
arthead - stock.adobe.com
Windows 365 security features for IT admins to know
Like any technology that supports end-user PCs, Windows 365 environments need properly configured security controls. IT must learn how to support these Cloud PCs before deployment.
Microsoft's Windows 365 Cloud PC service is a strong alternative to using a single physical endpoint in the enterprise, but organizations need to ensure that their cloud PCs are secure.
Fortunately, Microsoft has included several notable features to ensure Windows 365 maintains strong security posture, and these features could make a difference for enterprise administrators.
What security benefits does Windows 365 Cloud PC include?
The security features that come with Windows 365 Cloud PC vary based on the subscription plan. For example, an Enterprise-level license includes features that are not a part of a Business-level license.
Regardless of which plan organizations subscribe to, they have access to a solid baseline of features to ensure Windows 365 security. For example, Microsoft automatically keeps its Cloud PCs up to date with the latest cumulative updates. A timely patch application is critical to keeping Windows secure for any endpoint accessing a desktop.
Likewise, Windows 365 stores data on the cloud, thereby mitigating at least some of the risks associated with local data on physical devices. IT administrators can configure Enterprise-edition Windows 365 Cloud PCs to access on-premises resources, but that generally requires a site-to-site VPN between the organization's data center and the Azure public cloud. This approach requires admins to configure the environment to allow DNS name resolution in Azure and on-premises environments.
One of the key differences between the Business and Enterprise editions of Windows 365 is that Microsoft automatically enrolls Enterprise-level Cloud PCs in Microsoft Endpoint Manager (MEM). This means that IT can use Microsoft Intune to apply security policies to Cloud PCs. MEM also supports Azure AD, Windows Autopilot and Endpoint Analytics for various management tasks.
One of the greatest benefits of using MEM is Microsoft Defender for Endpoint. All Windows 365 Cloud PCs include Microsoft Defender, but Defender for Endpoint is only included with Enterprise subscriptions.
What is Microsoft Defender and how does it support Windows 365 environments?
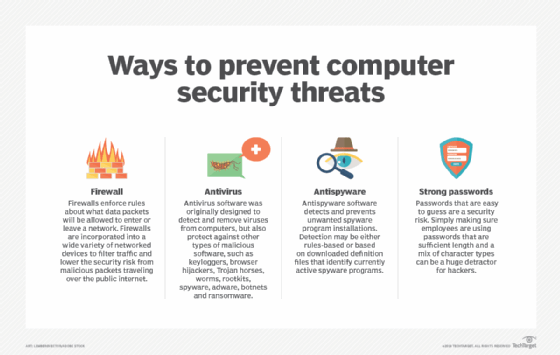
Microsoft Defender, which used to be known as Windows Defender, is a suite of security features that can enhance any organization's Windows environment. The Windows Firewall, for example, was rebranded as the Windows Defender Firewall. Microsoft Defender is natively included in Windows 10 and 11, both on physical devices and Windows 365 Cloud PCs.
Microsoft Defender's centerpiece is its antivirus capabilities, a native part of Windows for many years. Unlike third-party antivirus applications, Microsoft Defender is included with the OS and does not require a separate annual subscription. Generally, third-party antivirus vendors provide more frequent virus signature updates, so they tend to offer better protection against the most recent malware variants.
Microsoft Defender and the Microsoft Defender Firewall are part of Windows Security and included with Windows 10 and 11. Windows Security includes virus and threat protection, account protection, firewall and network protection, app and browser control, device security and device performance.
Microsoft also offers Microsoft 365 Defender. Microsoft 365 Defender is not included with Windows 365. However, it is included with Microsoft 365 E5 plans, which many Windows 365 subscribers may already have. Organizations can also purchase Microsoft 365 Defender as an add-on for other Microsoft 365 subscriptions, and they can do the same for Microsoft's identity protection service -- called Microsoft Defender for Identity.
Microsoft 365 Defender pulls security information from across the Microsoft 365 ecosystem and presents that information on a centralized dashboard. This dashboard design aims to help security admins detect and respond to the most critical threats while filtering out noise alerts.
The previously mentioned Defender for Endpoint, which is included with Microsoft Endpoint Manager, is a cloud-based vulnerability management system for endpoints. It focuses on the ability to detect endpoint vulnerabilities or misconfigurations in real time. In many cases, Defender for Endpoint can automatically remediate these issues according to preset policies or Microsoft's established best practices.
Defender for Endpoint offers malware protection beyond what is available with Microsoft Defender. Rather than relying solely on malware signatures, Defender for Endpoint uses behavior-based analytics and machine learning to detect malware and other types of attacks. Microsoft offers two different editions of Defender for Endpoint -- P1 and P2. While both provide next-generation malware protection, the more advanced capabilities are only found in P2 subscriptions.








