What is cyber resilience?
Cyber resilience is the ability of a computing system to identify, respond to and recover quickly from a security incident.
The goal of cyber resilience is to enable an organization to continue operating, even directly after adverse cyberevents, such as a cyberattack, natural disaster or a security incident caused by human error. Cyber-resilience capabilities are essential in IT systems, critical infrastructure, business processes, organizations, societies and nation-states. A good cyber-resilience strategy enables an organization to maintain essential business functions or restore them quickly after a cyberincident.
To do this, cyber resilience requires a continuous effort and touches on many aspects of information security, such as disaster recovery (DR), business continuity and computer forensics. Cyber resilience is built up over time and refers to the preparations an organization makes to deal with threats and vulnerabilities, the defenses that have been developed, and the resources available for mitigating a security failure after the fact.
Why should organizations have a cyber-resilience plan?
Organizations should have a cyber-resilience plan in place as cyberthreats are inevitable, and not having a plan in place to deal with them can have devastating consequences -- from prolonged downtime to financial losses.
No matter how strong an organization's cybersecurity practices are, vulnerabilities can still open up due to human error or zero-day vulnerabilities.
A cyber-resilience plan increases an organization's security posture by focusing on its ability to respond to and recover quickly from a cyber threat or incident. An ideal plan can help mitigate potential financial losses, increase end-user trust and reputation, and reduce potential downtimes while also reducing the risks that the organization's infrastructure and data could face.
Key pillars of cyber resilience
The exact components of cyber resilience will differ by company; however, some general components can include the following:
- Cybersecurity. As a part of a cyber-resilience strategy, cybersecurity teams work with different tools and policies to help protect an organization's IT systems -- including hardware and software. Cybersecurity software can monitor, detect and respond to cyberattacks. Organizations can follow cybersecurity frameworks provided by groups such as the National Institute of Standards and Technology (NIST) to implement standardized cybersecurity practices.
- Business continuity. Business continuity is an organization's ability to maintain critical business functions during and after a disaster. Business continuity planning creates a risk management process that helps define a plan to reestablish full function to the organization as quickly and smoothly as possible and helps to prevent interruptions to mission-critical services.
- Risk management. Risk management is the process of identifying, assessing and controlling threats to an organization's capital and operations. These risks can stem from various sources, including malicious actors, strategic management errors, accidents and natural disasters. A successful risk management program, along with a cyber-resilience plan, helps an organization consider the full range of risks it faces.
- Disaster recovery. DR is the set of procedures, policies and tools an organization has in place to respond to and recover from cyberthreats that negatively affect business operations. The goal of having a DR process is to help an organization regain use of critical systems and IT infrastructure as soon as possible after a disaster.
- Incident response. Incident response is an organized and strategic approach to detecting and managing cyberattacks. It focuses on what happens during and after an incident and defines the specific processes for detecting, analyzing and recovering from cybersecurity incidents.
- Encryption. Encryption plays an important role in protecting data, both in transit and at rest. As part of a cyber resilience strategy, encryption ensures that data is only readable to the entity meant to read it. Even if data is accessed or intercepted by a threat actor, it remains unreadable to them.
Comparing cyber resilience vs. cybersecurity
Cybersecurity is the practice of protecting internet-connected systems such as hardware, software and data from cyberthreats. It's used by individuals and enterprises to protect against unauthorized access to user data or systems.
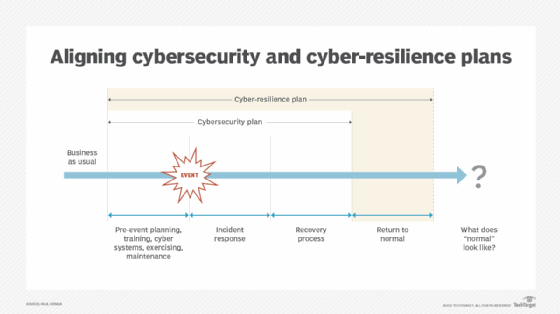
Although they sound similar, cyber resilience and cybersecurity are two separate concepts. While cybersecurity focuses on the active practice of prevention, detection and response to threats, cyber resilience focuses on the organization's ability to identify, respond to and recover from those threats.
The two concepts are not mutually exclusive, however. To strengthen protection against cyberattacks, organizations should implement both cybersecurity and cyber-resilience plans.
How to create a cyber resilience plan
A finalized cyber resilience plan will look different for each organization. Organizations looking to create a cyber resilience plan should outline their overall cyber resilience strategy based on their business strategies and risk appetite.
To help guide the design and implementation of a cyber resilience strategy, organizations can adopt a cyber resilience framework -- or a framework that adheres closely to cyber resiliency. These could include frameworks such as the NIST Cybersecurity Framework, ISO 27001 or MITRE's Cyber Resiliency Engineering Framework. These frameworks consist of structured guidelines and practices that are designed to improve an organization's ability to withstand or recover from cyber threats.
Another key aspect of cyber resilience is to have a deep understanding of risk -- which means going beyond IT planning to make limiting risk exposure an integral part of the strategy. Organizations should focus their resources on the cyber-risks that are likely to have the biggest impact and concentrate on the metrics that provide insight into helping to predict them.
A cyber-resilience framework should be built on a strategy surrounding the following steps, as defined by NIST:
- Identify. Organizations should look for potential security exposure indications proactively. This includes monitoring for potential software vulnerabilities and misconfigured devices.
- Protect. Organizations should build up their infrastructure to deal with the potential for cyberthreats and use cybersecurity tools to help prevent potential harm to critical infrastructure and data.
- Detect. Security tools and processes should be fine-tuned for incident detection and to identify potential risks and irregularities. Tools and processes in use should be able to monitor critical systems for internal, external, malicious or natural threats.
- Respond. Data from any security incident should be collected and analyzed to help organizations make better-informed decisions.
- Recover. To avoid interruption to business, organizations should have systems in place to rapidly restore data and to recover mission-critical systems. For example, this could include keeping a backup of customer data in the cloud, hosted in a different geographic location from the organization.
The cyberthreat landscape is constantly changing, and organizations should be able to adapt to any given circumstance. For example, once an organization recovers from an incident, it should modify its security procedures and design a security strategy to defend against the same issue. Organizations should also be proactive and continually review their security posture.
Cyber resilience is an important aspect of keeping an organization safe from malicious or natural threats. Learn how to build a culture of cyber resilience in the enterprise.