisioning Protocol.
- Use homomorphic encryption.
5. Prevent brute-force attacks
MFA products should prevent brute-force attacks. One way to do this is to enforce account lockouts after multiple failed login attempts. Setting strict rate limiting or throttling can also prevent hackers from continually attempting to log in within a set time period.
Extra options for MFA resiliency
Some additional ways to make MFA more resilient are the following:
- Set authentication secrets to expire within a set time period.
- Use existing cryptographic methods instead of devising your own.
- Make MFA crypto-agile.
- Educate users on how to properly use MFA, and explain that no MFA method is infallible.







