CISO reporting structure key to strong cybersecurity outcomes
Find out which CISO reporting structure a cybersecurity expert recommends, based on objective security performance metrics from hundreds of organizations.
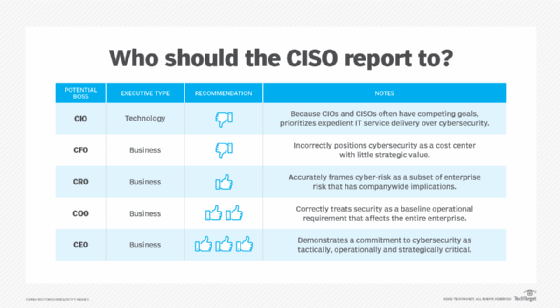
Who should the chief information security officer report to? It depends on whom you ask and on what the organization wants to accomplish by having a CISO in the first place.
That said, for the majority of organizations, it's critical to have the CISO report to a business executive rather than a technology executive, and with as few levels as possible between the CISO and the CEO. Research shows that security outcomes -- based on objective and concrete metrics -- tend to be worse in organizations where the CISO reports to someone who neither is the CEO nor reports directly to the CEO.
Common CISO reporting structures
CISOs typically report to either a business position, such as the CEO, COO or chief risk officer (CRO), or a technology position -- typically, the CIO.
The choice depends on how the organization views cybersecurity: as a transformative business enabler; as a business enabler focused on ensuring continuity and integrity in operations; as another facet of risk management; as a compliance checkbox; or as a safety precaution subordinate to delivering IT services.
CISO to CEO: Cybersecurity as strategy enabler
Research shows that organizations where CISOs report directly to CEOs tend to see the best security outcomes.
Pros of a CISO-to-CEO reporting structure
- Positions cybersecurity as a strategically and operationally critical business priority with top-level support.
- Enables the CISO to directly communicate cyber-risk to top decision-makers and align cybersecurity initiatives with business goals.
- Ensures cybersecurity is not subordinate to IT expediency by default.
Cons of a CISO-to-CEO reporting structure
- Without the right skill set -- strong business acumen, sophisticated communication abilities and a firm grasp of organizational goals -- a CISO reporting directly to the CEO will likely struggle.
CISO to COO: Cybersecurity as operational necessity
A CISO who reports to the COO typically has significant authority and influence within the broader organization, supporting strong cybersecurity outcomes.
Pros of a CISO-to-COO reporting structure
- Acknowledges cybersecurity and cyber resilience as foundational to business continuity and risk management.
- Enables the CISO to directly support daily business functions and align cybersecurity initiatives with organizational objectives.
- Puts the CISO on equal footing with the CIO and CTO -- who typically also report to the COO -- minimizing conflict-of-interest issues that arise when security reports to IT.
- With just one position between the CISO and CEO, ensures cyber-risk issues can readily reach top decision makers.
Cons of a CISO-to-COO reporting structure
- Without the right skill set, a CISO reporting directly to the COO will likely struggle.
- With no direct access to the CEO, the CISO must rely on the COO to convey cyber-risk issues.
CISO to CRO: Cyber-risk as part of enterprise risk
Some organizations that view cyber-risk as a type of enterprise risk -- similar to geopolitical risk, innovation risk, etc. -- have the CISO report to the CRO. This is an effective reporting structure if and only if the organization has a well-structured and mature risk program -- typical of financial firms, pharmaceutical companies and defense organizations, among others -- and a CRO that reports directly to the CEO.
Pros of a CISO-to-CRO reporting structure
- Contextualizes the CISO's challenges, concerns and issues within the broader scheme of enterprise risk, which, theoretically at least, is where they belong.
- Frames cyber-risk as a primary business concern, rather than a niche technical issue.
- With just one person between the CISO and CEO, ensures cyber-risk issues can readily reach top decision makers -- assuming the CRO reports directly to the CEO.
Cons of a CISO-to-CRO reporting structure
- In an immature enterprise risk program, the CRO might be inexperienced, under-resourced, too far from the ear of leadership or all three.
- In some cases, insufficient proximity to daily business operations could undermine the cybersecurity program's effectiveness and influence.
- With no direct access to the CEO, the CISO must rely on the CRO to convey cyber-risk issues.
CISO to CFO: Cybersecurity because the auditors demand it
Companies that treat cybersecurity as a checkbox requirement for auditors to approve might put their CISOs -- and, often, their CIOs -- under the CFO. Typically, such organizations see cybersecurity, along with IT, as a cost of doing business with little or no strategic value.
Pros of a CISO-to-CFO reporting structure
- Ensures the organization meets externally imposed requirements, such as compliance regulations, while monitoring and containing costs.
Cons of a CISO-to-CFO reporting structure
- Marginalizes cybersecurity, positioning it as a cost center and cyber-risk management as a box-checking exercise.
- Aligns with compliance-based cybersecurity, rather than more sophisticated risk-based strategies.
- The CISO lacks access and opportunity to communicate cyber-risks to the CEO and board.
- A CISO reporting to the CFO often has an extremely limited scope of authority, possibly without staff or even a dedicated budget.
CISO to CIO: Cybersecurity as a part of IT
It has historically been most common -- but typically least effective -- to have the CISO report to the CIO, based on the dangerous misconception that cybersecurity is largely a technology function.
This presumption is inaccurate because the CISO is charged not just with defending technology infrastructure, but with protecting the entire company. Beyond damaging an enterprise's networks and systems, for example, a successful attack can cost billions of dollars in market capitalization and tarnish the organization's brand. It's also dangerous because CIOs and CISOs often have competing priorities. When the CISO reports to the CIO, the CIO ultimately has veto power over the actions of the CISO and can control the CISO's agenda and focus.
Pros of a CISO-to-CIO reporting structure
- IT departments typically have significant and established budgets, which could benefit cybersecurity.
Cons of a CISO-to-CIO reporting structure
- Positions cybersecurity as a niche IT issue rather than a business issue and limits the CISO's influence.
- Often indicates that the business sees delivering services with inadequate security as acceptable -- albeit often only temporarily -- if it means hitting critical deadlines. In other words, doing business quickly trumps doing business responsibly.
- Creates a conflict of interest in cases where IT and cybersecurity priorities are at odds.
- The CISO lacks access and opportunity to directly communicate cyber-risks to the CEO and board.
How to choose the right CISO reporting structure
In our work at Nemertes Research, my colleagues and I have surveyed many hundreds of security and business executives, asking to whom their CISOs report and collecting objective cybersecurity success metrics. Certain CISO reporting structures clearly and consistently align with better outcomes.
The data shows that companies with the greatest cybersecurity success typically have CISOs who report directly to top-level business executives, rather than to CIOs or lower-level business executives.
In many cases, reporting to the CEO is optimal. Cybersecurity is an existential issue for any company that relies on IT to conduct business -- which is to say nearly every company, of all sizes and from across sectors. Having the leader of cybersecurity report to the leader of the company signals its importance unambiguously. If a company is big enough to have a CISO, that CISO should report to the top.