identity theft
What is identity theft?
Identity theft, also known as identity fraud, is a crime in which an imposter obtains key pieces of personally identifiable information (PII), such as Social Security or driver's license numbers, to impersonate someone else.
The stolen information can be used to run up debt purchasing credit, goods and services in the name of the victim or to provide the thief with false credentials. In rare cases, an imposter might provide false identification to police, creating a criminal record or leaving outstanding arrest warrants for the person whose identity they stole.
Types of identity theft
The two categories of identity theft are the following:
- True-name identity theft is when the thief uses PII to open new accounts. The thief might open a new credit card account, establish cellular phone service or open a new checking account to obtain blank checks.
- Account-takeover identity theft is when the imposter uses PII to gain access to the person's existing accounts. Typically, the thief changes the mailing address on an account and runs up a bill before the victim realizes there is a problem. The internet has made it easier for identity thieves to use the information they've stolen since online transactions are made without any personal interaction.
Examples of identity theft include the following:
- Financial identity theft. This is the most common type of identity theft. Financial identity theft aims to gain economic benefits by using a stolen identity.
- Tax-related identity theft. In this type of exploit, the criminal files a false tax return, for example, with the Internal Revenue Service (IRS) using a stolen Social Security number.
- Medical identity theft. This involves the thief stealing information, such health insurance member numbers, to receive medical services. The victim's health insurance provider might get fraudulent bills. This is reflected in the victim's account as services they received.
- Criminal identity theft. In this example, a person under arrest gives stolen identity information to the police. If this exploit is successful, the victim is charged instead of the thief.
- Child identity theft. In this exploit, a child's Social Security number is misused to apply for government benefits and open bank accounts or other services. Criminals often use the information of children because the damage might go unnoticed for a long time.
- Senior identity theft. This type of exploit targets people over the age of 60. Senior citizens are often identified as easy theft targets. It is important for seniors to be aware of the evolving methods thieves use to steal information.
- Identity cloning for concealment. In this exploit, a thief impersonates someone else to hide from law enforcement or creditors. Because this isn't always financially motivated, it's hard to track, and there often isn't a paper trail for law enforcement to follow.
- Synthetic identity theft. In this type of exploit, a thief partially or completely fabricates an identity by combining different pieces of PII from different sources. For example, the thief might combine one stolen Social Security number with an unrelated birthdate. This type of theft is usually difficult to track because the activities of the thief are recorded files that do not belong to a real person.
Identity theft techniques
Although an identity thief might hack into a database to obtain PII, experts say it's more likely for thieves to obtain information using social engineering techniques such as the following:
- Mail theft. The thief steals credit card bills and junk mail from a victim's mailbox or from public mailboxes on the street.
- Dumpster diving. Retrieving personal paperwork and discarded mail from dumpsters is an easy way for an identity thief to get information. Recipients of preapproved credit card applications often discard them without shredding them first, which increases the risk of credit card theft.
- Shoulder surfing. This happens when the thief gleans information as the victim fills out personal information on a form, enters a passcode on a keypad or provides a credit card number over the telephone.
- Phishing. This involves using email to trick people into offering up their PII. Phishing emails might contain malicious attachments designed to steal PII or links to fraudulent websites where people are prompted to enter their information.
How to tell if your identity has been stolen
In 2017, major credit bureau Equifax experienced a data breach that exposed 147 million people's data. A settlement of $425 million was agreed upon to help the victims affected. It is still regarded by some as the most significant instance of identity theft in recent history due to the large-scale damages and significance of the breached organization. This breach occurred due to a number of security lapses by Equifax.
Warning signs of identity theft include the following:
- Victims notice withdrawals from their bank account not made by them.
- An impacted credit score.
- Victims don't receive bills or other important mail containing sensitive information.
- Victims find false accounts and charges on their credit report.
- Victims get rejected from a health plan because their medical records reflect a condition they don't have.
- Victims receive an IRS notification that another tax return was filed under their name.
- Victims get notified of a data breach at a company that stores their PII.
Impact and identity theft prevention
In addition to losing money and accruing debt, victims of identity theft can incur severe intangible costs, such as damage to reputation and credit, which can prevent victims from finding a job or getting credit. Depending on the circumstances, identity theft can take years to recover from.
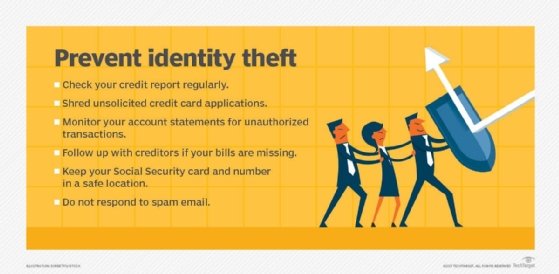
To protect yourself from identity theft, experts recommend individuals regularly check credit reports with major credit bureaus, pay attention to billing cycles and follow up with creditors if bills do not arrive on time.
Additionally, people should do the following:
- Destroy unsolicited credit applications.
- Watch out for unauthorized transactions on account statements.
- Avoid carrying Social Security cards.
- Avoid giving out PII in response to unsolicited emails.
- Shred discarded financial documents.
Many state attorney general websites offer identity theft kits designed to educate people on identity theft prevention and recovery. Some offerings include helpful documents and forms. The Identity Theft Affidavit, for example, is a form to officially file a claim of identity theft with a given business. This form in particular is most often used when new accounts have been opened using a victim's personal data, not when an existing account has been illegally accessed.
If an individual experiences tax-related identity theft, they should continue to pay and file taxes, even if they must file paper returns.
Identity theft recovery
Depending on the type of information stolen, victims should contact the appropriate organization and inform it of the situation. This could be a bank, credit card company, health insurance provider or the IRS. Victims should freeze or close their account to prevent further fraudulent charges, claims or actions.
In the U.S., identity theft victims should file a complaint with the Federal Trade Commission (FTC) and inform one of the three major credit bureaus -- Equifax, Experian or TransUnion -- to have a fraud alert or security freeze placed on their credit records.
Victims can visit the FTC website to obtain a recovery plan and put it into action. The plan includes the collection of forms and letters necessary to guide the victim through the recovery process.
If PII is compromised in a data security breach, victims should follow up with the company responsible about what assistance and protections it has in place for victims and their data.
Identity theft laws and penalties
Governments respond to identity theft crimes differently. In the U.S., two laws largely define the legal proceedings around identity theft: the Identity Theft and Assumption Deterrence Act of 1998 and the Identity Theft Penalty Enhancement Act of 2004.
The Identity Theft and Assumption Deterrence Act prohibits "knowingly transferring or using a means of identification with the intent to commit, aid or abet any unlawful activity that constitutes a violation of federal law or that constitutes a felony under any applicable state or local law."
The Act increased sentence lengths by varying degrees for general and terrorism-related offenses. It also established penalties for aggravated identity theft. Aggravated identity theft refers to the use of another person's identity to commit felonies.
Penalties for identity theft, which vary based on offense, are wide ranging and can be severe. Some penalties for identity theft include the following:
- In certain first-offense scenarios, thieves might be sentenced to probation if they didn't cause significant harm. Those on probation could still be responsible for fines and restitution.
- Being issued felony and misdemeanor charges is the most common consequence for perpetrators.
- The thief could be required to compensate the victim for financial losses, including lost wages, legal fees and potentially emotional distress costs.
- Perpetrators of identity theft in the U.S. often face imprisonment, with the minimum sentence being two years for aggravated identity theft. This penalty increases with case severity.
Identity theft insurance
Identity theft insurance can help victims expediate slow and costly recovery processes. It usually only covers recovery costs, however, not the damages caused directly by the theft. Depending on the policy, expenses covered could include the following:
- Lost wages.
- Childcare costs.
- Credit monitoring services.
- Legal fees.
- Copies of credit reports.
Identity theft insurance is available as an endorsement to homeowners or renters insurance policies or as a standalone policy. It often has deductibles of $100 to $500. It also usually has benefit limits of $10,000 to $15,000. Damages that exceed the limit are not fully covered, and the victim must pay the difference.
Victims seeking an alternative to insurance or help beyond insurance can use identity theft protection services. These services sometimes provide reimbursement of stolen funds, restoration services and credit monitoring services.
Ben Lutkevich is a writer for WhatIs, where he writes definitions and features.








