
ra2 studio - Fotolia
Explore the benefits of Azure AD vs. on-prem AD
A move to Office 365 doesn't require cutting the cord from on-premises Active Directory, but it is an option. Here's what you need to know when comparing Azure AD vs. on-prem AD.
The shift by many companies to adopt cloud services, such as Office 365, reduces some administrative overhead in some areas but increases it in others. A move to the cloud also makes it tricky for administrators to keep track of who has access to what.
With more organizations using cloud services and apps, such as Microsoft Teams, Power Apps and Power BI, more corporate data is in Microsoft's servers. Knowing who has access to this data and is interacting with it is part of the security strategy for CIOs and administrators. Having the right identity management solution is paramount, and that's where an Azure Active Directory (AD) vs. on-prem AD comparison comes into play.
Learn about the Azure AD vs. on-prem AD differences
On-premises AD has been around since the early versions of Windows Server and is the established identity provider for the enterprise. Microsoft also offers Azure AD, which packs many features that make it very attractive.
Is a move to this paid service worth the investment?
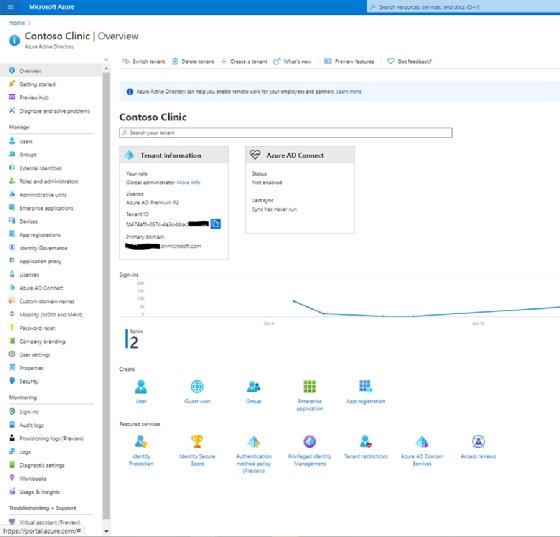
Organizations that subscribe to Office 365 also get the free edition of Azure AD for user management and authentication of Microsoft services. But a company that uses the cloud hasn't completely cut the tether from on-premises Active Directory. Office 365 communicates with the on-premises Active Directory via Azure AD Connect. Azure AD Connect runs on a server on the organization's network and accesses the local AD objects within the domain forest. Azure AD Connect synchronizes on-premises objects, such as security groups, user accounts contacts and other Active Directory attributes with Azure AD.
Azure AD operates in a comparable fashion to on-premises Active Directory, as both manage and support authentication for services and user memberships. But despite the similarities, there are several key capabilities in Azure AD that might nudge some enterprises to switch over.
Azure AD brings visibility to hacking attempts
One of the most common attacks on the Office 365 platform are hacking attempts for user credentials against the Exchange Online hosted email service. Without a tool, such as Azure AD, which reports both successful and failed logins against the system, monitoring for these types of attacks is difficult. Azure AD works with the Identity Protection tool to warn administrators of unauthorized access and account hijacking. To get the same functionality with on-premises AD would require paying for a third-party tool.
Azure AD offers seamless SSO for popular SaaS platforms
As more enterprises subscribe to more online services, single sign-on (SSO) helps end users avoid keeping track of multiple passwords for different sites.
Administrators will have to configure a third-party tool to implement SSO with their on-premises AD to connect to online services, such as Salesforce and LinkedIn. Azure AD does not require a third-party tool to get SSO working. As part of some of the paid plans for Azure AD Premium, such as the P1 or P2 plans, administrators can connect to different SaaS platforms with minimal effort.
Enhanced self-service for group membership within Azure AD
Microsoft introduced Office 365 Groups -- also called Microsoft 365 Groups -- in 2018 for workers to use a common workspace that holds emails, files and other collaborative resources. The advantage is the permissions model grants access to the resources in the workspace based on the team. It's very similar to the security groups feature in Active Directory.
However, the Office 365 Groups differ in that they can be managed by business users without relying on IT support to update Active Directory when there are changes to the membership. These groups are being used across many of Office 365 services such as Microsoft Teams, Outlook, Exchange Online, SharePoint and OneDrive. The only way to manage these groups is through the Azure AD admin portal, which provides a centralized view of group memberships that go across on-premises AD and Office 365.
Azure AD's features separate it from on-premises AD
There are additional components that make Azure AD an attractive add-on to use along with the on-premises AD, such as privileged identity management, tenant restriction capabilities, identity secure scores based on Microsoft's security recommendations and best practices, and identity protection services. These additions to secure your organization can be appealing for IT workers who want these enhanced capabilities that require no installation and very little configuration from an administrative standpoint.
License assignment flexibility and self-service in Azure AD
Another advantage Azure AD has over on-premises AD is the functionality to manage licenses for Microsoft services directly from the admin portal. Administrators can verify their current license counts and assign them to a user or a group without changing portals.
To use Azure AD, administrators must:
- Download and install Azure AD Connect from Microsoft's website.
- Select the appropriate Azure AD Connect configuration based on the existing setup of the environment and the desired scenarios needed for user sign-ins, which include any of the following: password hash sync, pass-through authentication, authentication using Active Directory Federation services, federation with PingFederate.
- Set up and configure Azure AD from the portal.azure.com URL.
- Connect and configure filtering of domain and organizational units.
- Select desired options from Azure AD Connect, such as directory extension attribute sync; group, password or device writeback; Azure AD app and attribute filtering; password hash synchronization; and directory extension attribute sync.
- Complete the setup and initiate the syncing of the objects.
Breaking down the differences in the Azure AD tiers
After this setup work is done and the on-premises AD communicates with Azure AD, the admin decides on the type of functionality needed. Microsoft offers several Azure AD tiers -- free, Premium P1 and Premium P2 -- and provides a list of differences.
After signing up for a plan that meets the company's requirements, the administrator can then subscribe to the licenses using Microsoft 365 E3/E5 or Microsoft open volume licensing for Azure AD Premium P1 or Premium P2.
Purchasing Premium P1 costs $6 per user, per month or $9 per user, per month for the Premium P2 plan. IT decision-makers might opt for the Microsoft 365 package, which includes Azure AD, Office 365 and Windows 10 Enterprise in one bundle.
After completing the subscription, the administrator can navigate to the admin portal and search for Azure Active Directory to use the service.
Azure AD vs. on-prem AD: Is it time to go or stay?
Active Directory in the data center remains a popular setup for many organizations. There are perks to keeping a domain controller within the environment when other organizations that rely on Azure AD cannot get work done due to a Microsoft cloud outage.
But with many of the improvements and redundancies many companies use for connectivity to the cloud, more administrators are considering a switch from on-premises AD and replacing it with managed domain services on Azure. As more companies continue to sign up for cloud services, on-premises AD might fade away as Azure AD takes on a much bigger role.





