
CISA aims to reduce email threats with serial CDR prototype
CISA officials at RSA Conference 2023 showed off a prototype designed to measure the risk of suspicious files and remove them from email and web services.
SAN FRANCISCO -- CISA issued a call-to-action on Wednesday to improve email security through a new approach for scoring and reducing malicious files.
Olga Livingston, senior economist at CISA, and Thomas Ruoff, chief of the methodology branch in CISA's vulnerability management division, led an RSA Conference session titled "Wanna Get Malware Out of Emails? CISA's Latest Research" to provide attendees with actionable steps to evaluate and mitigate what they called risk content. Over the past four years, CISA conducted two pilot tests using a Content Disarm and Reconstruction (CDR) approach to examine email attachments to sort out files that did not belong.
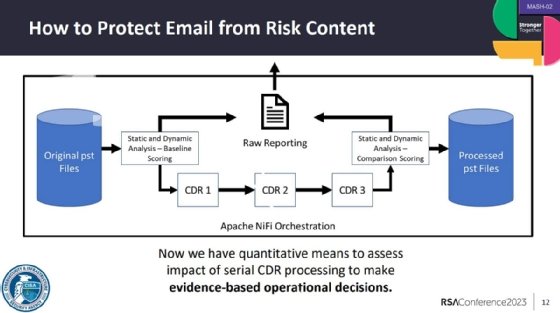
Ruoff said CISA's prototype platform for risk content scoring and reduction uses CDR technology, which is designed to remove or sanitize potentially malicious code from a file. He explained that the approach is different than antimalware analysis because CDR doesn't necessarily identify if a file is malware but instead removes components that do not adhere to a system's policies.
Ruoff said the prototype platform has serial CDR, which feeds the results of one CDR product into a second product for review and then possibly a third. "What our research found is that CDR products -- regardless of the name – are highly effective. But they are really, really effective when you use one, and then another, and then another."
The results of the prototype tests showed more than 90% risk content reduction. CISA's goal now is to apply the methodology at scale for email and web services. Livingston highlighted several benefits, but ransomware reduction was one of the most significant as enterprises continually struggle to defend against the evolving threat.
"Talk to vendors, service providers and ask for this capability. For vendors -- you already have these tools; use them in this particular way and provide it to customers. Help the market start to adopt this," she said during the panel.
For the pilot tests, CISA built its risk content scoring and reduction platform from commercial tools, including Reversing Labs for static analysis; CrowdStrike Falcon Sandbox for dynamic analysis; and Glasswall, Opswat and PuriFile to sanitize the files with serial CDR. However, the speakers emphasized that other commercial tools can be implemented as well to achieve the same outcome.
The pilot tests focused on email attachments, and the platform was used to score malicious and suspicious email content. The first pilot test took place in 2019 with the Department of Homeland Security and MITRE. It reviewed more than 28,000 files, achieving a 93% risk reduction.
The second was conducted in 2021 and examined university students and employees using Microsoft 365. Incoming emails reached more than 12 million users. Using the platform, CISA determined 6% of student files and 7.9% of employee files contained risk indicators. Ultimately, the platform reduced risk content by 98%.
Now CISA's goal is to apply it more broadly to downloaded content by combining a virtual browser with a serial CDR system.
During the session, Ruoff challenged the audience to think about email and web security, and cybersecurity overall, as a control system that can be measured. Based on risk tolerance, Ruoff said enterprises can then determine what tools or other security measures need to be implemented to protect its email and web services.
"Is this easy to do? Maybe," Ruoff said during the session. "It's kind of hard. But we have extremely high confidence it can be done because a couple of vendors we worked with have done it with successful results."
The speakers repeatedly stressed that they know the approach is "technically effective and economically justifiable." One attendee questioned how feasible it would be for small to medium-sized businesses with fewer resources to implement the risk content approach. Livingston said that hopefully in the short term, MSPs and other service providers would implement serial CDR and extend those offerings to SMB customers. Eventually the level of the adoption for this risk content approach would allow the price to drop.
Arielle Waldman is a Boston-based news reporter covering enterprise security news.






