email security
What is email security?
Email security is the process of ensuring the availability, integrity and authenticity of email communications by protecting against unauthorized access and email threats. Email enables billions of connected people and organizations to communicate with one another to send messages. Since email is at the foundation of how the internet is used, it has long been a target for malicious attacks.
Email security aims to help prevent attacks and abuse of email communication systems. Within the domain of email security, there are various email security protocols that technology standards organizations have proposed and recommended to help limit email risks. Protocols can be deployed by email clients and email servers, such as Microsoft Exchange and Microsoft 365, to help ensure the secure transit of email. Looking beyond just protocols, email security gateways can help organizations and individuals to protect email from various threats.
The topic of email security also includes privacy concerns, as unauthorized parties could potentially read email that contains sensitive information.
Types of email attacks
Since the earliest days of email, it has been abused and misused in different ways with no shortage of email threats.
The following are some common types of email attacks:
- Phishing. In a phishing attack, cybercriminals send malicious emails to users that seemingly look legitimate. The aim is to dupe users into divulging sensitive information, such as usernames, passwords and bank account details. Phishing manifests in various guises, including spear phishing, standard phishing and whaling. While spear phishing focuses on an individual target, whaling aims at someone of higher authority within an organization, masquerading as a trusted figure.
- Spoofing. Email spoofing is a deceptive tactic where attackers alter the sender's address in an email header to mimic a trusted source. The aim is to trick recipients into believing the email is genuine and lead them to disclose sensitive information, click on harmful links or download infected files.
- Spamming. This is the practice of bulk emailing unsolicited, irrelevant or inappropriate messages with the primary goal of promoting goods, services or websites. These messages can be annoying and might contain phishing attempts or links to malicious websites.
- Malware delivery. The main purpose of malware, or malicious software, is to harm or exploit computers and computer systems. Common forms of malware include viruses, worms, ransomware and spyware.
- Business email compromise (BEC). BEC is a type of cyber attack in which hackers target businesses, organizations or individuals to manipulate or deceive them into sending money, sharing sensitive information or taking other actions that benefit the attacker.
- Ransomware. This is a malicious attack where the attackers use malware to encrypt the files and systems of a target. Access typically isn't granted until the targeted party pays the ransom.
- Man-in-the-middle (MitM) attack. A MitM attack involves an attacker intercepting and controlling messages between two parties who think they're communicating directly. It's a form of eavesdropping where the attacker controls the conversation.
- Data exfiltration. Data exfiltration is an advanced form of email attack where an attacker illicitly steals sensitive data from an organization's email system.
How secure is email?
While email security measures have evolved, email communications aren't foolproof. According to a report by the Anti-Phishing Working Group, more than 4.7 million phishing attacks took place in 2022.
Various factors contribute to the inherent lack of complete security in email communications. The original implementation of email protocols, including Simple Mail Transfer Protocol, Internet Message Access Protocol and Post Office Protocol 3, didn't mandate the use of secure transport mechanisms, such as Secure Sockets Layer (SSL)/Transport Layer Security (TLS). As such, connections to and from an email server weren't made over an encrypted tunnel, which means that an intercepted message could have potentially been read by anyone.
Adding further complications, email messages are often stored on email servers in an unencrypted format. System administrators with access to an unencrypted email server could potentially gain access to read any email. A user email account can only be as secure as the server on which the email is stored.
The user side of email is another area that demonstrates its inherent insecurity. Access to user email accounts is commonly secured only by a username and password, which is often insufficient to deal with modern email threats. With the volume of data breaches continuing to grow year after year, an increasing number of email credentials have been leaked to public sites. Attackers can sometimes simply find user credentials for email services from public data breaches. Brute-force and password-guessing attacks are also a risk of the username-and-password approach to email access.
Email insecurity also comes from a lack of guaranteed authenticity. It's possible and common for attackers to spoof an email address and make it appear as though a fake email has come from a legitimate address. The lack of email authenticity is a common tactic used in phishing attempts, as well as spam phishing attacks that cast a wider net to attract unsuspecting victims to click.
Why is email security important?
Email is used for business communications and is often a foundational element of an organization's IT operations and ability to communicate both inside and outside of the company.
The following points highlight the importance of having secure email communications:
- A risk to email, such as a lack of access due to a denial-of-service attack, can potentially restrict the ability of a business to conduct business.
- Spam, which is another key email threat, can have negative effects on a business, including filling up inboxes with useless information and potentially leading to phishing attacks.
- Email often includes sensitive data that's intended only for the recipient of an email message. Without email security, sensitive information could be leaked to an unauthorized entity.
- The authenticity of corporate email also highlights the importance of email security. If an unauthorized individual can send an email that seemingly comes from a corporate email account, it could lead to fraud as part of a BEC attack.
- Enforcing email security safeguards sensitive data and ensures compliance with regulations such as the European Union's General Data Protection Regulation and the United States' Health Insurance Portability and Accountability Act.
- Secure email communications can prevent network disruptions and financial losses caused by malicious emails.
What are the benefits of email security for businesses?
As most organizations continue to rely on email for business operations, email security technologies and best practices provide several critical benefits for businesses of all sizes, including the following:
- Availability. At the most basic level, email security can help to ensure the continued availability of email services so a business can continue to communicate with its employees and customers.
- Authenticity. Having email authenticity measures in place can help to build trust for an organization and its users that email coming from its domain is authentic.
- Fraud prevention. The ability to identify potential email and cybersecurity risks, such as spoofing, can potentially help an organization to reduce the opportunity for fraud.
- Malware prevention. An appropriate set of security capabilities in place on an email platform can limit the risks of malware transmitted by email.
- Phishing protection. Social engineering tactics, such as phishing attacks, can trick employees to click on links or download items that could be harmful and lead to information disclosure and credential theft. Email security products use techniques to recognize and block phishing emails, shielding people and businesses against fraud and identity theft.
- Real-time defense. Email security programs that include antimalware and antispam protection can offer real-time defense against zero-day exploits.
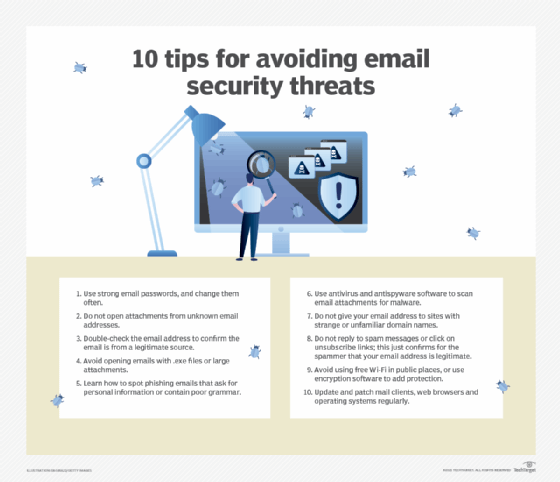
Email security best practices
While email isn't secure by default, there are proactive best practices that individuals and organizations can take to significantly improve email security, including the following:
- Enforce encrypted connections. To ensure endpoint security, all connections to and from an email platform should occur over an SSL/TLS connection that encrypts the data as it travels the public internet.
- Encrypt email. While perhaps not an ideal option for every user at every organization, encrypting email messages provides an additional layer of privacy that can help to protect against unauthorized information disclosure.
- Create strong passwords. For users, it's important to ensure that any passwords are complex and not easy to guess. It's often recommended that users include a combination of letters, numbers and symbols for their passwords.
- Use two-factor authentication (2FA) or multifactor authentication (MFA). While strong passwords are helpful, they often aren't enough. Using 2FA or MFA provides an additional layer of access control that can help to improve email security.
- Train on anti-phishing. Phishing is a common email threat. Organizations need to provide security awareness training for users so that they can avoid risky behaviors and spot phishing spam that gets through to their inbox.
- Use domain authentication. The use of domain authentication protocols and techniques, including Domain-based Message Authentication, Reporting and Conformance, can help to reduce the risk of domain spoofing.
- Employ a secure email gateway. A secure email gateway acts as a barrier, filtering incoming and outgoing emails for potential cyber threats, such as malware, phishing attempts and spam. By setting up a secure email gateway, organizations can significantly reduce the risk of malicious emails reaching recipients' inboxes, ensuring a higher level of email protection for sensitive information.
- Use secure Wi-Fi networks. Users should exercise caution regarding the Wi-Fi networks they connect to when accessing their email on the go. Opting for a virtual private network to encrypt the connection, rather than using open or public Wi-Fi networks for sensitive email tasks, is a more advisable approach.
Email security tools
Best practices alone aren't typically enough to help guarantee email security and reduce the risk from threats. Email security tools and services can help organizations with advanced threat protection and improving their security posture. Examples of these tools and security services include the following:
- Integrated online email service provider platforms. Microsoft Exchange Online, which is part of the Microsoft 365 Business Standard suite, provides users with an integrated set of email security capabilities. Similarly, Google Workspace offers an enterprise supported version of Gmail that integrates email security as part of the online service. Both Microsoft and Google services provide integrated antimalware and antispam capabilities, as well as options for encrypted data transit.
- Email security gateways. For organizations that have on-premises email systems and cloud-hosted email, an email security gateway can provide an inspection point for malware, spam and phishing attempts. Email security gateways are available from numerous vendors, including Barracuda, Cisco, Forcepoint, Fortinet, Mimecast, Proofpoint and Sophos.
The following are some common features and functionalities offered by most email security tools:
- Malware and antivirus. These tools scan email attachments and embedded links within emails to detect and block malware and viruses.
- Spam and phishing detection. These tools use complex algorithms and filters to detect and block spam emails and phishing attempts.
- Email encryption. These tools use encryption mechanisms to ensure only authorized recipients receive and access the emails.
- Data loss prevention. These tools use email content and spam filtering, policy enforcement and encryption to identify and block malicious emails and prevent the leakage of confidential data.
- Anti-spoofing. These tools use email authentication protocols to prevent spoofing and impersonation attacks.
- Reporting and analytics. These tools use reporting and analytics features to monitor email traffic, track security incidents, gain insights into potential security threats and generate detailed reports.
Although email was originally conceived without prioritizing security, specific security protocols now safeguard email communications. Explore the crucial email security protocols that businesses must adopt to ensure email security.







