
Getty Images
Meaningful metrics demonstrate the value of cyber-resiliency
Cyber-resilience metrics translate raw technical performance into real business outcomes. The right analytics can enhance more than just security operations.
Business leaders face daily threats to the security of their information systems -- phishing attacks, DDoS attacks, viruses, ransomware and more. Many organizations have IT departments to address cybersecurity and manage threats to information systems, applications, websites networks and data. Larger enterprises likely have a security team or security operations center dedicated to preparing for, preventing and responding to cybersecurity incidents.
But what happens in the aftermath of a cyberattack? How does the organization weather the intrusion? How well does it respond to the incident and then adapt and modify operations to better recover from future attacks?
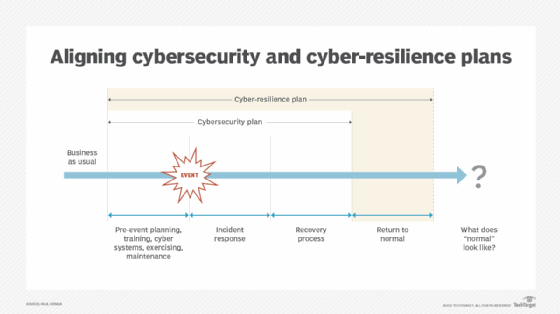
Cyber-resilience is the ability to manage the outcomes of a cybersecurity incident and, more importantly, make changes to business and technology. Mature security operations have the data and insights to establish effective cyber-resilience programs that provide measurable value to the business.
Why CISOs need cyber-resilience metrics
As with many aspects of cybersecurity management, metrics help CISOs measure the effectiveness of their cybersecurity initiatives, particularly from a business perspective. CISOs need to understand and employ these metrics to demonstrate that cybersecurity investments not only protect the organization, but also align with business strategies and leadership priorities.
-
They are measurable, especially in the aftermath of a cyberattack, mapping the company's performance against acceptable performance metrics.
-
They are business-focused and examine which business processes were affected, how well they recovered and the impact of the disruption to the firm.
-
They help identify needed improvements in cybersecurity and decision-making.
-
They examine all aspects of a cyberattack for insights into where the firm needs to adapt or change how it responds and recovers from an attack.
-
They are benchmarked with relevant risk-based standards, frameworks and regulations to help identify progress and maturity.
Business, financial and operational considerations all factor into cyber-resilience analyses. Ideally, the outcomes improve cyber-resilience and result in a "new normal" that enhances cybersecurity efforts.
Core cyber-resilience metrics
An array of metrics is available to help senior management understand cyber-resilience. The key is to select the relevant metrics for the situation.
-
Mean time to detect measures the average time it takes for an organization to identify a security threat or incident after it occurs. Rapid MTTD and analysis reduce the likelihood that a cyberattack will disrupt business operations.
-
Mean time to respond measures the average time it takes to contain and neutralize a cyberthreat. Rapid MTTR is essential for minimizing the severity of a cyberattack.
-
Time needed for system recovery determines how quickly the organization can recover IT operations and return to normal business activities.
-
Patch management metrics measure the frequency of patching and number of systems patched. Effective patching ensures cybersecurity resources are optimized for keeping the business operating smoothly.
-
Third-party risk metrics monitor the performance of supply chains and key vendor ecosystems.
-
Business impact metrics measure losses avoided due to resilience initiatives.
-
Recovery time objectives versus actual recovery times metrics illustrate how quickly mission-critical assets are recovered against target recovery times.
-
Recovery point objective metrics assess how long data can be unused before it no longer has value to the enterprise. A short-duration RPO means the risk of lost business or customer data was reduced.
-
Percentage of backed up assets measures how many mission-critical systems, networks and applications are backed up to a secure location and have sufficient availability to minimize the likelihood of a system failure.
-
Compliance metrics measure the level of compliance with security standards, such as ISO 27001 or NIST Special Publication 800-53.
Best practices for implementing cyber-resilience metrics
The process for building a cyber-resilient technology infrastructure includes the following activities.
Identify relevant business performance targets and align metrics
Cybersecurity teams charged with addressing cyber-resilience should understand business mandates, such as uninterrupted availability, compliance and customer trust.
Build resilience using established frameworks
The NIST Cybersecurity Framework and Mitre cyber-resiliency metrics should be high on the list of development tools.
Examine cybersecurity events
Use all relevant metrics related to cyberattack prevention, detection, response and recovery.
Ensure metrics drive positive actions
Use analytics to identify where investments are needed or procedures need to be changed.
Validate metrics
Run simulations or other tests to ensure the metrics are providing useful data.
Balance metrics
Balance technology metrics -- e.g., MTTD and MTTR and business metrics -- e.g., cost of downtime -- to deliver a more inclusive situation analysis.
Discuss third-party and supply chain issues
Address external relationships and supply chains when discussing resilience, as those dependencies can pose risks.
Keep an eye on industry trends
Examine how other enterprises use cyber-resilience metrics to validate compliance and identify improvements.
Establish a process for continuous improvement
Keep metrics current and in sync with business strategies and the risk landscape to address the frequency and severity of cyberattacks.
Ensuring useful metrics
The right metrics translate abstract values into specific data used for decision-making. Conduct these activities to ensure that cyber-resilience metrics deliver actionable results:
-
Identify use. Define how metrics will map to business imperatives such as uptime and compliance.
-
Address the incident lifecycle. Include metrics that address prevention, detection, response, recovery and post-event outcomes.
-
Find the right frameworks. Use specific standards and frameworks to ensure regulatory compliance.
-
Gather data using relevant methods. Many data sources are available, such as incident logs and risk assessments. Automate data gathering when possible.
Reporting cyber-resilience metrics
The data metrics create is of little value unless CISOs can clearly communicate it to the board, CEO or other stakeholders or committees. CISOs must know their audience when presenting to senior management. Use business terms rather than technical jargon, discussing only the most relevant metrics linked to desired outcomes. Report on straightforward outcomes, such as "resolving a cyberattack and recovering business operations in less than one hour." When possible, use visual aids such as dashboards and charts.
The audience will need context, so present trending data that shows how cybersecurity improvements have enhanced business risk management and justified cyber-resilience investments. People respond to stories, so consider presenting a narrative that illustrates how cyber-resilience initiatives have helped the company, such as mitigating a recent cyberattack or saving the company money.
Paul Kirvan, FBCI, CISA, is an independent consultant and technical writer with more than 35 years of experience in business continuity, disaster recovery, resilience, cybersecurity, GRC, telecom and technical writing.








