How to recover from a ransomware attack
With a ransomware recovery plan, organizations can act quickly to prevent data loss without descending into chaos. Learn the six steps to incorporate into your plan.
How an organization recovers in the days following a ransomware attack may affect its viability in the long run. An organization can quickly resume normal operations with a ransomware recovery plan in place.
Deploying a variety of cybersecurity tools and platforms, such as endpoint security, email security, next-generation firewalls and security awareness training, should reduce the risk of ransomware infiltration. If ransomware does infect an organization's system, however, the security team should immediately deploy a ransomware recovery plan.
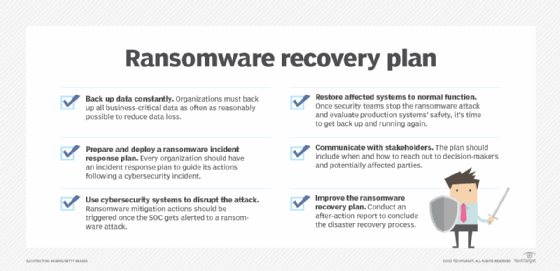
The ransomware recovery plan should include how the organization prepares for attacks, how to handle an in-progress attack and what to do in the aftermath. Include the following steps in the plan:
- Back up data constantly.
- Prepare and deploy a ransomware incident response plan.
- Use cybersecurity systems to disrupt the attack.
- Restore affected systems to normal function.
- Communicate with stakeholders.
- Improve the ransomware recovery plan.
1. Back up data constantly
Organizations must back up all business-critical data as often as reasonably possible to reduce data loss. Data backups are a necessity to recover following a ransomware attack. Confirm through regular testing that the backups are viable and that restoring from backups works. To ensure data backups remain secure, organizations should have data protection capabilities in place.
This article is part of
What is ransomware? Definition and complete guide
Consider isolating at least one data backup from the internet. Virtual air gapping ensures data isn't directly reachable by systems in an organization's production environments. True air gapping is another option: The backup medium, or the whole backup system, is physically disconnected from the enterprise network -- creating a literal air gap between them. Air-gapped backups are not vulnerable to active corruption by ransomware. That said, organizations should still evaluate any data backups before deploying them to production environments.
2. Prepare and deploy a ransomware response plan
Every organization should have a general-purpose incident response plan (IRP) to guide their actions in the event of a cybersecurity incident. Some organizations develop a ransomware-specific incident response plan. A ransomware IRP details immediate measures for the security operations center (SOC), network operations center and system admins to take in response to a known or strongly suspected ransomware event.
Steps on a ransomware IRP include the following:
- Confirm the attack is ransomware.
- Gather the incident response team.
- Evaluate the incident.
- Contain the ransomware.
- Mitigate the ransomware.
- Perform a digital forensics investigation.
A ransomware IRP is only useful if it's deployed. Far too often, IRPs sit unused during incidents. The incident response team should also periodically evaluate the IRP's fit to current infrastructures, staff and processes.
Alongside reviewing the ransomware IRP, the incident response team should conduct regular drills and tabletop exercises to ensure everyone involved understands the plan, follows it and can improve upon the plan after trying to execute on it.
3. Use cybersecurity systems to disrupt the attack
Ransomware mitigation actions should be triggered once the SOC gets alerted to a ransomware attack. While part of the IRP, this step is important enough to be its own separate action in the ransomware recovery plan, too.
Cybersecurity systems should work to contain the ransomware and mitigate damage from it. The first move should be to tighten cybersecurity where relevant. Security teams should ensure the network automatically quarantines endpoints behaving suspiciously, lock down network segments and block command-and-control connections. Automate security mitigation and remediation methods as much as possible, so the security teams do not have to stop ransomware entirely manually.
4. Restore affected systems to normal function
Once security teams stop the ransomware attack and evaluate production systems' safety, it's time to get back up and running again. Some steps to resume business functions include the following:
- Deploy backup data.
- Wipe and restore endpoints.
- Delete and replace central system instances.
- Attempt data recovery, as necessary.
- Scan restored data for infections.
5. Communicate with stakeholders
While they restore data and resume normal business functions, organizations must communicate internally and, potentially, externally. The ransomware recovery plan should include when and how to reach out to decision-makers and potentially affected parties, which include employees, executive leadership, third-party vendors and customers.
The plan should define decision points so security teams know who to contact based on the scope and speed of the infection. The plan should specify who makes the decisions, how to reach those people and who their alternates are. Also include who to inform of each decision, how and when to inform them, and the expected business effects of decisions.
External communication includes reporting the attack to law enforcement. In the U.S., organizations can notify CISA, their local FBI field office, the Secret Service or the Internet Crime Complaint Center. The law enforcement agency can provide assistance, if requested.
6. Improve the ransomware recovery plan
Conduct an after-action report to conclude the disaster recovery process. This report should be a full, honest and blame-free review of everything done and not done in response to the ransomware incident.
Review what worked and what didn't in the IRP. Add anything missing and trim out extraneous processes that slowed response efforts. Use the revised recovery plan in the next round of drills or tabletop exercises and war games.
The military saying is, "No plan survives first contact with the enemy," but -- on the assumption that a perfect plan is not possible -- no plan should. Retrospective analysis of the incident response turns that truism from a bug into a feature.
It is not inevitable that every organization will experience a successful ransomware attack. It is inevitable that those that fail to plan for one will be at a serious disadvantage when faced with cybercriminals.








