What is network scanning? How to, types and best practices
Network scanning is a procedure for identifying active devices on a network by employing a feature or features in the network protocol to signal to devices and await a response. Most network scanning is used to monitor and manage networks, but scanning can also be used to proactively identify vulnerabilities that cyberattackers could exploit.
Many different network scanning tools are available, including open source tools and commercial network scanning products. Different platforms come with different functions, so it is important to choose a tool with the right features for an organization's needs.
How does network scanning work?
The specific protocol features used in scanning depend on the network. for Internet Protocol (IP) networks, scanning normally sends a simple message -- a ping, for example -- to each possible IP address in a specified range. If a response to the ping is received, the network scanner then uses another protocol to obtain data on the devices. This is referred to as active scanning.
By contrast, passive network scanning involves continuously monitoring network traffic for potential risks, such as malicious code, and flagging potential issues for further analysis.
In monitoring and management systems, network administrators routinely use scanning for three management functions:
- To use network discovery functionality to identify and establish an inventory of network users.
- To determine the state of systems and devices.
- To take a further inventory of network elements that are compared against a list of expected devices as a metric of network health.
Cybercriminals use the same tools and protocols as network admins to scan potential targets. In a malicious scenario, an attacker first obtains the IP address range assigned to a company using the domain name system or the WHOIS protocol. Addresses within that range are scanned to look for servers, operating systems, system architecture and the services. The attacker then attempts to access ports that are open and not properly secured to breach the target systems and applications.
Why is network scanning important?
Considering the volume of cyberthreats that occur daily -- and the breadth of potential network vulnerabilities -- scanning is an important part of maintaining a network's health and protecting it from cyberattacks. It's an essential network security tool and should be performed regularly. Threats can materialize in an instant, and network scanning plays a significant role in identifying and troubleshooting potential security vulnerabilities and threats.
The key to effective network scanning is to perform it often, even though network performance might be degraded slightly while scanning is in progress. These tools provide a detailed network map with the following information:
- An inventory of all devices connected to the network.
- Data on key entry points, such as ports.
- Identification of suspicious packets traversing the network.
- Performance data displayed on dashboards.
- Reports on network status.
In short, scanning helps cybersecurity and network security administrators stay ahead of hackers and other threat actors.
Network scanning steps
The following five steps are included in most network scan processes:
- Inventory. First, the scanning tools survey the network to create an inventory of all connected devices.
- Network map. If the function is available, the tool can prepare a network topology map. Nmap, which is short for Network Mapper, is a command-level port scanning tool used to first identify what's on the network and create a map of the devices. This open source tool can scan large networks with diverse features; identify active and idle hosts or ports; and evaluate network perimeters -- such as firewalls and intrusion detection and intrusion prevention systems -- and other parameters.
- Health and vulnerability check. Next, a protocol called Address Resolution Protocol examines network addresses at primary and subnet levels for suspicious activity. The Internet Control Message Protocol is used for a wider scan, such as systems in other geographic locations. Other more advanced protocols are available to gather detailed data on the network's health and to identify potential vulnerabilities.
- Reporting. Data from scanning is often presented on a dashboard in real time, with specific parameters highlighted and suggestions for mitigating attacks. Scanning systems can also prepare documented reports for auditing.
What types of network scans are available?
Scans fall into two basic categories: active and passive. They can also be categorized into more specialized functions:
- Host scanning. Host systems are among the key targets for hackers. As a result, it's important to scan all host systems and determine their status. This can be done by sending a ping to all IP addresses, which prompts the host to send a return message and, with it, its status. Hosts that do not reply get placed on a list of vulnerable targets. Hackers regularly use host scanning to identify candidates for exploitation.
- Port scanning. A port scanner identifies ports that might be malfunctioning or compromised. The scan sends packets to various ports and examines the responses when trying to connect to a service running on a port. Hackers also use port scanning to identify potential victims.
- Network scanning. This scan examines IP addresses and identifies operating systems and devices connected to the network. It can also generate a network map.
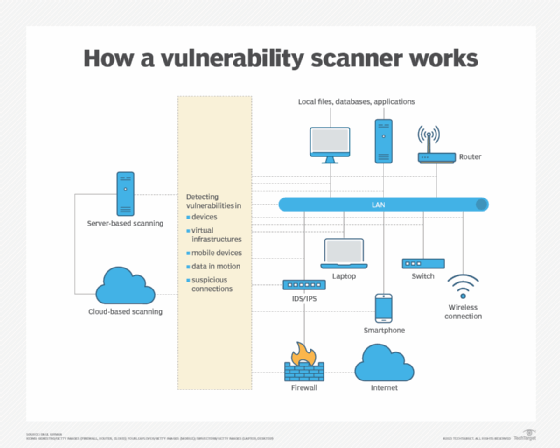
- External vulnerability scans. These scans look for flaws and weaknesses in the network, such as misconfigured or outdated firewalls and security systems, open ports, devices that haven't been properly patched and insecure internet of things endpoints. Vulnerability scanners evaluate the network and network devices from a hacker's perspective.
- Total assessment scan. This scan looks at devices on every IP address and examines them for a variety of conditions, such as overall security status, patching status, last time of use, presence of antivirus software and presence of endpoint detection and response systems.
- Penetration testing. Sometimes called ethical hacking, penetration or pen testing attempts to simulate an attack by bypassing existing perimeter security measures, searching the network for potential vulnerabilities, identifying exploitable systems and data, and performing a detailed risk assessment of the network. It's advisable to get approvals from users and clients before performing a pen test.
Network scanning best practices
Several practices are recommended to obtain the best results from network scanning:
- Regularly inspect internal and external devices in the network infrastructure.
- Establish a documentation process that can be used for troubleshooting, security assessment and planning, status report generation and creating audit report evidence.
- Prioritize scanning based on the criticality of each device to the organization.
- Establish a regular schedule of frequent scanning.
- Automate scanning at predetermined times or conditions if the tool used allows this.
- Regularly review and update scanning parameters to minimize false positives and false negatives.
Find out more about how to deal with the challenges of monitoring and maintaining an enterprise network.






