
Getty Images/iStockphoto
Use Teams compliance controls to meet security requirements
Administrators have a lot of flexibility when configuring Microsoft Teams to meet their organizations' security and compliance targets. Limiting chat access is just one tactic.
Many organizations have deployed Microsoft Teams to support remote collaboration and business workflows. But using Teams and managing the reams of data generated by users, from chats to shared files, also means ensuring the platform meets your organization's security and compliance requirements. That's even more important for companies that allow external users to log into Teams sessions.
Fortunately, administrators have a variety of ways to implement security and Teams compliance policies mandated by their organizations. The first step, however, is to outline the compliance requirements specific to the particular business -- say, a hospital where patient information can't be shared to any nonclinical or unauthorized user, or a financial institution whose sensitive information can't fall into the wrong hands -- and map those needs to the security controls within Teams. Let's examine some of those controls and how they might be put into operation.
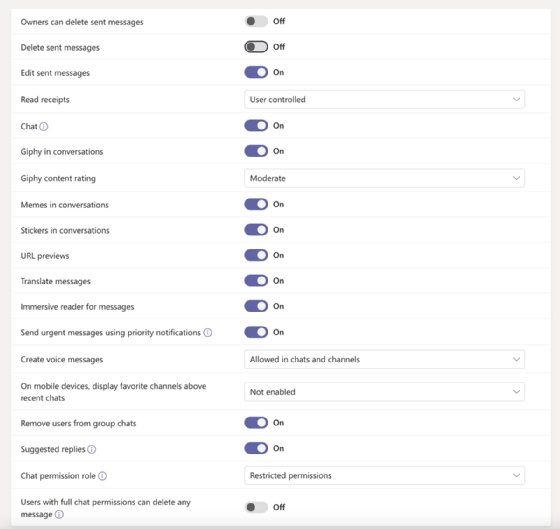
Messaging policies. Using the messaging policies available in Teams Admin portal, as shown in Figure 1, administrators can limit several chat features. These controls enable organizations to fine-tune how users can share information within chat sessions.
Membership and access to Teams and its channels. This feature governs how users can access different teams, created either independently or as part of a Microsoft 365 group. Within either the Office 365 or Teams admin portals, administrators or teams/group owners can mandate that only invited users have access to content shared in specific teams or channels. In addition, owners can decide if they want to elevate their members' access by promoting them to owners, which in turn would permit them to invite other users to see and interact with the content within their teams or channel.
Sensitivity and content labeling. Sensitivity labeling is a way to categorize content based on specific business requirements. For example, a "confidential content" tag can be applied to information that can only be shared within a limited number of people, while "PHI" signifies patient health information that must adhere to HIPAA requirements. Once labels are defined within the Compliance admin portal, administrators can ensure content protection by enabling policies to force the additional restrictions.
Information barriers. For those use cases where restrictions around communication and searches is required, the IB -- or information barrier -- policy allows Teams administrators to define exactly how users can contact or communicate with others. R&D staff, for instance, could be barred from sharing information with any external or internal user other than members of their own department.
Identity management with 2FA. Other controls can be applied outside of Teams, such as multifactor authentication (MFA) or two-factor authentication (2FA). This is part of Office 365's identity management dashboard, and it allows admins to require participants use MFA when signing into Teams.
Device compliance. Organizations that use Microsoft Intune for mobile device management can set up policies that ensure devices running the Teams app meet security and compliance targets established by IT. A company, for example, could use the app to mandate that passcodes are required, antivirus software is used or that users' devices run the most recent operating software.
Microsoft Teams will continue to be the preferred communication and collaboration platform for many Office 365 subscribers. For system administrators, the ability to oversee security and Teams compliance policies from a single portal -- and have them extended to other Office 365 apps, such as OneDrive and Exchange Online -- is a key benefit.







