
Petya Petrova - Fotolia
Top 5 VPN myths and misconceptions for IT organizations
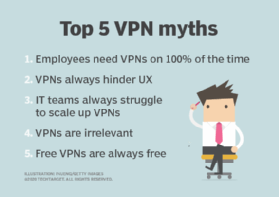
Although VPN technology has its challenges, various misconceptions exist that can muddle IT teams' understandings of VPNs. Here are five common VPN misconceptions debunked.
VPNs are a central part of remote work strategies, so information on the topic abounds. However, this bevy of information may sometimes lead readers to myriad VPN myths and misconceptions as they research.
Common VPN myths include the belief that VPNs consistently hinder UX, they must always remain on and they are irrelevant. While readers may derive some truth from these points, they are not definitively true, according to Joel Windels, chief marketing officer at NetMotion Software, a mobile software provider based in Seattle. The distinction between VPN myths and facts has become increasingly crucial as more companies turn to remote work strategies for business operations.
"If you have remote workers handling sensitive data, you need some kind of VPN," Windels said. "If you are [in] retail … it's probably not urgent until you're a little bit bigger, but if you're in the financial industry or you're in a law firm, you absolutely cannot compromise when it comes to this kind of thing."
The top 5 VPN myths, debunked
Below are five common VPN myths IT teams should remain aware of as they evaluate VPN technology as a staple of their remote work plans.
1. Employees need their VPNs on 100% of the time
VPNs were invented to encrypt data traffic, especially internet traffic. Yet, many current websites inherently encrypt data traffic, which can make VPNs seem superfluous, Windels said. Still, organizations may encourage employees to keep VPNs on throughout entire workdays to monitor employee performance, ensure highly sensitive data remains protected or in case an employee encounters an untrustworthy network or website.
Some organizations may choose to enable policies that automatically turn on VPNs when employees require the service and turn it off when it isn't necessary -- if the organizations don't want to tunnel all employee data.
"The more intelligent way companies are trying to adopt now is setting up rules or, at least, allowing a policy engine to say, 'Office 365 is kind of secure, but it's handling such sensitive data, so make sure the VPN automatically comes on,'" Windels said. "But, if someone's just browsing Facebook, what's the worst that could happen? We don't need the VPN to be on right there."
2. VPNs always hinder UX
This misconception stems from how legacy VPNs work. Typically, a legacy VPN tunnels traffic from an employee's authorized VPN client to the physical VPN hardware at a company headquarters. These legacy VPNs often incite complaints about slow speeds and high latency, which can hinder employee UX, according to Paul Kirvan, an independent IT consultant.
 Joel Windels
Joel Windels
However, modern VPNs, which are typically software- or cloud-based, are less physically restrictive. IT teams can install, deploy and upgrade modern VPNs from anywhere, including remotely. The enhanced speeds and lower latency make modern VPNs more appealing and improve UX or maintain the same level of UX employees would have on premises, Windels said.
"The neat thing about that is the traffic can go wherever you want it to. If an employee is in the U.K., then you don't have to send all your traffic back to the U.S. and then to the internet again," he said.
3. IT teams always face difficulty as they scale up VPNs
Like UX hindrances, the VPN scaling misconception also stems from legacy VPNs. Legacy VPNs -- typically hardware -- are difficult to scale up because they use physical appliances, which make scaling up more time-consuming. Software- or cloud-based VPNs simplify this, Windels said, because IT teams can deploy and scale up a VPN through a cloud environment within hours, whereas legacy VPNs require a vendor to ship new hardware to the business, which could take days to weeks.
Despite their efficiencies, modern VPNs have challenges as well. If an organization decides to use a cloud-based VPN to easily scale the service up to increasing amounts of remote workers, then IT teams may lose some control over employee performance monitoring or spend money on large amounts of bandwidth the organization doesn't necessarily need.
"You can end up in a situation where you're tunneling a lot of traffic through a VPN in the cloud that possibly doesn't even need to be tunneled. It's in [the vendor's] interest to make sure you're using as much network capacity as you can," Windels said.
4. VPNs are out -- software-defined perimeter (SDP) is in
Before the COVID-19 pandemic, many experts touted the VPN's demise and claimed the time had come for zero-trust networks and SDPs to rule remote access strategies. During COVID-19, the increasing demand for remote network connectivity proved VPNs aren't going anywhere -- at least, not for a while.
Though the concept of SDP is still in its infancy, Windels predicted SDPs will replace VPNs in the next 10 years, as SDPs are the next step in the VPN evolution. Yet, as the SDP concept remains nascent, IT teams may decide to pair SDP and VPN technologies to start, according to Kirvan.
"[SDPs] can function in a stand-alone capacity and also enhance and perhaps supplement security provisions in existing VPNs from firewalls, intrusion detection/prevention systems and other perimeter security solutions," Kirvan said. He added this would only be necessary if the organization could afford it or if business operations required both technologies.
5. Free VPNs are free
The concept of free VPNs can be tricky. Cost-wise, free VPNs are free, may be useful for SMBs to save money in IT budgets and suffice if they don't introduce any risks to the business, Kirvan said. However, it's unlikely free VPNs are completely free of cost, as well as completely free from risk, a point with which Windels agreed.
"If their business model is to not make money out of you, then it's to make money out your data, and effectively, that's what you're giving up when you use one of these free VPN providers," Windels said.
VPN providers can see all traffic that the organization tunnels through their service, so vendors that provide free VPN services can take employee data and sell it to make their profit. Therefore, an organization should prioritize VPNs in its IT budget to ensure remote access for employees and ensure company data is efficiently protected.








