Top benefits and challenges of SOAR tools
To ensure successful adoption, IT leaders need to understand the benefits of SOAR tools, as well as potential disadvantages. Explore pros, cons and how to measure SOAR success.
As organizations around the world face a constant and dynamic barrage of cybersecurity threats, the development of tools to accelerate security operations, automation and response, or SOAR, has rapidly increased.
According to the latest "Internet Crime Report" from the FBI's Internet Crime Complaint Center, global losses from cybercrime amounted to $10.3 billion in 2022, a 281% increase since 2018. Adding to the challenge is the fact that infosec teams are struggling to keep up with cyberthreats due to limited resources and head count. Overextended teams may also have accumulated numerous, often disparate, security tools to contain the firehose of threats -- each of which must be monitored, analyzed and triaged.
SOAR tools are designed to take on these types of real-world enterprise data security challenges and can help assist with the following functions:
- Security orchestration that connects and coordinates heterogeneous tool sets and data sources and defines incident analysis parameters and processes.
- Process automation that automatically and intelligently triggers specific workflows, tasks and triages based on predefined thresholds, including the automated remediation of lower-risk vulnerabilities.
- Response delivered through a single source of truth view so that security, network and system analysts can access, query and share threat intelligence between teams.
There are three main business incentives for adopting SOAR tools in security programs. First, SOAR centralizes visibility and insights of automatically discovered threats. Second, it analyzes and prioritizes threats based on the level of risk to the business. Third, SOAR systems simultaneously manage low-level incidents to support and scale human analysts. From these upstream motivations flow several downstream effects that security leaders must consider.
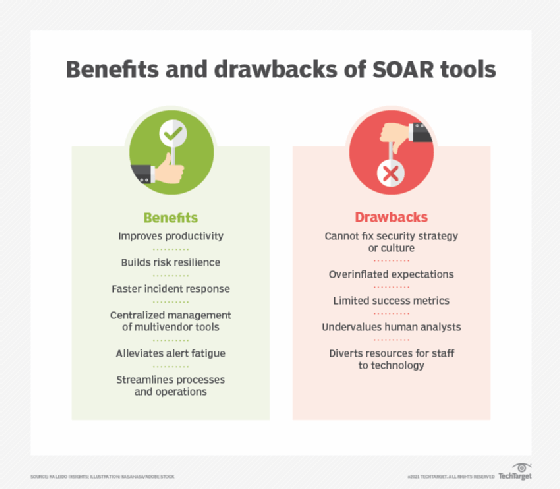
Compare SOAR benefits vs. drawbacks
To achieve the benefits of SOAR while simultaneously avoiding potential pitfalls, it behooves organizations to first look beyond the tools and technology. After all, no technology is a silver bullet for fixing broken security culture or alleviating antagonized and depleted infosec teams. Additionally, a Band-Aid deployment will not mitigate a lack of security strategy, nor outdated or patchwork tools and information.
After addressing corporate and departmental culture, assess SOAR's technical benefits to determine if the value justifies the cost of tools and implementation. To help, let's look at the benefits and drawbacks that are relevant to most enterprises.
SOAR benefits
Though adoption success may vary depending on the organization, security leaders can anticipate the following benefits of SOAR implementation:
- Improved productivity.
- Less tedious and repetitive work for humans.
- More strategic allocation for human analysts.
- Ability to make better use of existing security tools.
- Process and operational efficiencies in alerts and triage through automated and intelligent alert prioritization.
- Faster incident response and remediation.
- Improved third-party tool integration through API hooks.
- Increased resilience against a growing and rapidly changing threat landscape.
SOAR challenges
To help set expectations regarding SOAR adoption and capabilities, bear in mind the following potential pitfalls:
- Inability to assess broader or edge security maturity or integrate into strategy.
- Failure to address the security culture, which can further information silos within the IT department.
- Undervaluing of human analysts in favor of software.
- Redirection of too many security staff resources to other tasks.
- Overinflation of expectations for SOAR capabilities and intelligence.
- Integration complexities.
- Potential mistaken conflation with AI.
- Limited or unclear success metrics.
SOAR adoption considerations
To ensure successful SOAR adoption, security leaders need to identify the organizational objectives the tools will advance, how those objectives align to the broader cybersecurity roadmap and how success or failure of the technology will be measured.
For example, security operations orchestration, a core capability of SOAR, helps coordinate how SecOps detects, assesses and remediates security incidents. This objective often aligns with the strategic need for visibility and management across multiple large-scale enterprise security topologies. Potential metrics are not limited to time-centric measurements, but can also support vendor management, identifying redundancies, analyst workflows, compliance and unidentified permissions or devices, among other KPIs. Connecting these dots is as important for success as the technical integration.
It is also essential to understand SOAR not only as an enterprise tool for sheer efficiency gains, but foremost as a tool to empower human analysts. SOAR tools typically focus on common security scenarios and highly repetitive front-end steps, such as basic alert enrichment, prioritization or triggering an alert to external tools such as ServiceNow and Slack.
Because they do not defend against anomalous scenarios and are not tools for highly nuanced investigations, note that SOAR tools cannot fully replace security pros or compensate for talent shortfalls. Instead, the utility of SOAR is to lighten the load by reducing the manual effort associated with alert overload and automating the tedium of proactive risk mitigation. Successful adoption frees up highly skilled analysts to focus on more challenging assignments, emergent threats and higher-risk incidents.
Security organizations must meet ever-increasing cyberthreats with agile and adaptive security postures and infrastructure. While any form of security automation offers inherent efficiencies, SOAR technologies can compound that value by elevating the combination of human and machine strengths.
Editor's note: This article was originally written in 2021. TechTarget editors revised it to improve the reader experience.
Andrew Froehlich is founder of InfraMomentum, an enterprise IT research and analyst firm, and president of West Gate Networks, an IT consulting company. He has been involved in enterprise IT for more than 20 years.
Jessica Groopman is an industry analyst, current director of digital innovation at Intentional Futures, former founding partner of Kaleido Insights and emerging technology advisor.






