managed service provider (MSP)
What is a managed service provider?
A managed service provider (MSP) is a third-party company that remotely manages a customer's information technology (IT) infrastructure and end-user systems. Small and medium-sized businesses (SMBs), nonprofits and government agencies hire MSPs to perform a defined set of day-to-day management services. These services may include network and infrastructure management, security and monitoring.
MSPs often handle management services on a daily basis so customer organizations can focus on improving their services without worrying about extended system downtimes or service interruptions.
While some MSPs may specialize in specific segments of IT, such as data storage, others focus on specific vertical markets, such as legal, financial services, healthcare or manufacturing. Managed security service providers, for instance, offer specialized types of services, such as remote firewall administration and other security-as-a-service offerings. Managed print service providers maintain printers and supply consumables. Often, MSPs perform their tasks remotely over the internet.
The evolution of MSPs began in the 1990s with the emergence of application service providers (ASPs), which offered a level of service for remote application hosting. ASPs helped pave the way for cloud computing and companies that would provide remote support for customers' IT infrastructure. MSPs initially focused on the remote monitoring and management (RMM) of servers and networks. Over time, they have expanded the scope of their services as a way to differentiate themselves from other providers.
Today, the terms cloud service provider and managed service provider are sometimes used synonymously when the provider's service is supported by a service-level agreement (SLA) and is delivered over the internet.
What are MSPs used for?
Hiring a managed service provider can help an organization improve its operations.
SMBs are typical MSP customers. Many smaller companies have limited in-house IT capabilities, so they may view an MSP's service offering as a way to obtain IT expertise. But larger enterprises may also contract with MSPs. For example, government agencies facing budget pressures and hiring limitations may contract with an MSP to supplement their in-house IT staff.
MSPs handle the complex, time-consuming or repetitive work involved in the management of IT infrastructure or end-user systems. MSPs typically do the following:
- Manage IT infrastructure.
- Offer technical support to internal staff.
- Add cybersecurity software to IT systems.
- Manage user access privileges.
- Handle contract management.
- Support compliance and risk management.
- Provide payroll services.
How do MSPs work?
When a managed service provider is requested to meet the business objectives of an organization, it is often expected to fill in some gap or role in an IT system or staff. Communication between the MSP and the organization typically begins with an assessment that determines the organization's current environment. This assessment may point out potential room for improvement and how to properly support business goals.
There is not one specific setup for every organization, so an MSP may provide many different service options. Two examples of MSP offerings are technical support fix services and subscription services.
MSP technical support fix services focus on remotely fixing or sending technicians to a business's location to resolve any issues. MSPs that provide this option charge the company for the time spent troubleshooting and for any parts used to repair the problem.
MSPs that offer a subscription service model work on the quality of service of an organization's network and usually bill customers monthly. If an issue arises, the MSP will fix the problem as part of the agreement between the organization and the MSP. Payment through the subscription model is based on defined rates per computer or equipment.
Maintenance, security, monitoring, reporting and other services are defined using an SLA that documents what the organization can expect from the MSP. Response times, performance and security specifications are also included in the service agreement.
MSPs may deliver their own native services, other providers' services or an integrated mix of the two. Pure-play MSPs specifically focus on one vendor or technology and more commonly offer their own native services.
MSPs also focus on deploying specialist software platforms that automatically manage functions. These platforms consist of RMM tools and professional services automation (PSA) applications:
- RMM software enables off-site technicians to maintain IT systems, such as networks, servers, desktops and mobile devices. These tools also enable MSPs to apply patches and other system updates.
- PSA tools enable an MSP to manage an organization's projects, billing, assets and inventory.
A managed service provider often provides its service offering under an SLA -- a contractual arrangement between the MSP and its customer. The SLA spells out the performance and quality metrics that govern the relationship. Organizations need to be precise when agreeing on the commitments they make in SLA contracts.
An SLA may be linked to an MSP's pricing formula. For example, an MSP may offer a range of SLAs to customers, with the customer paying a higher fee for higher levels of service in a tiered pricing structure.
What are the types of MSPs?
The types of managed service providers can differ depending on the criteria chosen to categorize them. For example, if a business chooses to organize MSPs by the size of their target customers and how much responsibility they take on, MSPs can be organized in the following way:
- Pure-play MSPs. These tend to be smaller providers that focus on monitoring networks and application performance. They offer their own native services that focus mainly on reporting and alerts.
- Staffing legacy MSPs. These MSPs generally target midlevel organizations and Fortune 500 companies and often offer a wide range of services, including monitoring, reporting, and software installation and upgrades.
- High-level MSPs. These consist of small and large providers that enable their clients to outsource as much of their IT processes as needed. Typically, high-level MSPs offer a wide range of services.
MSPs can also be categorized by the type of services they offer:
- Monitoring. These MSPs offer real-time monitoring software for different applications, network devices, servers or websites.
- Remote support. These MSPs offer cloud-based software, support remote devices and remotely troubleshoot technical issues.
- Proactive support. These MSPs perform preventative maintenance to stay ahead of any device or network issues that could arise.
- Centralized management. These MSPs provide a management console for complex networks, remote monitoring, patch management and security software.
- Scheduled maintenance. These MSPs offer organizations regularly scheduled network maintenance.
- Simplified billing. These MSPs handle invoicing, payments and budgeting via a billing management system.
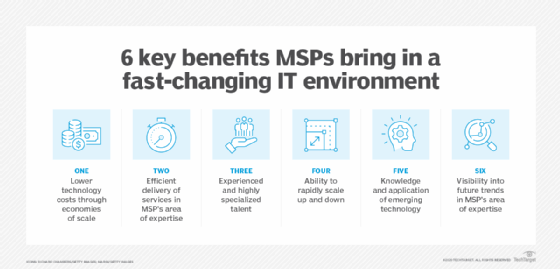
What are the benefits of managed service providers?
Benefits of managed service providers include the following:
- Help an organization fill staff shortages. If an organization lacks workers, it can outsource some of its tasks to the MSP.
- Provide expertise. Hiring a reputable MSP provides an organization with access to expert resources.
- Provide business continuity. An SLA documents the MSP's obligations to the business to prepare for or recover from a disaster.
- Provide constant network monitoring. Many MSPs offer 24/7 monitoring services using network monitoring tools that offer system visibility and cloud management.
- Improve security. Some MSPs provide security software and awareness training.
- Improve cost efficiency. If numerous unplanned repairs are needed, paying a fixed monthly charge can be more cost-effective than paying hourly. While the MSP handles the day-to-day management services, customer organizations can focus on improving their services.
What are the challenges of managed service providers?
Despite their advantages, managed service providers may also come with challenges, for example:
- Not all MSPs offer security measures. Many MSPs do not have a major focus on cybersecurity.
- Dependent on third-party organizations. Organizations that depend on an MSP to handle daily tasks may form a reliance on them. If the MSP fails to follow through on the SLA, the organization could experience system downtime.
- Waiting on a response. It may take time for an MSP to respond to an issue.
- Potential upselling. An MSP may try and upsell an organization on technology or services they do not need.
- Inaccessible information. An organization's information may not be freely accessible if the MSP is using a proprietary tool to manage and monitor its infrastructure.
What is the pricing model for managed service providers?
Managed service providers typically use one of the following pricing models:
- Per-device pricing. The MSP charges the customer a flat fee for each device it manages.
- Per-user pricing. The MSP charges a flat fee for each user, accommodating users who use multiple devices.
- All-inclusive pricing. Also referred to as the all-you-can-eat model, the MSP charges a flat fee for its IT infrastructure support and management services.
- Tiered pricing. Organizations can choose the bundle of services that best fits their needs. This is typically a favored pricing model for MSPs.
- Monitoring-only pricing. MSPs only offer monitoring and alerting services for an organization's IT infrastructure.
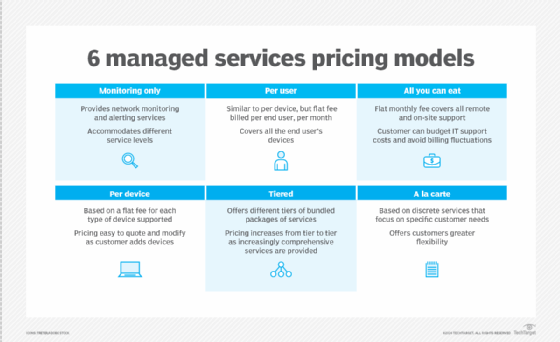
In each of these pricing approaches, the customer pays the flat fee on a regularly scheduled basis, often monthly. Such pricing methods let MSPs sell services under a subscription model. This approach provides the MSP with a monthly recurring revenue (MRR) stream, in contrast to IT projects that tend to be one-time transactions.
MRR differs from other business models, as providers pursuing the break/fix model, for example, usually price their services on a time and materials basis. They generally bill an hourly rate for repairing a customer's IT equipment and charge for parts or replacement gear.
Learn what MSP trends are expected to shape the year and set the stage for the ongoing development of other technologies, including cloud computing.






