authentication factor
What is an authentication factor?
An authentication factor is a category of credential that is intended to verify, sometimes in combination with other factors, that an entity involved in some kind of communication or requesting access to some system is who, or what, they are declared to be.
Each category of credential is considered a factor. For example, usernames and passwords are the same type of factor, so their combined use is single-factor authentication (SFA), despite the fact that there are two elements involved.
Types of authentication factors
The three categories of authentication factors are generally broken down as:
- Knowledge factors. A knowledge factor is something you know, such as a username and password.
- Possession factors. A possession factor is something you have, such as a smart card or a security token.
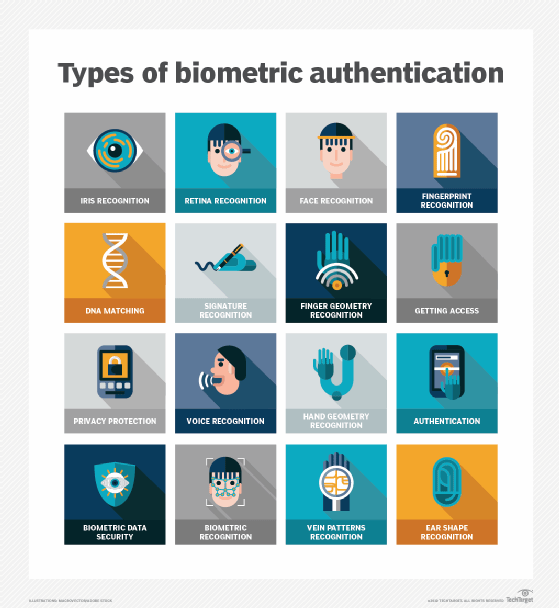
- Inherence factors. An inherence factor is something you are. This includes biometric factors such as a fingerprint, voice or iris pattern.
SFA vs. 2FA vs. 3FA vs. MFA
SFA is based on one category. The most common SFA method is a username and password combination (something you know). The security of SFA relies to some extent on the diligence of users. Best practices for SFA using passwords include selecting strong, unique passwords and not reusing passwords across accounts.
Systems and networks that contain sensitive data should use more than one authentication factor.
Two-factor authentication (2FA) uses two of the three categories. 2FA often includes a username-password combination, in addition to a security token, such as a key fob or smart card, a PIN or biometric, such as a fingerprint scan.
Three-factor authentication (3FA) requires the use of credentials from each of the three categories. An example of 3FA would be entering a PIN (something you know) to unlock your smartphone (something you have) and then supplying an iris scan (something you are) to finalize authentication.
Multifactor authentication (MFA) involves two or more independent credentials for more secure transactions. Like 2FA or 3FA, MFA can involve something you know, something you have and something you are.
Editor's note: This article was originally written by Ivy Wigmore. It was republished in March 2023 to improve the reader experience.







