How do cybercriminals steal credit card information?
Cybercriminals have various methods at their disposal to hack and exploit credit card information. Learn what they are, how to prevent them and what to do when hacked.
Cybersecurity has never been more critical given the exponential growth of e-commerce and online transactions. Hackers may attempt to invade our privacy in several ways, but one area they find particularly enticing is credit card information. Stolen credit cards can negatively affect not just your finances but your personal identity and privacy, too. Protecting them and the data connected to them is essential in the online world.
In this article, we delve into how cybercriminals can steal your credit card information, highlight best practices to keep you safe and explain what to do if your credit or debit card is compromised.
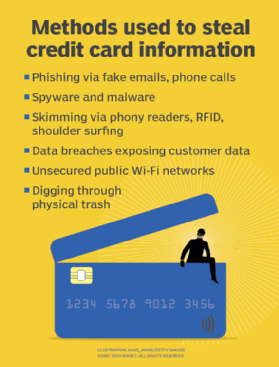
7 common ways credit card information is stolen
Hackers can steal credit and debit card information in a variety of ways, using both online and offline methods.
1. Phishing
Can a website steal your credit card information? The short answer is yes.
With phishing, hackers attempt to steal valuable information by impersonating a trusted source. Several phishing schemes include fake phone calls, fake websites and fake sales emails. According to an article by Forbes, there were 300,497 phishing victims, with a total loss of $52,089,159 in the U.S. reported in 2022.
For example, someone pretending to be from your issuing bank or credit card company calls and says they need to verify your recent credit card activity with some personal information and asks for your credit card number. Similarly, a phishing email sent by an attacker posing as a retailer that offers you a discount or free items could be trying to trick you into giving up payment card account details.
Common phishing attempts are relatively easy to spot because they demonstrate characteristics that legitimate messages do not: fear, urgency, poor message composition and demands that deviate from normally accepted business behaviors.
In 2024 and 2025, a rash of text messages targeted phone users across New England, purporting to be from toll management firm E-ZPass, demanding immediate payment for unpaid tolls. The texts originated from an unknown number – sometimes outside the country -- did not refer to the recipient by name, did not include any actual toll amount, and demanded payment within 12 hours by clicking on a vanilla URL. E-ZPass never sends payment notices via text. This combination of factors made the scam easy to spot.
However, scammers are upping the ante by implementing machine learning and AI tools to build more realistic messaging and send those messages in a more targeted manner. Users must always be vigilant and double-check account status or payment data directly with the actual provider.
How to prevent: The best way to prevent phishing scams -- whether via email, phone or text -- is to never give up any personal or credit card information unless you initiated the contact. Also, go directly to a retailer's website to conduct business to ensure you control all transactions.
2. Malware and spyware
Be careful what you download. Accidentally downloading malware or spyware can enable hackers to access information stored on your computer, including credit card information and other details. For example, a malware attack might use a keylogger that records your keystrokes or browser history and then sends that information to a hacker.
It's important to remember that not just client-side software and devices can be compromised by malicious code. Server-side systems can also be infected in otherwise legitimate businesses, compromising your data and that of countless other customers. For example, formjacking is an attack that injects malicious JavaScript code into a website's forms to steal sensitive user data -- such as credit card information -- that is entered during the regular checkout process.
How to prevent: Avoid downloading attachments, unless they come from a trusted source, and be wary of the programs you download and install on any of your devices. Also, use antivirus software that catches malware before it infects your computer. If you're concerned about server-side risks such as formjacking, enter only the minimum amount of information needed to complete the transaction.
3. Skimming
Credit card skimming is a popular offline method that criminals use to steal personal information at a point of sale, which can also lead to identity theft. Considering that skimming requires the installation of physical devices -- skimmers -- the practice tends to occur in more remote locations with less monitoring and lower human presence. The following are three forms of skimming to be aware of:
Card readers at ATMs, gas pumps and other locations can be tampered with to add skimming devices. These phony readers collect and pass on payment information to thieves, who clone the cards and use them as they see fit.
How to prevent: Inspect outdoor credit card readers for signs they may have been tampered with before using them.
RFID skimming uses radio frequency identification technology to wirelessly intercept credit, debit and ID information directly from RFID-enabled cards -- sometimes even smartphones and tablets. Attackers use devices that support near-field communication to record unencrypted data from the card's RFID chip to steal details such as card numbers, expiration dates and cardholder names.
How to prevent: Make sure your financial institution has adequate safeguards in place, including encryption. Shielded -- anti-RFID -- card holders such as wallets and purses can also be helpful.
4. Shoulder surfing
Shoulder surfing is a simple form of skimming that doesn't involve specialized technology. A thief simply watches a user enter their code into an ATM or credit card information into a phone. Shoulder surfing can be done nearby or far away, e.g., through binoculars.
How to prevent: Shield keypads with paperwork, your body or by cupping your hand. Be aware of your surroundings and be cautious of open areas that allow casual personal or social interactions -- such as coffee shops -- where strangers can see your computer or other electronic devices where data might be entered. Do not leave your smart device unattended and close laptops or lock tablets if they must be left unattended for any time.
5. Data breaches
Unfortunately, high-profile data breaches have become fairly common in recent years. With the amount of data stored online, hackers have another avenue to steal credit card, financial and other personal information. According to Verizon's 2024 Data Breach Investigations Report, social engineering -- such as phishing texts and emails -- captured personal data and credentials in more than 50% of 3,032 breaches, with confirmed data disclosure that occurred from November 2022 through October 2023.
How to prevent: One way to mitigate the possibility of becoming a data breach victim is to use a virtual credit card -- such as Google Wallet – or a third-party payment mechanism -- such as PayPal -- to check out at e-commerce stores without including your credit card information. If you become a victim, steps you should take include freezing your credit, placing a fraud alert on it and replacing the card affected by the breach. Also, obtain a copy of your credit report and be vigilant about suspicious credit card activity.
6. Public Wi-Fi networks
Unsecured public Wi-Fi networks carry some danger if you enter sensitive information when connected to them. While airport or hotel Wi-Fi can be convenient, precautions should be taken to protect against losing credit card data and other sensitive information. Furthermore, be cautious of Wi-Fi designations or labels. Should a "Free Public Wi-Fi" entry appear on your device, it might be a hacker on a nearby smartphone or laptop attempting to get unsuspecting users to sign on to steal their personal information.
How to prevent: Don't conduct sensitive business while connected to public networks. If you need to access these networks, use a VPN. Otherwise, stick to trusted and authenticated access points and service set identifiers or use your wireless cellular data connection.
7. Your trash
While it may seem old-fashioned, criminals can dig through your garbage to find credit card statements, account information and more that they can use to their advantage. In addition, there has been a dramatic rise in the theft of mail from carriers and mailboxes to obtain printed account statements.
How to prevent: Opt to receive credit card statements via email. If you receive paper statements in any form, shred them after you no longer need them.
What to do if your credit card information is stolen
Following the best practices in this article will help keep your credit card information away from danger. But nothing is foolproof, and you must act if your information is stolen.
Here's what you should do.
1. Contact your credit card issuer
Call your bank or credit card company if you suspect your card has been stolen or compromised. This can prevent further damage and help you avoid liability for fraudulent purchases. Your credit card issuer will cancel your card and issue a new one.
2. Update your passwords
Between data breaches, malware and public Wi-Fi networks, hackers can use several online methods to steal your credit card and personal information. Updating your passwords on any websites you regularly visit can prevent hackers from accessing this data.
3. Review and dispute credit reports
Even after you cancel your compromised credit card and get a new one, some fraudulent transactions you're unaware of could appear on your statements. Continue to monitor them so you can dispute any transactions that look suspicious. Credit reporting agencies such as Experian let people place temporary credit locks or fraud alerts on their credit files. These mechanisms can prevent access to credit reports, preventing credit inquiries and new credit-based accounts from being opened without further investigation by the credit-issuing business.
Why are you at risk of repeat credit card fraud?
Although many incidents of credit card fraud are single instances -- at least before fraudulent activity is detected and addressed -- repeat credit card fraud occurs when multiple fraudulent charges on the same or different credit cards victimize a person. There are several common classifications of repeat credit card fraud, including the following:
- Recurring fraud. This occurs when unauthorized use occurs on the same card several times. For example, a stolen card is used in a spending spree where numerous purchases are made at different locations using the same compromised card.
- Multi-card fraud occurs when unauthorized use occurs on two or more cards. For example, a wallet or purse with multiple cards is stolen, or a data breach involves multiple payment alternatives.
The frequency and severity of repeat credit card fraud depend mainly on the actions taken by the victim in the aftermath of the fraud incident. The longer it takes for a victim to act, the higher the likelihood that their credit cards will be used repeatedly. A failure to act makes you more susceptible to repeat credit card fraud. Fortunately, several simple actions can help prevent repeat credit card fraud or mitigate its effects, including the following:
- Set and watch for alerts. The best protection against repeat credit card fraud is timely information and decisive action by the victim. Modern technologies provide real-time account activity alerts that can be sent to users using emails and texts. Alerts can be quickly and easily configured through card provider websites. Take the time to set up alerts before card theft or fraud occurs. Users can be alerted to fraudulent transactions in real time when incidents happen. In some cases, victimized cardholders can block or dispute the transaction immediately.
- Lock cards that might have been compromised. Most credit cards now provide a lock feature to disable the card through the card provider's website or mobile app. If cards go missing or transaction alerts suggest malicious activity, lock the affected cards immediately and contact the card provider with more details. The provider can permanently disable a compromised card and immediately issue a replacement.
While these first two steps provide some immediate assistance, there are additional steps that can be taken later after fraud occurs, including the following:
- Review credit card accounts regularly. Whether received using mail or email, take the time to review credit card -- and all financial -- statements and look for signs of suspicious activity. Older generations used regular tactics such as "balancing the checkbook" to reconcile money spent with checks written to ensure that balances were correct and no money was missing or mis-spent.
- Contact law enforcement. Although law enforcement agencies might be unable to mitigate the effects of repeat credit card fraud, filing reports with them can help raise their awareness of malicious activity and allow for better enforcement moving forward. For example, reporting a stolen wallet or purse can tip off law enforcement to growing criminal activity in the area. Similarly, reporting data breaches or electronic theft to bodies such as the Federal Trade Commission can trigger closer scrutiny of businesses with weak security or noncompliant data protection postures.
- Use credit monitoring services. Numerous credit monitoring services are available through credit reporting agencies or third-party monitoring. These services can monitor credit reports and scores and alert users to changes in credit reports, such as new accounts or lines of credit -- all of which can point to suspicious activity and possible fraud.
Best practices to protect credit card data
Cybercriminals can use various methods to obtain your credit card. Some tips to prevent this include the following.
1. Monitor credit reports
Credit monitoring and identity security services -- such as LifeLock and CreditLock -- keep you updated on your credit card activity. They can also help get you ahead of any fraudulent activity faster than if you manually checked your statements.
2. Monitor bank accounts and review credit card statements for suspicious activity
Checking credit statements manually and monitoring Equifax, Experian or TransUnion for purchases you don't remember making can alert you to strange transactions and suspicious activity.
3. Set up alerts to notify of suspicious activity
Alerts from your bank via text, push notifications and email can help you identify suspicious transactions soon after they happen.
4. Use antivirus software and VPNs
If you're connecting to public networks, use a VPN to protect yourself from malware and hackers. Not to mention, antivirus software can protect you if you accidentally download harmful malware.
5. Check websites for a secure URL
When visiting any website -- but especially when conducting online transactions -- ensure the URL includes https:// and is designated as secure.
6. Don't save credit card information on websites
It can be tempting to save your credit card information on Google or at e-commerce sites you frequent. However, you should avoid this practice, as it potentially provides hackers access to your personal information in the case of a data breach. If you have saved such information previously, it's simple to revisit those sites and remove payment data from your account.
7. Use strong passwords and multifactor authentication
Another way to avoid being the victim of a data breach is to use strong passwords that contain a mix of letters, numbers and symbols. In addition, multifactor authentication -- such as receiving a six-digit code to your smartphone that can be entered into a website for validation -- can provide an added layer of security to protect you. Consider using it when offered. The same goes for newer passwordless authentication methods based on biometrics -- such as facial recognition or fingerprints -- or the FIDO protocols. Also, changing those strong passwords regularly is a routine security habit.
8. Don't write down your credit card information anywhere
Finally, avoid writing your credit card number, PIN and expiration date anywhere or posting pictures of your card number online.
Credit cards are a common target for cybercriminals, and that will not change anytime soon, if ever. Awareness of the methods they use to steal personal information -- credit card data, in particular, but other details that can lead to fraudulent transactions, identity theft and more -- is the first step toward protecting yourself. Implement the best practices in this article to keep your credit card information safe and take a more active role in preventing yourself from becoming a victim of fraud.








