supply chain security
Supply chain security is the part of supply chain management that focuses on the risk management of external suppliers, vendors, logistics and transportation. Its goal is to identify, analyze and mitigate the risks inherent in working with other organizations as part of a supply chain. Supply chain security involves both physical security relating to products and cybersecurity for software and services.
Because supply chains can vary greatly from group to group, and many different organizations may be involved, there is no single set of established supply chain security guidelines or best practices. A complete supply chain security strategy requires following risk management principles and cyberdefense in depth. It also takes into account protocols set by government agencies like the Department of Homeland Security or customs regulations for international supply chains.
Physical supply chain security and integrity
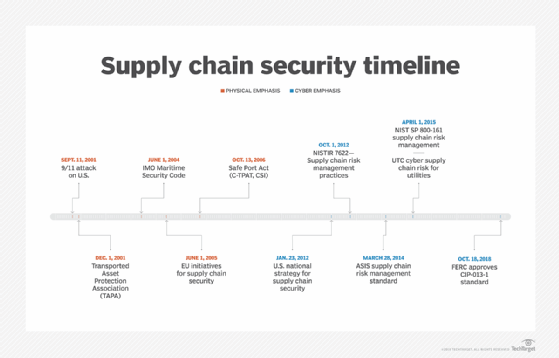
In the past, supply chain security primarily focused on physical security and integrity. Physical threats encompass risks with internal and external sources, such as theft, sabotage and terrorism.
Organizations often mitigate physical attacks by tracking shipments and checking regulatory paperwork. Additionally, vendors could be required to secure shipments following specific quality guidelines, and a business could employ several vendors to ensure a steady supply of commodity products.
External auditors or inspectors could go to a factory, and businesses could run background checks on personnel as well. Shipments could also be logged, guarded and checked prior to and after shipping to stop tampering or theft.
Cyberthreats and supply chain security
More recently, cyberthreats have risen to the forefront of supply chain security concerns. Cyberthreats refer to vulnerabilities in IT and software systems, like malware attacks, piracy, unauthorized ERP access and unintentional or maliciously injected backdoors in the purchased, Open Source or proprietary software used by organizations.
Supply chain security here primarily involves minimizing risks from using software developed by another organization, and securing organizational data accessed by another organization in your supply chain. Organizations cannot take for granted that the software that they use or purchase is secure.
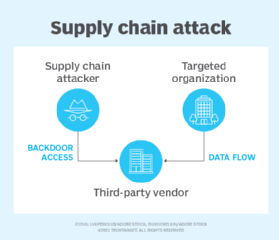
Because close collaboration is often required between businesses, suppliers and resellers, computer networks may become intertwined or sensitive data shared. This can result in a breach of one organization affecting many. Instead of attacking the target directly, a cybercriminal may attack a weaker organization in the target's supply chain and use that access to meet their goals.
Many are responding to recent supply chain attacks such as the SolarWinds attacks by, for example, reducing reliance on foreign suppliers and building primarily domestic supply chains. Some companies are moving production out of foreign factories to domestic ones as well.
Hewlett Packard Enterprise has released a server product line that uses a trusted supply chain for all of its components, for example. Also, the Chinese government has ordered that its ministries stop using foreign-made hardware and software by 2022.
Supply chain security best practices
Supply chain security touches on many areas, and will vary greatly from organization to organization. Risk management principles can guide the strategy to identify threats or potential issues and implement appropriate mitigations. No single set of best practices can cover every situation.
An in-depth defense strategy can greatly improve overall supply chain security. Best practices for supply chain security include:
- Log and track shipments. Use automated notifications for the sender and receiver.
- Use locks and tamper-evident seals during shipping.
- Inspect factories and warehouses.
- Require background checks on employees.
- Use accredited or certified suppliers.
- Perform security strategy assessments with local laws and governance policies in mind.
- Perform penetration and vulnerability testing on partners with which you share data.
- Authenticate all data transmission and identify requestors.
- Use permissions or role-based access to data.
- Require minimum cybersecurity or specific best practice baselines of vendors and resellers.
- Use licensed third-party auditors to certify potential partners.
- Train employees to be alert to changes and inconsistencies.
- Regularly audit open source and vendor source code.
- Restrict third-party programs' access and permissions.
- Use network level scanning, behavioral analysis and intrusion detection to identify potential breaches.
- Have a response plan in place for quickly acting on discovered threats.
- Consult governmental guidelines and regulations appropriate for your region.
By applying the mitigations best suited to its business sector, an organization can greatly improve its supply chain security posture.
Notable supply chain breaches
This list describes some notable supply chain security breaches:
1959: The CIA intercepted a USSR lunar probe as it was being shipped. It was able to completely disassemble, document and reassemble it back into its shipping crate in under 24 hours without leaving any evidence of tampering.
2014: Hackers obtained third-party vendor credentials to Home Depot's credit card terminals. This enabled them to steal an estimated 56 million credit and debit card numbers.
2020: A suspected Russian agency injected malicious backdoor code as an advanced persistent threat into the Orion systems management software made by SolarWinds. Referred to as Sunburst and Supernova, these exploits led to the breach of thousands of companies and government agencies, exposing sensitive data and more.
2021: An unknown party placed a backdoor in the open source PHP Git server, but it was caught before it was published and distributed. This breach could have opened up millions of web servers to hackers.
Importance of supply chain security
Supply chain security should be a high priority for organizations, as a breach within the system could damage or disrupt operations. Vulnerabilities within a supply chain could lead to unnecessary costs, inefficient delivery schedules and a loss of intellectual property. Additionally, delivering products that have been tampered with or are unauthorized could be harmful to customers and lead to unwanted lawsuits.
Security management systems can help protect supply chains from physical and cyber threats. While threats cannot be completely erased, supply chain security can work towards a more secure, efficient movement of goods that can recover rapidly from disruptions.






