Cryptography attacks: The ABCs of ciphertext exploits
Encryption is used to protect data from peeping eyes, making cryptographic systems an attractive target for attackers. Here are 18 types of cryptography attacks to watch out for.
The following is an excerpt from the Official (ISC)2 Guide to the CISSP CBK, fourth edition, edited by Adam Gordon, CISSP-ISSAP, ISSMP, SSCP. This section from Domain 3 offers a comprehensive overview of the various methods attackers use to crack ciphertext and otherwise exploit cryptography systems.
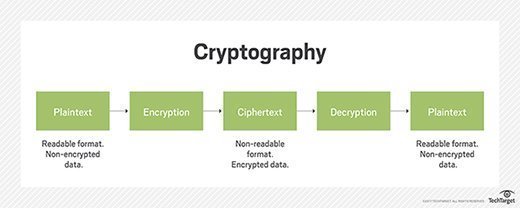
Today’s cryptography is far more advanced than the cryptosystems of yesterday. Organizations are able to both encrypt and break ciphers that could not even have been imagined before human civilization had the power of computers. Today's cryptosystems operate in a manner so that anyone with a computer can use cryptography without even understanding cryptographic operations, algorithms and advanced mathematics. However, it is still important to implement a cryptosystem in a secure manner. Any security system or product is subject to compromise or attack. The following explains common cryptography attacks.
Ciphertext-onIy attack
The ciphertext-only attack is one of the most difficult cryptography attacks because the attacker has so little information to start with. All the attacker starts with is some unintelligible data that he suspects may be an important encrypted message. The attack becomes simpler when the attacker is able to gather several pieces of ciphertext and thereby look for trends or statistical data that would help in the attack. Adequate encryption is defined as encryption that is strong enough to make brute force attacks impractical because there is a higher work factor than the attacker wants to invest into the attack. Moore’s law states that available computing power doubles every 18 months. Experts suggest this advance may be slowing; however, encryption strength considered adequate today will probably not be sufficient a few years from now due to advances in CPU and CPU technologies and new attack techniques. Security professionals should consider this when defining encryption requirements.
Known plaintext
For a known plaintext attack, the attacker has access to both the ciphertext and the plaintext versions of the same message. The goal of this type of attack is to find the link -- the cryptographic key that was used to encrypt the message. Once the key has been found, the attacker would then be able to decrypt all messages that had been encrypted using that key. In some cases, the attacker may not have an exact copy of the message; if the message was known to be an e-commerce transaction, the attacker knows the format of such transactions even though he does not know the actual values in the transaction.
Chosen plaintext
To execute the chosen attacks, the attacker knows the algorithm used for the encrypting, or even better, he may have access to the machine used to do the encryption and is trying to determine the key. This may happen if a workstation used for encrypting messages is left unattended. Now the attacker can run chosen pieces of plaintext through the algorithm and see what the result is. This may assist in a known plaintext attack. An adaptive chosen plaintext attack is where the attacker can modify the chosen input files to see what effect that would have on the resulting ciphertext.
Chosen ciphertext
This is similar to the chosen plaintext attack in that the attacker has access to the decryption device or software and is attempting to defeat the cryptographic protection by decrypting chosen pieces of ciphertext to discover the key. An adaptive chosen ciphertext would be the same, except that the attacker can modify the ciphertext prior to putting it through the algorithm. Asymmetric cryptosystems are vulnerable to chosen ciphertext attacks. For example, the RSA algorithm is vulnerable to this type of attack. The attacker would select a section of plaintext, encrypt it with the victim’s public key, then decrypt the ciphertext to get the plaintext back. Although this does not yield any new information to the attacker, the attacker can exploit properties of RSA by selecting blocks of data, when processed using the victim’s private key, yields information that can he used in cryptanalysis. The weakness with asymmetric encryption in chosen ciphertext attacks can be mitigated by including a random padding in the plaintext before encrypting the data. Security vendor RSA Security recommends modifying the plaintext by using a process called optimal asymmetric encryption padding (OAEP). RSA encryption with OAEP is defined in PKCS #1 v2.1.
Differential cryptanalysis
Also called a side-channel attack, this more complex attack is executed by measuring the exact execution times and power required by the crypto device to perform the encryption or decryption. By measuring this, it is possible to determine the value of the key and the algorithm used.
Linear cryptanalysis
This is a known plaintext attack that uses linear approximations to describe the behavior of the block cipher. Linear cryptanalysis is a known plaintext attack and uses a linear approximation to describe the behavior of the block cipher. Given sufficient pairs of plaintext and corresponding ciphertext, one can obtain bits of information about the key, and increased amounts of data will usually give a higher probability of success. There have been a variety of enhancements and improvements to the basic attack. For example, there is an attack called differential -- linear cryptanalysis, which combines elements of differential cryptanalysis with those of linear cryptanalysis.
Implementation attacks
Implementation attacks are some of the most common and popular attacks against cryptographic systems due to their ease and reliance on system elements outside of the algorithm. The main types of implementation attacks include:
Side-channel attacks are passive attacks that rely on a physical attribute of the implementation such as power consumption/emanation. These attributes are studied to determine the secret key and the algorithm function. Some examples of popular side channels include timing analysis and electromagnetic differential analysis.
Fault analysis attempts to force the system into an error state to gain erroneous results. By forcing an error, gaining the results and comparing it with known good results, an attacker may learn about the secret key and the algorithm.
Probing attacks attempt to watch the circuitry surrounding the cryptographic module in hopes that the complementary components will disclose information about the key or the algorithm. Additionally, new hardware may be added to the cryptographic module to observe and inject information.
Replay attack
This attack is meant to disrupt and damage processing by the attacker, through the resending of repeated files to the host. If there are no checks such as time-stamping, use of one-time tokens or sequence verification codes in the receiving software, the system might process duplicate files.
Algebraic
Algebraic attacks are a class of techniques that rely for their success on block ciphers exhibiting a high degree of mathematical structure. For instance, it is conceivable that a block cipher might exhibit a group structure. If this were the case, it would then mean that encrypting a plaintext under one key and then encrypting the result under another key would always be equivalent to single encryption under some other single key. If so, then the block cipher would be considerably weaker, and tile use of multiple encryption cycles would offer no additional security over single encryption.
Rainbow table
Hash functions map plaintext into a hash. Because the hash function is a one-way process, one should not be able to determine the plaintext from the hash itself. To determine a given plaintext from its hash, refer to these two ways to do that:
1. Hash each plaintext until matching hash is found; or
2. Hash each plaintext, but store each generated hash in a table that can used as a look up table so hashes do not need to be generated again. A rainbow table is a lookup table of sorted hash outputs. The idea here is that storing precomputed hash values in a rainbow table that one can later refer to saves time and computer resources when attempting to decipher tile plaintext from its hash value.
Frequency analysis
This attack works closely with several other types of attacks. It is especially useful when attacking a substitution cipher where the statistics of the plaintext language are known. In English, for example, some letters will appear more often than others will, allowing an attacker to assume that those letters may represent an E or S.
Birthday attack
Because a hash is a short representation of a message, given enough time and resources, another message would give the same hash value. However, hashing algorithms have been developed with this in mind so that they can resist a simple birthday attack. The point of the birthday attack is that it is easier to find two messages that hash to the same message digest than to match a specific message and its specific message digest. The usual countermeasure is to use a hash algorithm with twice the message digest length as the desired work factor (e.g., use 160-bit SHA-1 to have it resistant to 280 work factor).
Social engineering for key discovery
This is the most common type of attack and usually the most successful. All cryptography attacks rely to some extent on humans to implement and operate. Unfortunately, this is one of the greatest vulnerabilities and has led to some of the greatest compromises of a nation’s or organization’s secrets or intellectual property. Through coercion, bribery or befriending people in positions of responsibility, spies or competitors are able to gain access to systems without having any technical expertise.
Dictionary attack
The dictionary attack is used most commonly against password files. It exploits the poor habits of users who choose simple passwords based on natural words. The dictionary attack merely encrypts all of the words in a dictionary and then checks whether the resulting hash matches an encrypted password stored in the SAM file or other password file.
Brute force
Brute force is trying all possible keys until one is found that decrypts the ciphertext. This is why key length is such an important factor in determining the strength of a cryptosystem. With DES only having a 56-bit key, in time the attackers were able to discover the key and decrypt a DES message. This is also why SHA-256 is considered stronger than MD5; because the output hash is longer and, therefore, more resistant to a brute force attack. Graphical Processor Units (GPU) have revolutionized brute force hacking methods. Where a standard CPU might take 48 hours to crack an eight character mixed password, a modern GPU can crack it in less than 10 minutes. CPUs have a large number of arithmetic/logic units and are designed to perform repetitive tasks continuously. These characteristics make them ideal for performing brute force attack processes. Due to the introduction of CPU-based brute force attacks, many security professionals are evaluating password length, complexity and multifactor considerations.
Reverse engineering
Reverse engineering is one of the most common cryptography attacks. A competing firm buys a crypto product from another firm and then tries to reverse engineer the product. Through reverse engineering, it may be able to find weaknesses in the system or gain crucial information about the operations of the algorithm.
Attacking the random number generators
This attack was successful against the SSL installed in Netscape several years ago. Because the random number generator was too predictable; it gave the attackers the ability to guess the random numbers so critical in setting up initialization vectors or a nonce. With this information in hand, the attacker is much more likely to run a successful attack.
Temporary files
Most cryptosystems will use temporary files to perform their calculations. If these files are not deleted and overwritten, they may be compromised and lead an attacker to the message in plaintext.
CISSP® is a registered mark of (ISC)².





