What is an attack vector?
An attack vector is a path or means by which an attacker or hacker can gain access to a computer or network server to deliver a payload or malicious outcome. Attack vectors enable hackers to exploit system vulnerabilities, including the human element.
Common cyberattack vectors include viruses, malware, email attachments, webpages, pop-up windows, instant messages, chat rooms and deception. Except for deception, all these methods involve programming or, in a few cases, hardware. Deception is when a human operator is fooled into removing or weakening system defenses.
Firewalls and antivirus software can block attack vectors to some extent. But no protection method is totally attack-proof. A defense method can quickly become obsolete, as hackers constantly update attack vectors and seek new ones to gain unauthorized access to computers and servers.
The most common malicious payloads are viruses -- which can function as their own attack vectors -- as well as Trojan horses, worms and spyware. Third-party vendors and service providers can also be considered attack vectors, as they can pose a risk to an organization if they have access to its sensitive data.
How do cyberattackers exploit attack vectors?
Hackers have in-depth knowledge of the common security attack vectors available to them. When determining how to hack one of these security vectors, they first seek out vulnerabilities, or security holes, that they think they can penetrate.
A security hole can be found in software or a computer operating system (OS). Sometimes, a security vulnerability can open up because of a programming error in an application or a faulty security configuration. Hacks can even be low-tech, such as obtaining an employee's security credentials or breaking into a building.
Hackers constantly scan companies and individuals to identify all potential entry points into systems, applications and networks. In some cases, they might even target physical facilities, or find vulnerable users and internal employees who will knowingly or inadvertently share their IT access credentials.
What is the difference between an attack vector and an attack surface?
These terms are often used interchangeably, but they aren't the same. An attack vector differs from an attack surface, as the vector is how an intruder gains access, while the attack surface is what's being attacked.
What is the difference between passive vs. active attack vector exploits?
It's also essential to distinguish between passive and active attack vector exploits. While most attack vectors have a great deal in common -- including a target, gathering information about the target and using that information to access the target system -- they also differ. A passive attack vector exploit involves the attacker gathering information without actively exploiting the system's vulnerability. In an active attack vector exploit, the attacker exploits the vulnerability to gain access to the system.
In a passive attack vector exploit, the access attempt doesn't affect system resources. Phishing attacks, typosquatting and other social engineering attacks involving human beings fall into this category.
In an active attack vector exploit, the system hosting the target is altered, and its performance or operation is usually affected. Examples of active attacks include malware, ransomware, domain hijacking and man-in-the-middle (MitM) attacks.
One of the most publicized hacks was the SolarWinds supply chain attack. During its investigation to determine the attack vectors, SolarWinds found that the breach likely resulted from compromised credentials that enabled access to the development environment for SolarWinds' Orion IT management software.
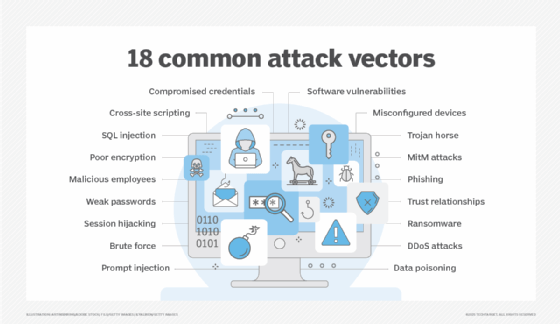
16 of the most common attack vectors
Intruders are continuously seeking out new attack vectors. The most common attack vectors include the following:
- Software vulnerabilities. If a network, OS, computer system or application has an unpatched security vulnerability, an attacker can use a threat vector, such as malware, to gain unauthorized access.
- Compromised user credentials. Users can knowingly or inadvertently share their user IDs and passwords. This can be done verbally, but cyberattackers can also gain access to credentials through a brute-force attack that tries different combinations of user IDs and passwords until an authorized set of credentials is uncovered. The hacker then uses these credentials to hack a network, system or application.
- Weak passwords and credentials. In brute-force attacks, cyberattackers focus on hacking user IDs and passwords that are weak or can be easily guessed. But hackers also steal credentials by using programs that monitor public Wi-Fi networks for when users input their access credentials. For example, a hacker could install keylogging software on a user's workstation through an infected website or email. The keylogging program logs user keyboard activity, including when the user enters their ID and password. Hackers can also gain access by enticing users to open unsolicited email attachments that contain malicious links to bogus websites that convince them to surrender personally identifiable information.
- Malicious employees. Malicious or disgruntled employees can hack into networks and systems using their security clearances to extract sensitive information, such as customer lists and intellectual property, that they either demand ransom for or sell to others for nefarious purposes.
- Poor or missing encryption. In some cases, employees -- or IT staff -- might forget to encrypt sensitive information stored on laptops and smartphones out in the field. In other cases, encryption techniques have known design flaws or only use limited keys to encrypt and protect data.
- Ransomware. This type of malware locks the data on the victim's computer, and the attacker either threatens to publish the victim's data or blocks access to it unless a ransom is paid. Ransomware can lock a user's files, often demanding a cash sum from the user to unlock the files. Most ransomware is inadvertently downloaded onto a computer or network by a user.
- Phishing. Phishing is the deceptive practice of sending emails in which the attacker purports to be from a reputable company to lure individuals into revealing personal information, such as passwords or credit card numbers. Spear phishing is a highly targeted attack that focuses on a single recipient, seeking unauthorized access to sensitive company information.
- Misconfigured devices. Companies can misconfigure their software and hardware security, which leaves them vulnerable to hackers. Vendor security presets on equipment are lax, and if IT staff doesn't reconfigure this equipment before installing it on networks, security hacks can occur. In other cases, companies purchase equipment and forget to configure security fully.
- Trust relationships. Companies often entrust their security to outside system and network vendors, cloud providers, and business partners. When hackers breach the systems of these third parties, the information they obtain can also contain sensitive information from the companies these providers service.
- Distributed denial-of-service attacks. DDoS attacks flood victims with bogus emails, rendering their systems or networks unusable and services unavailable to their intended recipients. These attacks often target the web servers of finance, commerce and government organizations, and are often used to distract an organization from other network attacks.
- SQL injection attacks. This attack leverages the Structured Query Language used to query most databases -- where most target data coveted by threat actors resides. In such an attack, malicious SQL code is slipped into a server query or management procedure to extract sensitive data.
- Session hijacking. This attack exploits the session keys and cookies generated when someone logs in to a service. By hijacking the key or cookie, an attacker can use it to access the service.
- Cross-site scripting. Also known as an XSS attack, cross-site scripting injects malicious code into a website, but targets the site's visitors, not its resources. For instance, a cross-site scripting attack might drop malicious JavaScript code into a blog post comment.
- MitM attacks. The ubiquity of public Wi-Fi networks has spawned new forms of attack, one of which is the interception of traffic in a public network intended to go elsewhere. This enables attackers to steal sensitive or confidential information.
- Brute force. This refers to cybercriminals' ongoing efforts to gain access to a system or network through sheer trial and error -- trying one thing, then another, using various types of attack vectors, from phishing attacks to password and encryption hacks to hijacking, until an attempt finally succeeds.
- Trojan horse. A Trojan horse is a specific kind of malware that fools the user into thinking it is legitimate software. Trojan horse malware is often spread through email attachments, which is one reason never to download any attachment that doesn't appear to be legitimate or that comes from an unknown source.
How to protect devices against common vector attacks
Attackers use a variety of techniques to penetrate corporate IT assets. As these techniques continue to evolve, the IT team's job is to identify and implement the policies, tools and techniques that are most effective in protecting against these attacks. The following is a list of effective protection techniques:
- Implement effective password policies. Ensure usernames and passwords meet proper length and strength criteria, and that the same credentials aren't used to access multiple applications and systems. Using two-factor authentication or verification methods, such as a password and a personal identification number, can provide an added layer of protection for system access.
- Install security monitoring and reporting software. This includes software that monitors, identifies, alerts and even locks down entry points to networks, systems, workstations and edge technology once it has detected a potential attack by an unidentified or unauthorized user or source.
- Regularly audit and test IT resources for vulnerabilities. At a minimum, IT vulnerability testing should be conducted quarterly, and an outside IT security audit firm should test IT resources for vulnerability annually. Based on these findings, security policies, practices and prevention techniques should be updated immediately.
- Keep IT security front and center. Security investments cost money, and a chief information officer and a chief security officer need the chief executive officer and the board of directors to approve these purchases. This requires regular briefings and education for C-level executives so that they understand the importance of securing IT, and the ramifications for the company and its reputation if IT is left unsecured.
- Train users. All new employees should receive comprehensive training in IT security policies and practices, and existing employees should receive refresher training annually. IT personnel, especially in the security area, should be current on the latest security policies and practices.
- Collaborate with human resources. Social engineering vulnerability audits should be performed with an outside security audit firm at least once every two to three years. If there's suspicious employee activity, IT should immediately alert HR so that it can take appropriate action, whether it's meeting with an employee, restricting an employee's access, coaching an employee or firing an employee.
- Immediately install all updates. Whenever a hardware, firmware or software update is issued, IT staff should promptly install it. If devices are used in the field, the security updates should be provided as push notifications, where software or firmware is automatically updated.
- Use thin clients for companies with a bring-your-own-device policy. It's preferable to house all corporate data in a secure cloud or other enterprise system so that users can sign in from home or their own devices through a virtual private network, which is restricted to a specific set of users and isn't open to the public. This prevents sensitive data from being stored on remote devices.
- Use strong data encryption on portable devices. Whether a portable device is a laptop, a smartphone, a sensor or any other edge device, data encryption should be used wherever sensitive data is stored. This can be done by selecting a strong data encryption technology, such as the Advanced Encryption Standard. The U.S. government uses AES, which contains 128-, 192- and 256-bit keys for data encryption.
- Review and set all security configurations. This includes OSes, internet browsers, security software, network hubs and edge devices, such as sensors, smartphones and routers. Often, systems, browsers, hubs and internet of things devices come with minimal default security settings, and companies forget to adjust these settings. As a standard practice, companies should check and, if necessary, reset security on all new IT.
- Secure physical spaces. While most data breaches and security hacks target IT, physical access intrusions can also occur. Data centers, servers located in different departments and remote field offices, medical equipment, field-based sensors, and even physical file cabinets in offices are all hacking targets. They should be secured, protected and regularly inspected.
Cloud DDoS attacks are just one of the many threats that can lead to business losses. Learn what defenses and protections cloud service providers are providing to combat these threats.







