How to perform a data risk assessment, step by step
Data risk assessments review how an organization protects its sensitive data and identify necessary improvements by revealing potential vulnerabilities, threats and other risks.
Most organizations today count sensitive data among their most valuable assets. It is vital to safeguard the security and privacy of this data to avoid data breaches, intellectual property theft and other compromises that might result in fines, lawsuits and -- in the worst case -- business failure.
Security teams use various tools and technologies to protect sensitive information, and it is critical that these tools and technologies work as intended. This is where a data risk assessment comes in. This review of how an organization protects its sensitive data helps teams identify improvements by searching for potential vulnerabilities, threats and other risks in the security program.
Let's dig into what a data risk assessment is and how to perform one.
Why is a data risk assessment important?
Data risk assessments give organizations visibility into how they handle valuable data.
Organizations generate and gather massive amounts of data and store it across different geographic sites and platforms. Tracking this data, as well as who has access to it and how it's stored, is difficult. Without added visibility, organizations could leave that data exposed or accessible to unauthorized parties.
A structured assessment, known as a data risk assessment, provides organizations with visibility into how they handle valuable data and makes it easier for them to evaluate the risks their data faces.
This article is part of
What is data security? The ultimate guide
Organizations should conduct periodic data risk assessments as part of an audit to identify information security and privacy control shortcomings and reduce risk. Data risk assessments are also necessary after a data breach, whether intentional or inadvertent, to improve controls and reduce the likelihood of a similar breach occurring in the future.
Benefits and drawbacks of data risk assessment
Data risk assessments come with a host of benefits, including the following:
- Cost savings. Costs associated with data breaches, such as legal fees and revenue losses, can be mitigated by identifying data security risks in advance.
- Security. Organizations can proactively strengthen their security posture by identifying vulnerabilities and threats before they become issues.
- Compliance. Organizations can conduct an assessment to ensure compliance with applicable regulatory frameworks, such as GDPR or HIPAA.
- Decision-making. Data risk assessments help inform leadership decisions on security and data management.
Yet assessments also face the following challenges:
- Complexity. Organizations with massive amounts of data might store it across multiple distributed or hybrid environments and use first- and third-party services, making it more difficult to analyze and secure.
- Visibility. Although assessments help improve visibility, it might initially be difficult to account for all data across distributed and hybrid environments.
- Subjectivity. Determining which threats pose the greatest risk to data can be a subjective process.
How to perform a data risk assessment
Follow these steps to conduct a thorough data risk assessment.
Determine the scope of the assessment
The scope outlines the systems, processes and data being evaluated. This step also includes defining which regulations apply to the data and identifying key stakeholders, such as the owners of the assessment.
Note that an organization might have so much data that it is not feasible to review it all during each assessment. If necessary, prioritize the most sensitive data, the data with the most stringent requirements or the data that has gone the longest without assessment.
Inventory sensitive data
Document all data assets, including what they are, where they are stored -- on-premises, in the cloud, on endpoints -- and the access controls used for them. Also, identify who is responsible for each data instance in case they need to be contacted.
Check endpoints, cloud services, storage media and other locations to find and record all data instances. Include any characteristics that might influence risk requirements. For example, the geographic location of stored data affects which laws and regulations apply.
Assign data classifications to each data instance
Classify data based on its sensitivity and criticality. Every organization should have a clearly defined data classification policy that outlines how to categorize structured and unstructured data. Data classifications based on sensitivity often include public, internal, private, confidential, personally identifiable information and financial data. These definitions should specify which security and privacy controls are mandatory and which are recommended for each data type.
Even if data already has a classification, recheck it periodically. The nature of data can change over time, and new classifications might emerge that apply to the data in question.
Identify threats
Identify potential internal and external vulnerabilities, risks and threats to data. This could include cyberattacks, third-party risks, insider threats and data loss.
Assess and analyze risks
For each threat and risk listed in the prior step, analyze how likely it is to occur and what its impacts would be. Impacts might include financial losses, operational disruptions, regulatory penalties and reputational damages.
Use qualitative and quantitative methods to rank risks by severity and business relevance.
Evaluate existing security and privacy controls
Audit the controls in place that protect sensitive data wherever it is used, stored or transmitted. Common audit steps include the following:
- Verify the privilege of least privilege. Confirm that only the necessary human and nonhuman users, services, administrators and third parties -- including business partners, contractors and vendors -- have access to sensitive data and that they have only the access required, such as read-only or read-write.
- Ensure all policies restricting access to data are actively enforced. For example, an organization might limit access to certain sensitive data based on the following factors:
- The location of the user.
- The location of the data.
- The time of day.
- The day of the week.
- The user's device type.
- Ensure all other necessary security and privacy controls are in use. Common tools to mitigate risk include the following:
- Data loss prevention software.
- Firewalls.
- Encryption.
- MFA.
- User and entity behavior analytics.
- Identify data retention violations. Determine whether any data that is present should be destroyed to comply with data retention policies.
Monitor and report findings
Monitor and take notes during the assessment steps. After the assessment, create a report that identifies the threats, the results of the risk analysis and gaps in coverage.
While identifying security and privacy deficiencies is within the scope of a data risk assessment, fixing them is not. It's reasonable, however, for an assessment to include the following information for the remediation team:
- A relative priority level for each deficiency. For example, rank by priority: high, medium, low. Or on a numerical scale or by potential impact, such as operational downtime.
- A recommended course of action to address each deficiency. Include steps to mitigate or fix the risk, for example, implementing new controls, updating policies or conducting employee training.
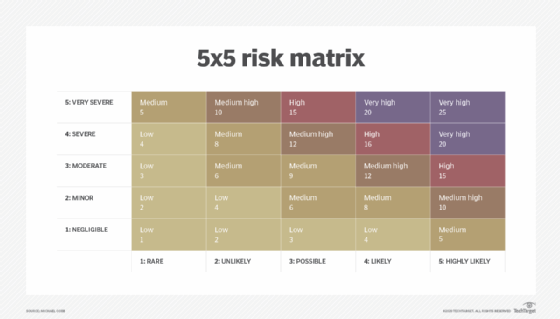
These recommendations ideally inform a roadmap toward better security. A risk matrix can help organize and prioritize issues based on the severity of potential consequences and the likelihood of their occurrence.
How to use data risk assessment results
CISOs and other enterprise leaders should formulate a strategy to mitigate the security and privacy shortcomings uncovered in the data risk assessment. Consider remediation recommendations and prioritize high-risk issues.
Ultimately, the output of a data risk assessment should be a major input to an organization's risk management and mitigation program, enabling more informed decision-making that helps improve data protection.
Alexander S. Gillis is a technical writer for WhatIs. He holds a bachelor's degree in professional writing from Fitchburg State University.
Karen Kent is the co-founder of Trusted Cyber Annex. She provides cybersecurity research and publication services to organizations and was formerly a senior computer scientist for NIST.






