
markrubens - Fotolia
What's the difference between an edge router vs. core router?
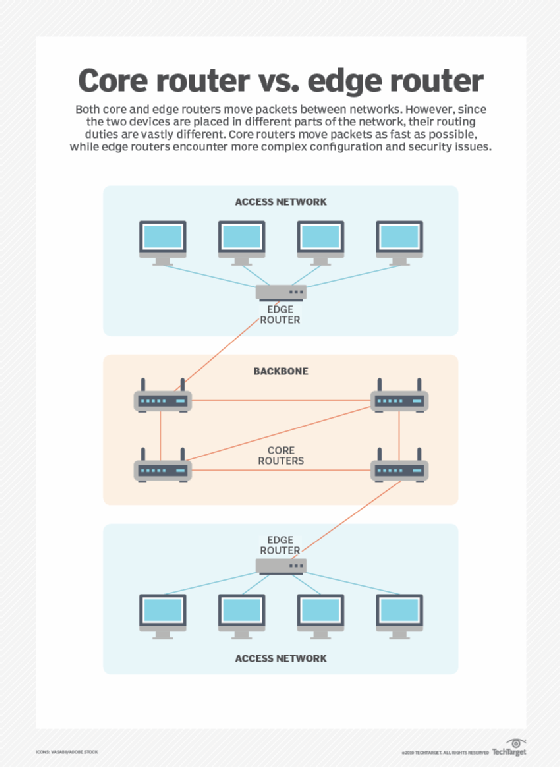
Clearly, an edge router and core router are placed in different parts of the network, but their routing roles are more complex than their physical locations.
Despite their shared primary goal of moving packets between networks, core and edge routers serve dramatically different purposes. The first difference when comparing an edge router vs. core router is the placement of the routers within an enterprise network.
A traditional LAN architecture has three distinct and logical tiers: core, distribution and access. The access tier connects end devices, such as PCs, laptops, smartphones and IoT devices. The distribution tier handles virtual LAN and subnet creation, access controls and most of the routing functions. The core tier -- where core routers reside -- is designed to serve one purpose: route packets as fast as possible.
When deploying a core router, you won't encounter many configuration complexities. For instance, in a core router, you won't find any access control, route or packet filtering, or route redistribution configurations. These functions require increased memory and CPU resources -- things that affect packet flow speed.
Edge router vs. core router -- internet traffic a key differentiator
An edge router is the last internally managed routing device that separates one autonomous network from another. The most common example of an edge router within an enterprise is the router that connects the corporate LAN to the internet. Edge routers can also be used when connecting your corporate LAN to a third party, such as a partner or customer network. You'd place an edge router at the boundary where the two networks connect.
From a routing perspective, edge routers are commonly configured using static routes as opposed to dynamically peering and learning routes from the foreign network. The reason for this is because you should largely not trust anything on the other side of the boundary to make routing decisions for you. Otherwise, you may end up with an outage that is outside your control.
One major caveat to this, however, is when your enterprise network requires bidirectional internet service redundancy from two or more internet service providers (ISPs). In this situation, enterprise customer edge routers connect to ISP edge routers using the Border Gateway Protocol (BGP), a dynamic routing protocol that controls routes on the internet.
Thus, if you need full bidirectional redundancy on your corporate network, there must be a level of trust that your ISP is going to handle dynamic BGP routing appropriately as to not cause your end users unintentional internet outages.
Edge router vs. core router and security controls
Beyond routing, edge routers commonly incorporate strict access controls and route filters configured to protect the trusted internal network from the external one. These rules provide catch-all protection for the network in the event other security appliances, such as network firewalls, miss something they should have blocked.
Access controls are also used to protect these security devices from being bombarded with fraudulent traffic. An example of this is the use of internet edge routers to filter and block traffic sourced from Bogon and Martian networks from ever reaching a corporate firewall.








