cardholder data environment (CDE)
What is a cardholder data environment (CDE)?
A cardholder data environment (CDE) is a computer system or networked group of IT systems that process, store or transmit cardholder data or sensitive payment authentication data. A CDE also includes any component that directly connects to or supports this network.
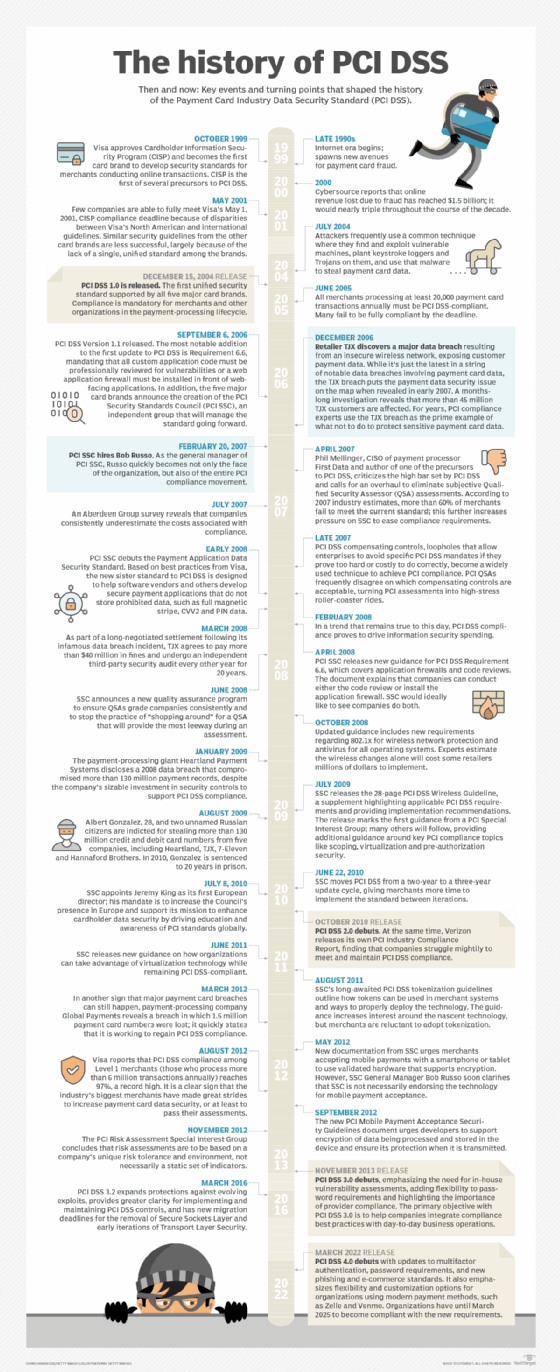
The Payment Card Industry Data Security Standard (PCI DSS) defines a CDE as "the people, processes, and technologies that store, process, or transmit, cardholder data or sensitive authentication data [SAD]."
A cardholder refers to any person who receives a payment card (credit or debit) from a card-issuing company and is authorized to use it. Cardholder data refers to the information that identifies the cardholder, is printed on the card, and lets the issuer track accounts. The data includes a unique card number that identifies both the card issuer and card user, and the cardholder name, card issuing date, expiry date and service code (if provided).
When the cardholder makes a payment using that card, numerous entities are involved in processing the card to facilitate the transaction and complete the payment. Some entities may also store the cardholder data or transmit it to other entities. Together, all these entities that are exposed to cardholder data and involved in authenticating the cardholder via "secret" information -- like a personal identification number (PIN) or CVV code -- constitute the CDE. The more entities that are part of the CDE, the greater the "scope" of the CDE.
IThe PCI DSS specifies what kind of cardholder data can or cannot be stored in the CDE. Generally, data about the cardholder, including their name and card number, can be stored in the CDE, but SAD like the PIN number or CVV cannot be stored. Not storing SAD in the CDE limits the risk of fraud since it prevents a malicious actor from accessing the authentication information required to complete an unauthorized transaction.
Examples of entities in a cardholder data environment
Examples of entities that may be part of a particular CDE include the following:
- Point-of-sale systems. POS systems accept a user's card and process it to complete the transaction. Since these systems read cardholder data and authenticate the cardholder, they are part of the CDE.
- Servers. When electronic transactions are processed, one or more servers are always part of the CDE. Some may be physical; others may be virtual.
- Applications. Servers and applications go hand in hand. Applications are hosted on servers and enable cardholder data processing.
- Network devices. As the cardholder data flows through the network, it may encounter many network devices. These devices may inspect the data and perform other operations on it, which is why they are also part of the CDE.
The need to protect the cardholder data environment
Different organizations may own or operate the various entities that constitute a cardholder's environment. Since all these entities are involved in processing a cardholder's data, they must all be secured to prevent the data from falling into the wrong hands. If a cybercriminal can access sensitive cardholder data, they might execute fraudulent transactions on that card or steal the cardholder's identity.
To avoid such situations, all organizations that collect, process or store cardholder holder and have entities that are part of the CDE must implement measures to protect the CDE. In doing so, they can better protect cardholders from fraud and identity theft as well as comply with the PCI DSS.
Securing CDE entities for PCI DSS compliance
The PCI DSS includes specific requirements for securing electronic payment and authentication data residing on all physical and virtual components in the CDE:
- Network components, such as firewalls, switches, routers, access points, network appliances and security appliances.
- POS systems, such as payment terminals, cash registers, card readers and other systems that intake payment card data from a customer at the time of a payment transaction.
- Servers, including web servers, application servers, database servers, authentication servers, mail servers, proxy servers, network time protocol servers and domain name servers.
- All applications both internal and external.
- Any virtual component, including virtual machines, virtual switches, virtual routers, virtual appliances, virtual applications, virtual desktops and hypervisors.
- Third-party IT systems.

Most data breaches in the retail sector involve a compromise of the CDE. PCI DSS requires various controls to secure the CDE. The idea of one such control, network segmentation, is that if the size and scope of the CDE is minimal and is adequately isolated from other parts of the network using technology and rule sets, this will reduce the likelihood of a data breach.
Besides segmentation, the PCI DSS requires organizations to implement these measures to protect the CDE:
- Install a firewall and ensure it remains active continuously.
- Do not use default passwords for systems that are part of the CDE.
- Minimize the amount of stored cardholder data.
- Securely encrypt cardholder data if the data is sent over open/public networks.
- Implement and regularly update antivirus programs.
- Regularly patch all systems and applications to remove exploitable vulnerabilities.
- Restrict access to cardholder data on a strict need-to-know basis.
- Restrict physical access to cardholder data.
- Monitor all access to cardholder data and maintain transparent access records to enable auditability and increase accountability.
- Regularly test the performance and robustness of all security systems and processes.
- Maintain an up-to-date information security policy for all employees and third parties.
Learn more about the best practices for complying with the new PCI DSS 4.0. Explore best practices and tactics to prevent a data breach, and check out how cybercriminals steal credit card information.






