Sender Policy Framework (SPF)
What is Sender Policy Framework (SPF)?
Sender Policy Framework (SPF) is a protocol designed to restrict who can use an organization's domain as the source of an email message. SPF blocks spammers and other attackers from sending email that appears to be from a legitimate organization. SMTP (Simple Mail Transfer Protocol) does not place any restrictions on the source address for emails, so SPF defines a process for the domain owners to identify which IP addresses are authorized to forward email for their domains.
The SPF protocol was published in 2014 by the Internet Engineering Task Force (IETF) in RFC 7208, "Sender Policy Framework (SPF) for Authorizing Use of Domains in Email, Version 1." SPF is an IETF Proposed Standard specification.
How does Sender Policy Framework protect against spoofing and spam?
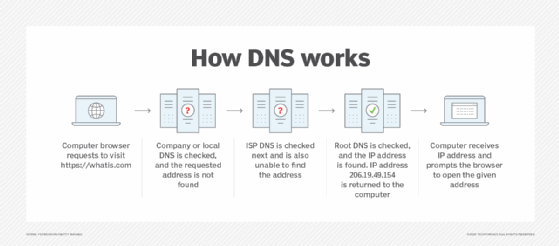
SPF defines a format for adding a record in the Domain Name System (DNS) that indicates valid email servers. Receiving email servers that get email from an email service under SPF must check the TXT records when they perform DNS lookup on the inbound email.
The SPF policy framework is an authentication scheme and a machine-readable language. Each participating domain declares attributes that uniquely describe their mail, including authorized senders. This description is represented in an SPF record, which is published in DNS records. An SPF client program performs a query searching for the correct SPF record, in order to determine whether a message comes from an authorized source.
There are seven possible query results, including pass, which means that the message meets the domain's definition for legitimate messages; fail, which means that a message does not meet that requirement; and further stipulations for mail that don't fit either category, such as messages from domains that do not publish SPF data.
SPF and other authentication-based measures are designed to redress a vulnerability in SMTP, the main protocol used in sending email, which does not include an authentication mechanism.
What's the difference between SPF, DKIM and DMARC?
SPF is not the only email authentication strategy used against spammers. DomainKeys Identified Mail (DKIM) and the Domain-based Message Authentication (DMARC) protocols both work with SPF to enhance email security.
DKIM defines a protocol for claiming responsibility cryptographically for email messages sent from a domain. Cryptographic signatures are included in DKIM protocol headers, and refer to the MAIL FROM field in the SMTP packet header. DKIM stops the unauthorized use of that field for email sent by spammers.
DMARC defines a mechanism that enables email-sending organizations to define domain-level policies for email authentication and validation. This mechanism uses both SPF and DKIM, which are the protocols that define how DMARC policies are implemented.
Domain administrators implement SPF, DKIM and DMARC to keep email servers secure by battling spammers and phishing attempts. Learn about other ways to prevent business email compromise.






