
Getty Images/iStockphoto
Aligning cybersecurity with ESG goals: A guide for IT leaders
An aligned cybersecurity with ESG strategy can improve sustainability, governance and risk management while addressing regulatory scrutiny and balancing environmental impacts.
Cybersecurity has evolved from an IT concern to a core business risk and trust factor, and environmental, social and governance practices have been a key response to this evolution.
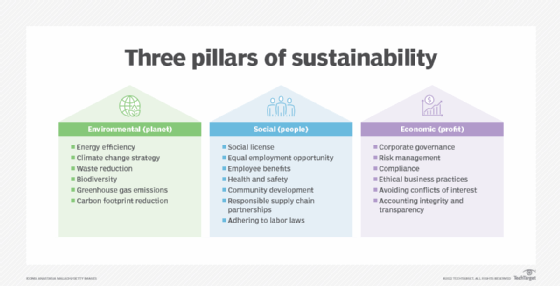
Integrating cybersecurity into an organization's environmental, social and governance responsibilities demonstrates its central role in modern ESG strategy. In particular, cybersecurity and ESG work together in the following ways:
- Environmental. Cybersecurity protects the systems managing smart grids, renewable energy and environmental monitoring, helping prevent disruptions to sustainability efforts.
- Social. Cybersecurity protects personal data and privacy, which directly affects people.
- Governance. Cybersecurity enhances oversight and risk management, promoting accountability and transparency at the leadership level.
Effective cybersecurity practices are part of responsible corporate behavior. Organizations often include cyber risk in ESG reporting, oversight, incident response and privacy controls. Investors also view cyber maturity as a signal of resilience and solid governance.
Additionally, organizations are extending hardware and platform lifecycles to reduce costs and e-waste. These efforts often conflict with common cybersecurity practices and requirements, as aging systems often lack support for modern security controls and updates.
Without effective alignment, sustainability initiatives can inadvertently increase cyber risks. For example, IT teams may have to choose between reducing environmental impact and maintaining resilience.
To achieve this integration, IT leaders must move from siloed approaches to a cohesive strategy that unites sustainability and security within broader IT governance frameworks and balances resilience, efficiency and environmental responsibility. This way, cybersecurity becomes an ESG enabler rather than a competing priority.
Why align cybersecurity and ESG strategies?
ESG has shifted from a compliance-oriented exercise to a core business and investment priority, with executive teams holding IT leaders accountable for ESG outcomes. Digital infrastructure plays a central role in sustainability initiatives, meaning technology decisions directly affect ESG compliance and its long-term value.
Organizations also face increasing scrutiny around ESG practices. For example, regulators are expanding ESG compliance frameworks to include cyber risk and transparency in governance. Investors have also begun to evaluate cybersecurity posture as part of ESG reporting and risk reviews. This has made it even more crucial to align cybersecurity and ESG strategies.
An aligned strategy considers the following points:
- Lifecycle extension vs. risk exposure. Extending hardware and platform lifecycles reduces e-waste and supports sustainable IT goals, but aging systems increase vulnerabilities, patching complexity and attack surfaces.
- Cybersecurity as a governance pillar. Cybersecurity is central to the governance aspect of ESG, reinforcing accountability, risk management and operational resilience.
- Regulatory and investor scrutiny. ESG reporting now includes cyber risk disclosures, incident transparency and resilience metrics within ESG frameworks.
- The overall effects of misalignment. Failure to align security and ESG results in compliance gaps, amplified breach risk and eroded stakeholder trust.
Cyber incidents hurt brand reputation and shareholder confidence, and the rising frequency and sophistication of attacks amplify the consequences of ineffective security. Organizations that fail to integrate ESG into cybersecurity practices risk regulatory scrutiny, financial penalties and reputational damage.
Modern security requirements and sustainability mandates
IT leaders must operationalize alignment by coordinating planning across infrastructure, security and sustainability initiatives.
Key areas to evaluate include the following:
- Lifecycle planning. Balance longevity with security viability. Policy-driven thresholds can prevent system lifecycles from becoming too risky or costly to maintain while keeping older systems in use for longer.
- Secure patch management. Automate patching across extended lifecycles to reduce vulnerabilities, operational overhead and energy use. IT leaders can prioritize patches based on exploit risks and business impact. Legacy systems should be segmented, virtualized or wrapped with compensating controls if patching is limited.
- OS upgrade strategies. Ensure OSes perform, are supported and secure, even as refresh cycles slow, and adhere to supported OSes to avoid unpatchable vulnerabilities. Additionally, IT leaders should evaluate lightweight or energy-efficient OS alternatives where appropriate.
- Hardware refresh timing. A shift from time-based to risk- and performance-based refresh cycles better incorporates security risk scoring, energy efficiency and total cost of ownership. This often requires risk-based asset prioritization.
- Risk-based asset prioritization. Identify systems that require earlier upgrades vs. lower-risk assets that can be safely extended. IT leaders can classify these assets based on data sensitivity, exposure level and business criticality, and apply zero-trust principles to mitigate risk from extended use devices.
- Supply chain vendor consideration. Evaluate vendors on ESG compliance and security posture to reduce third-party risk, and include security and ESG criteria in procurement and vendor selection processes. For example, some organizations may favor partners with circular economy initiatives, such as refurbishment and recycling. Additionally, organizations can require transparency into vendors' security controls, patching policies and sustainability commitments.
- Secure decommissioning and asset disposition. Track asset disposition and maintain documentation as part of ESG reporting and e-waste standards. This may include secure data destruction protocols for retired assets to prevent data leakage.
To be effective, this alignment requires clear, measurable objectives and consistent metrics to support it and create a foundation for continuous improvement.
Sustainability and security metrics
Organizations must unify ESG reporting and cybersecurity metrics to create a complete view of risk and performance.
Essential practices to balance ESG and security include the following:
- Integrated KPI frameworks. Align cybersecurity KPIs -- for example, vulnerability remediation time -- with ESG goals, like asset lifespan and energy consumption.
- E-waste reduction without risk. Track device reuse and recycling, and securely decommission retired assets.
- Risk exposure vs. sustainability goals. Quantify trade-offs between extended usage and increased attack surface.
- Governance models. Embed cybersecurity into IT governance structures alongside ESG oversight metrics.
- Transparent ESG reporting. Include cybersecurity posture, incidents and resilience measures for stakeholders.
Metrics can be defined by category and include the following KPIs.
Asset lifecycle and sustainability
- Average device lifecycle in years.
- Percent of assets that operate beyond standard lifecycles.
- E-waste reduction rate, as a percentage.
- Percent of IT assets reused or refurbished.
- Carbon emissions per endpoint, in kilograms of CO2 per device per year.
Vulnerability and patch management
- Mean time to patch.
- Patch compliance rate, as a percentage.
- Percent of unpatchable or unsupported systems.
- Critical vulnerability exposure window in days.
- Automated patch coverage, as a percentage.
Risk and exposure
- Risk score per asset.
- Percent of high-risk legacy systems.
- Attack surface size, or the number of exposed endpoints.
- Zero trust coverage, as a percentage.
- Third-party risk rating, or average vendor score.
Energy and efficiency
- Energy consumption per IT asset, in kilowatt hours per device per year.
- Data center or endpoint energy efficiency ratio.
- Percent of workloads running on energy-efficient infrastructure.
- Security tooling energy footprint, in kilowatt hours per year.
- Workload consolidation rate, as a percentage.
Governance and ESG compliance
- Cybersecurity metrics included in ESG reporting, as a percentage.
- Audit findings related to cybersecurity and ESG.
- Policy compliance rate, as a percentage.
- Board-level cybersecurity reporting frequency.
- Percent of IT decisions aligned with ESG criteria.
Incident and resilience KPIs
- Number of security incidents linked to legacy systems.
- Mean time to detect.
- Mean time to respond.
- Incident disclosure time.
- Business downtime from cyber incidents, in hours per year.
- Resilience score, or a composite KPI.
Secure decommissioning and data protection KPIs
- Percent of decommissioned assets with verified data wipe.
- Time to decommission assets, in days.
- Chain-of-custody compliance rate, as a percentage.
- Improper disposal incidents.
With these metrics, IT leaders can establish a baseline and monitor progress toward a more resilient cybersecurity strategy. These indicators also support credible auditability and transparent reporting for business partners, regulatory bodies and investors.
What IT leaders can do today
Organizations that want to lead in both cybersecurity and ESG should take immediate action.
Use the following steps to align cybersecurity with ESG:
- Conduct regular risk assessments. Evaluate aging infrastructure, lifecycle decisions and ESG-driven changes for their security and sustainability impacts.
- Implement transparent reporting mechanisms. Integrate cybersecurity incidents into ESG reporting for accountability and compliance.
- Collaborate across functions. Align IT, security and ESG teams to create shared goals, metrics and decision-making frameworks.
- Use AI and automation. AI-driven tools can improve threat detection, automate patching and optimize energy-efficient operations.
- Adopt a secure-by-sustainability mindset. Treat sustainability and security as mutually reinforcing priorities, not trade-offs or competing standards.
Cybersecurity and ESG are converging priorities rather than competing initiatives. Organizations that integrate cybersecurity into their ESG strategy can reduce risk and position themselves as resilient, responsible leaders in a rapidly evolving digital landscape.
Damon Garn owns Cogspinner Coaction and provides freelance IT writing and editing services. He has written multiple CompTIA study guides, including the Linux+, Cloud Essentials+ and Server+ guides, and contributes extensively to TechTarget Editorial, The New Stack and CompTIA Blogs.








