
Funtap - stock.adobe.com
Streamline SecOps with SOAR workflows and playbooks
Through their automated workflows and playbooks, SOAR platforms help SOC teams overcome limited resources, skills gaps and alert fatigue.
The job of the security operations center professional isn't getting any easier. SOC teams continue to grapple with skills gaps, an overwhelming influx of security alerts and daunting resource constraints. Meanwhile, IT environments have grown increasingly complex, compounded by multi-cloud strategies, highly scalable deployments and evolving cybersecurity threats.
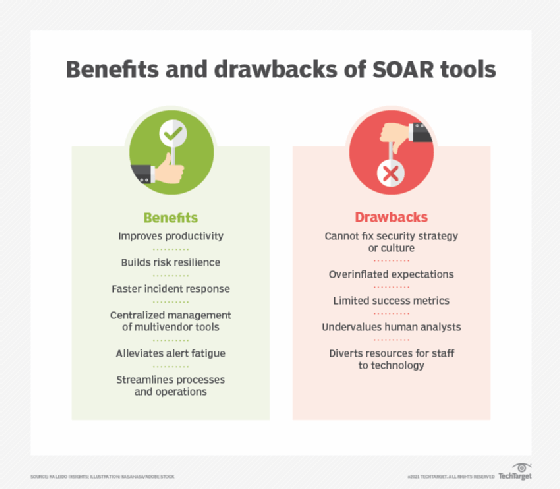
Many CISOs and IT decision-makers are confronting these challenges by embracing tools that help security teams control and optimize incident responses using advanced detection and remediation. One such technology is SOAR, or security orchestration, automation and response, which comprises a stack of technologies designed to automate and coordinate incident response, threat identification and routine operations.
Using predefined automated workflows and playbooks to execute repetitive tasks and validate security configurations, SOAR can lighten the load for security teams.
More incidents, more complexity: The case for SOAR
The sophistication and volume of security incidents continue to rise as enterprise environments become more complex. Consider the current landscape: Multivector and AI-fueled cyberattacks are common, attack frequency has doubled compared to pre-pandemic levels, and financial losses are expected to rise from about $10.5 trillion in 2025 to over $12.2 trillion in 2031. Enterprise reliance on multi-cloud, hybrid cloud, edge and IoT deployments contributes to the complexity and increases the attack surface. Expanding compliance requirements also complicate configurations and incident handling.
All this leaves CISOs and IT leadership wondering how security staff can realistically handle the escalating workload. With overworked SOC teams chasing false positive alerts and lacking the resources to address them, organizations will experience response delays and inefficient mitigation processes, which could result in vulnerabilities or breaches.
This is where SOAR comes in. By automating and orchestrating incident response and centralizing incident management, SOAR platforms help teams address a host of IT security challenges. For example, when integrated into security operations, SOAR can alleviate alert overload and fatigue, improve alert prioritization, reduce human error and ensure consistency. It thereby helps SOC teams minimize the impact of skills gaps and staff shortages. Additionally, the reports generated by SOAR platforms provide information to aid human responders and speed decision-making.
Core components of SOAR
SOAR deployments typically consist of the following elements:
- Event management. Event ingestion, correlation and enrichment engine.
- Ecosystem alignment. Integration of SIEM, endpoint detection and response (EDR), firewalls, threat intelligence platforms and APIs for external security tools.
- Procedure development. Automated incident response and remediation workflows and playbooks.
- Monitoring and reporting. Monitoring dashboards and reporting features that offer SOC teams a clear, up-to-date view of current incidents and potential issues.
What are SOAR workflows and playbooks?
SOAR workflows and playbooks are similar but not the same. Some vendors, however, use the terms interchangeably.
SOAR workflows are automated sequences of steps executed by a SOAR platform to perform a specific task in an IT system. Playbooks are complete sets of incident response procedures that often contain multiple workflows.
Consider a phishing attack. A SOAR workflow would do the following:
- Receive an alert about an email containing potentially malicious content from an email security gateway or other related tool.
- Extract URLs and attachments from the suspicious email.
- Enrich the alert with threat intelligence data.
- Assign threat indicators a risk level.
- Send an alert to the security team.
A SOAR playbook containing multiple workflows would do the following:
- Analyze the email (as outlined above).
- Trigger a remediation -- for example, blocklist the IP address of the sender.
- Alert the user about the phishing attempt.
- Trigger follow-up investigations and remediations -- for example, search other users' email inboxes and remove the malicious email.
- Send an alert to the security team.
- Create a report about the incident.
Playbooks cover various scenarios, including configuration security, resource access, configuration validation and vulnerability management. Potential use cases range from ransomware containment to insider threat investigations. CISOs must evaluate how well each scenario aligns with the organization's security and regulatory compliance requirements.
The details of SOAR workflows and playbooks will vary by incident, deployed SOAR tools and the degree of automation versus human oversight.
How to adopt SOAR
Adopting SOAR involves the following implementation stages:
- Assess the organization's current cybersecurity maturity level, incident response processes and SOC workflows.
- Define clear objectives with measurable goals.
- Identify the operational issues the SOAR platform should solve. Focus on high-volume, repetitive alerts based on common incidents and threats.
- Assess the organization's current security stack to identify needed integrations.
- Select a SOAR platform that fits the organization's needs and integrate it into existing systems.
- Design SOAR workflows and playbooks.
- Test and refine automated workflows and playbooks based on incident priority with the goal of reducing the security staff's workload.
- Train analysts and other team members to ensure a positive ROI.
- Deploy SOAR into production. Start small and scale from there.
- Build metrics and continuous improvement into the deployment. Monitor and optimize workflows and playbooks when threats evolve, processes change or whenever needed.
A successful SOAR deployment can help SOCs overcome limited resources, skills gaps, disparate technologies, complex compliance requirements and alert fatigue. Putting SOAR near the top of the security to-do list will strengthen the organization's security posture and free teams to focus on what matters most -- strategic threat analysis, incident investigation, innovation and growth.
Damon Garn owns Cogspinner Coaction and provides freelance IT writing and editing services. He has written multiple CompTIA study guides, including the Linux+, Cloud Essentials+ and Server+ guides, and contributes extensively to TechTarget Editorial, The New Stack and CompTIA Blogs.








