trunk (trunking)
What is trunk and what is trunking in networking?
A network trunk is a communications line or link designed to carry multiple signals simultaneously to provide network access between two points. Trunks typically connect switching centers in a communications system. The signals can convey any type of communications data.
A networking trunk can consist of several wires, cables or fiber optic strands bundled together in a single physical cable to maximize the available bandwidth. Or it can consist of a single high-capacity link over which many signals are multiplexed.
Types of network trunking
There are several ways to use trunking in networking, including in broadcasting, phone systems and data networks.
Trunking in telephone systems
The term trunking in networking dates from the days of analog phone systems. With those systems, many landline users shared a few communication paths extending from a main trunk line, like the branches of a tree.
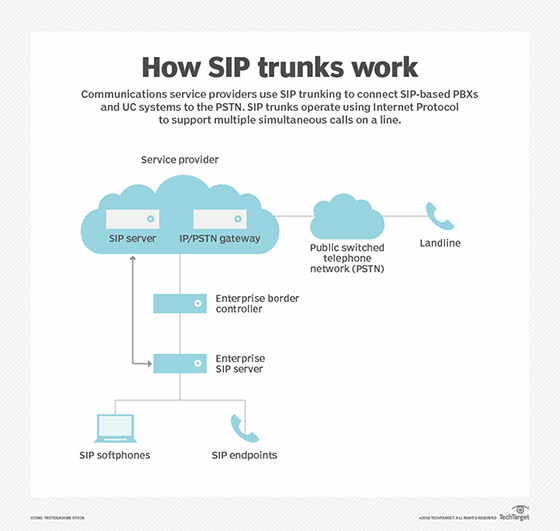
Today, trunks interconnect switching network nodes, such as private branch exchanges (PBXs) and central offices. Session Initiation Protocol (SIP) trunk links enable voice over Internet Protocol (VoIP) to connect a PBX to the internet. In enterprise telephony, the transition from traditional time-division multiplexing trunks to SIP trunks began around 2009.
VoIP, also known as IP trunking, is a technology that converts human speech to data for digital transmission via the internet. By contrast, analog telephone lines send electrical signals across cables to convey changes in voice.
A SIP trunk is a virtualized instance of analog telephone lines. It connects an unlimited number of channels to a PBX system for long-distance and international calling over the internet. The SIP trunk router must be set to quality of service to ensure voice traffic takes priority over data-intensive activities, such as downloading or content streaming.
Trunking in broadcasting
A trunk can also consist of a cluster of broadcast frequencies, as in a trunked radio system that enables the sharing of a few radio frequency channels among a large group of users. Trunked radio systems were developed in the 1990s. They provide more efficient use of the radio spectrum. Rather than assigning a frequency to one group, users are placed in logical groups. All the frequencies are pooled, and computers automatically allocate broadcast channels as users request them. Repeaters retransmit signals and extend the coverage to a wider area.
Computerized data networks
Data networks use the following two types of trunks:
- trunks that carry data from multiple local area networks or virtual local area networks (VLANs) across a single interconnect between network switches or routers, called a trunk port.
- trunks that bond or aggregate multiple physical links to create a single, higher-capacity, more reliable logical link, which is called port trunking.
Trunking and VLAN configuration
Trunking is a key architectural component of VLANs. In VLANS, a physical network is virtualized to create several logical networks that are independent broadcast domains. The main physical communications link is the trunk; switches connected to the trunk provide the branches out to support many client devices.
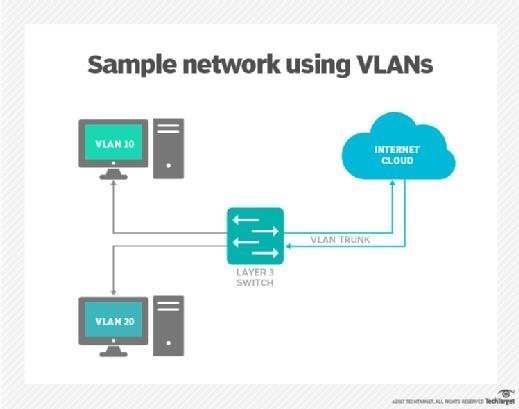
VLANs were an improvement over shared network hubs. A VLAN groups client devices that frequently communicate with one another. On busy networks, this reduces broadcast traffic congestion. It also segments data as it goes through the switches. Trunk links pass packets of data from each of the VLANs. This connects switches together so that each port can be independently configured to a dedicated VLAN.
Trunk ports vs. access ports
An Ethernet interface can be configured as an access port or a trunk port by switching the port's mode setting:
- Access port. In the switch port mode access setting, a port provides a dedicated link to servers, routers or terminals within a single VLAN. Access ports convey only the data traffic that matches the access value of its pre-assigned VLAN. When configured as an access port, the switch connects to a network host. The host presumes the arriving data frames to be part of that VLAN. A common use case for access ports is to connect a personal computer or peripheral device to a switch.
- Trunk ports. In switch port mode trunk setting, a port will concurrently carry traffic between several VLAN switches on the same physical link. A trunk port adds special identifying tags to isolate traffic on the different switches. IEEE (Institute of Electrical and Electronics Engineers) open standard 802.1Q describes the vendor-agnostic encapsulation protocol for VLAN tagging. A tag gets placed on Ethernet frames as they pass between switches. This ensures each frame is routed to its intended VLAN at the other end of the trunked link. A trunk port is commonly used for connecting two switches, connecting switches to servers and routers, and connecting hypervisors to switches.
Trunking to extend VLAN access
Using port trunking extends VLAN access across an entire network. This practice is also known as link aggregation. Numerous Ethernet links are bunched together to behave as a single, logical link. The method to aggregate links is defined by IEEE standard 802.1aq and by the 802.1AX standard for LANs and metropolitan area networks, as well by various vendor-proprietary methods. The trunking function must be activated via parallel commands on both the sending and receiving ends.
Before open standards, adding VLAN tags required the use of switch makers' proprietary protocols developed. Cisco's VLAN tagging protocol, known as Inter-Switch Link (ISL), encapsulates frames in a header and trailer. ISL only works with Cisco switches. Not all switches support ISL, and Cisco has since deprecated ISL in favor of newer switches that also support the IEEE tagging protocol.
Trunking in networking differs from trunking in software development. In software, a trunk refers to the primary branch of code that developers use to iterate and make version changes. Code changes are made to the trunk, rather than secondary branches of the code, a process that enables new features to be added and deployed more rapidly.
Learn more about the benefits of SIP trunking for cloud migration. If you're interested in other networking topics, check out our guide to unified communications as a service.






