
Alex - stock.adobe.com
Attackers targeting storage infrastructure for remote work
Threat actors are pivoting from endpoints to storage, crippling backups and exploiting cloud misconfigurations. See how identity, remote work and zero trust gaps fuel ransomware.
Threat actors are no longer content with targeting endpoint systems. They have more to gain if they go after storage infrastructure directly. An enterprise data breach can provide them with access to vast amounts of valuable data, with the least amount of effort. By taking advantage of on-premises and cloud storage vulnerabilities, attackers can exploit storage backup security flaws, launch ransomware targeting storage systems, carry out credential theft and exfiltration, and in other ways compromise data.
Why target storage infrastructure?
We've entered a new era in cybercrime, with storage the next frontier. Threat actors are going directly after storage infrastructure because it contains large stores of high-value data, including personal information, intellectual property, file shares, system logs, source code, configuration files, financial records, AI training data and much more.
Storage infrastructure also hosts backups and snapshots, which have become prime targets for enterprise cyber threat actors who want to neutralize recovery capabilities before carrying out their extortion campaigns. Stored data might also include credentials, service account keys, connection strings or other access data, making it possible for attackers to move laterally through an organization's systems, spreading the blast radius even further.
By attacking storage infrastructure, threat actors can maximize their impact far more efficiently than they can achieve by going after individual endpoints. Once they infiltrate a storage system, they can release ransomware that targets the storage systems. They might also destroy backups, corrupt data, steal data or manipulate information and settings. They might also use the stolen credentials to branch out to other connected systems and third-party services.
A storage infrastructure attack can impact an organization in many ways, including regulatory fines, loss of productivity, reputational damage, operational disruption, revenue loss, recovery costs, exposed data and legal expenses. Threat actors are particularly interested in cloud storage, such as carrying out Azure Blob Storage attacks, because these platforms often house massive amounts of high-value data.
Despite these threats, many storage systems lack comprehensive protections, relying instead on endpoint and network security to protect the data. For example, a storage system might use shared credentials or unmanaged service accounts, fail to employ zero-trust for storage access, assign over-privileged access to resources, or lack proper monitoring or network segmentation.
Storage systems are also commonly misconfigured, especially in complex hybrid cloud environments, leaving their systems susceptible to enterprise cyber threat actors who take advantage of cloud storage vulnerabilities, including storage backup security flaws.
Given the lack of protections, along with the amount and quality of data, threat actors have been steadily switching their focus from endpoints to storage infrastructure. This momentum is also fueled by the growing effectiveness of endpoint security platforms, which make it more difficult to carry out traditional attacks against managed devices. In addition, threat actors recognize the importance of going after an organization's backups directly and using storage as a pivot point for permission escalation and lateral movement into other systems and data stores.
Remote work cybersecurity risks
When employees work remotely, they access storage resources from outside the safety of the internal corporate network and perimeter firewall. They might connect from their homes, hotel rooms, cafes, airports, mobile hotspots or other public locations, using a variety of devices and connection protocols. If they're traveling, they might be connecting from just about any place in the world, often at any time of day or night.
IT teams have no control over or visibility into outside networks, making it difficult to predict access patterns or identify subtle anomalies in behavior. At the same time, remote networks often have weaker protections in place and are not as carefully implemented or maintained. For example, a Wi-Fi network might be set up with default account passwords, or the router might be running unpatched firmware, leaving the network susceptible to different types of attacks, such as man-in-the-middle attacks.
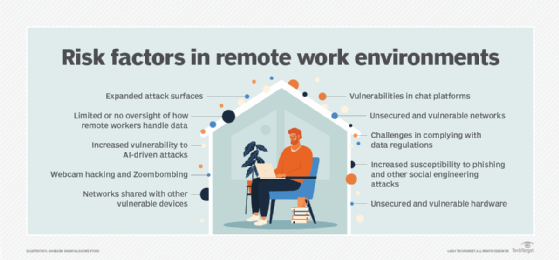
IT teams also have limited control over the remote endpoints and their users' behavior when working remotely. Remote users might use personal devices that lack enterprise protections such as data loss prevention or endpoint detection and response. The devices might also be running outdated or unpatched software or lack proper antimalware protection. In addition, users might share their devices with other people, leave the devices unlocked or lying around, or in other ways fail to protect their devices from potential risks.
When an organization supports remote workers, identity becomes the new perimeter, rather than firewalls and other network protections. Remote work relies extensively on identity and access management, multifactor authentication (MFA), single sign-on and other access technologies to protect corporate resources. If any of these are compromised, attackers might be able to access network resources without being detected.
Remote workers also rely on different types of access mechanisms when connecting to corporate resources. For example, they might use VPNs, Remote Desktop Protocol sessions or cloud storage APIs. Any of these can be misconfigured or outdated, giving threat actors additional remote access attack vectors.
In addition, organizations often loosen permissions on resources to support greater flexibility and collaboration and increase productivity among remote workers. Users might also get careless in their everyday operations, such as failing to use MFA when connecting to resources or storing API keys on their computers.
Remote work also increases the risks of shadow IT. Workers might use tools or data services not sanctioned by IT, such as storing sensitive data in their personal Dropbox accounts or maintaining their own GitHub repositories for proprietary source code. Shadow IT can lead to fragmented and compromised data, as well as uncontrolled data sprawl, while denying IT teams the visibility they need to safeguard that data.
For all these reasons, remote workers have become prime targets for credential theft, MFA fatigue attacks, OAuth abuse and other threats, increasing the risk of storage infrastructure attacks. This, in turn, can lead to ransomware targeting storage systems, credential theft and exfiltration, and other types of data compromise.
How a successful cyberattack can impact an organization
More than ever, enterprise cyber threat actors are targeting on-premises and cloud storage vulnerabilities, taking advantage of remote work cybersecurity risks wherever possible. A successful attack can have a devastating impact on remote work, as well as the storage infrastructure and organization as a whole:
- Remote work. If storage becomes unavailable because of a cyberattack, remote workers can no longer access the data they need, nor can the applications that rely on that data continue to operate properly. In many cases, work stops completely or is severely handicapped, resulting in lost productivity and the inability to meet business objectives and carry out strategic initiatives. In addition, users must often contend with credential resets, tighter access controls and modifications to operations and workflows, along with uncertainty about whether they can trust the data.
- Storage infrastructure. An attack on storage can result in data encryption, corruption, modification, deletion or exfiltration. Any data housed in that system can be compromised -- including backups, snapshots, metadata, system settings and credentials -- and the organization can no longer rely on the data's integrity, accuracy or completeness. The storage infrastructure might also be physically damaged or suffer resource exhaustion, perhaps causing systems to overheat or fail. In some cases, the storage controller firmware is corrupted. Attackers might also steal or update security and configuration settings and then prevent authorized access or use the information to access other data or systems.
- Organization. A successful attack on storage infrastructure can impact an organization in a number of significant ways. The financial impact alone can be staggering. The organization can face ransom costs, legal fees, regulatory fines, incident response and recovery costs, forensic service fees and much more. The organization might also experience lower productivity, lose revenue and even see a drop in its market value, while suffering considerable reputational damage that can take years to repair.
According to IBM's Cost of a Data Breach Report 2025, the global average cost of a data breach was $4.4 million for that year. This is actually a 9% decrease from the previous year, which IBM attributes to faster identification and containment. However, an enterprise data breach can cost an organization much more.
In May 2025, for example, Coinbase was the victim of a cyberattack on its customer data. According to a Coinbase press release, "Cyber criminals bribed and recruited a group of rogue overseas support agents to steal Coinbase customer data to facilitate social engineering attacks." The threat actors demanded $20 million in ransom fees, which the company refused to pay. Instead, Coinbase set up a $20 million reward fund for information leading to the arrest and conviction of those responsible for the attack. At the time, it was widely reported that Coinbase estimated the attack could cost the company up to $400 million.
Tools for protecting the storage infrastructure
An organization can protect its storage infrastructure from enterprise cyber threat actors only if IT and security teams have the tools they need to safeguard the data and protect the environment in which it resides. The following table provides an overview of some of the more popular tools available for protecting data and storage infrastructure. However, these are just a sample of the different types of products out there. An organization should carefully vet and choose tools that best work for their circumstances and storage environments.
Regardless of the tools they choose, IT and security teams must still be diligent in securing their storage systems, such as implementing zero-trust for storage access, safeguarding remote access attack vectors, air gapping backups and snapshots as well as encrypting audit logs. They should also ensure that their storage security is properly integrated into the organization's larger security strategy to ensure consistent and complete protection wherever the data resides and however it is accessed.







