What is supply chain risk management (SCRM)?
Supply chain risk management (SCRM) is the coordinated efforts of an organization to help identify, monitor, detect and mitigate threats to supply chain continuity and profitability.
The supply chain is a network of companies and activities involved in the manufacturing and distribution of goods and services. With SCRM, possible risks, such as natural disasters, geopolitical upheavals, pandemics, cyberattacks and supplier failures, are assessed. By identifying and assessing these risks, organizations can build mitigation strategies to manage and reduce the effect of disruptions on their operations and bottom line.
Why does SCRM matter?
SCRM has become an important business imperative in the volatile global marketplace. It safeguards organizations against costly disruptions that can affect business operations, finances and reputation.
By systematically identifying, assessing and mitigating potential threats across the supply network, SCRM lets businesses maintain business continuity during unexpected events, such as natural disasters, geopolitical tensions, supplier failures and cybersecurity breaches. The COVID-19 pandemic highlighted SCRM's importance, as companies with solid risk management frameworks were more resilient than ones without frameworks, which struggled with the disruptions.
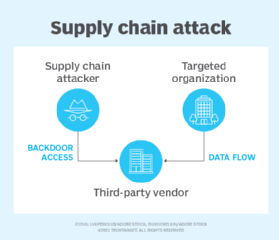
Cybersecurity SCRM (C-SCRM) takes SCRM a step further by addressing the cybersecurity risks introduced through third-party vendors, software providers and hardware manufacturers. The compromise of even one component or partner can leave an organization vulnerable to data breaches, intellectual property theft and operational disruptions.
C-SCRM is especially critical in today's digital landscape, where software and firmware vulnerabilities are often exploited before they're detected and third-party access points frequently pose the greatest cybersecurity risks. In addition, nation-state actors are increasingly targeting supply chains to infiltrate secure environments.
Beyond crisis prevention and cyber-risk management, SCRM provides enhanced visibility into supply chain operations, improved decision-making capabilities, regulatory compliance assurance and the ability to optimize resources.
What risks affect supply chain processes?
Threats to the supply chain can affect business continuity by inducing risk factors, such as cost volatility, material shortages, supplier financial issues and failures, and natural and humanmade disasters.
According to the National Institute of Standards and Technology, examples of risks to the supply chain include counterfeiting, tampering, theft, introduction of malicious software and hardware, and substandard manufacturing and development procedures. SCRM strategies and software help an organization foresee potential issues and adapt to those risks and unforeseeable supply chain disruptions as quickly and efficiently as possible.
Supply chain risks can come from both internal and external factors.
Internal supply chain risks
Internal supply chain risks originate from inside a company and can cause operational or supply chain disruptions. These risks are within the organization's control or influence, and there are opportunities to mitigate and manage them. The following are examples of internal supply chain risks:
- Manufacturing risks. Interruptions and disruptions in internal procedures can result in quality failures where products fail to meet their specifications or their performance is subpar.
- Business risks. Business risks arise from changes to key employees, management, reporting structures or operational protocols, such as the interactions among suppliers, customers and procurement.
- Mitigation risks. Mitigation risks refer to issues that happen when companies fail to plan for contingencies or explore alternative options.
- Planning and control risks. Planning and control hazards result from inadequate assessment and planning, which can lead to less-than-ideal management and control.
- Cultural risks. Cultural risks arise from a business culture that's prone to concealing or postponing the release of negative facts.
- IT and technology risks. Internal system failures and a lack of technological integrations can result in data breaches and other cybersecurity risks.
External supply chain risks
Risks that come from outside a company and have the potential to affect the supply chain's seamless operation are known as external supply chain risks. Since businesses can't directly manage these risks, it's necessary to take actions to reduce their negative effects.
The following are examples of external supply chain risks:
- Demand risks. These risks stem from unseen or inaccurately interpreted needs of consumers or end users.
- Environmental risks. Environmental hazards come from outside the supply chain and are usually associated with environmental problems, such as natural disasters and the possibility of terrorism.
- Social risks. Social risks are societal factors beyond a company's control, such as labor strikes, civil unrest, unethical labor practices or community opposition to something the company is doing. These risks can disrupt production, delay transportation, damage a company's reputation or lead to regulatory consequences.
- Economic risks. Economic volatility, including currency swings, inflation, spikes in commodity prices and abrupt demand changes, represents a major external threat to supply chains. These dynamics can compress profit margins, derail procurement strategies and cause inventory shortages, especially for organizations relying on Lean manufacturing or just-in-time models.
- Supply risks. Any interruption in the movement of goods -- whether raw materials or components -- within an organization's supply chain can cause supply risks.
- Business risks. Variables such as a supplier's financial or management stability or the purchase and sale of suppliers can cause business risks.
- Physical plant risks. The state of a supplier's physical facilities and regulatory compliance can produce physical plant risks.
- Geopolitical risks. Political instability, trade wars, tariffs, sanctions and regulatory changes can threaten the stability of the supply chain.

What are the consequences of a supply chain attack?
Supply chain attacks can have serious ramifications on businesses, their customers and even entire industries. Key consequences of supply chain attacks include the following:
- Financial losses. Supply chain attacks can incur substantial financial setbacks for organizations. These attacks can cause interruptions in operations, expensive periods of inactivity and postponements in production or service provisions. They can also necessitate extensive corrective actions.
- Data breaches. A supply chain attack has the potential to compromise sensitive data and result in data breaches. Attackers might gain unauthorized access to systems, steal valuable information or manipulate data for malicious purposes.
- Business disruptions. Successful supply chain attacks have the potential to seriously impair an organization's functioning. They can lead to production delays, disruptions in services and crippled productivity.
- Reputational damage. Supply chain attacks can damage an organization's reputation if they jeopardize the reliability and quality of its products. Customer and supplier trust and loyalty can deteriorate, resulting in a decline in business prospects and earnings.
- Regulatory and legal consequences. Attacks on the supply chain could have legal and regulatory repercussions for organizations. For example, if an organization violates data protection rules or fails to protect consumer data, it can be held accountable with fines and legal implications.
- Malware installation. Applications containing malicious code from supply chain attacks can be used to download and inject malware into company networks. Attackers could install ransomware, rootkits, keyloggers, viruses and other malware using injected supply chain attack code.
- National security risks. Attacks targeting critical infrastructure, such as power grids and transportation systems, can disrupt essential services and threaten national security.
Best practices for an SCRM plan
An organization should consider best practices for efficiently identifying, evaluating and mitigating risks while creating supply chain risk management strategies. Key steps involved in creating a supply chain strategy include the following:
- Identify and assess risks. The first step in developing an effective supply chain risk management program is to recognize and evaluate potential risks, including supply chain issues, natural disasters, geopolitical events and threats to cybersecurity. Both internal and external factors that can affect the supply chain should be assessed.
- Develop a formal SCRM program. Businesses should create a comprehensive supply chain risk management program that describes the roles, responsibilities and processes involved in managing supply chain risks. This program should be updated regularly.
- Monitor critical suppliers and components. Organizations must understand which supplier base or providers are vital to their business and continue to keep an eye on and assess their performance, dependability and risk-taking acumen.
- Deploy SCRM across the board. SCRM practices should be executed throughout the organization, ensuring that all relevant departments and stakeholders are involved. This entails raising awareness, providing training and establishing communication channels within the organization.
- Establish protocols for supplier assessment. Organizations should create guidelines and standards for evaluating their vendors' supply chain operations. This involves assessing risk management procedures, supply chain security culture and adherence to industry standards.
- Adopt technology for enhanced risk management. The adoption of technologies such as AI, internet of things and blockchain is recommended for organizations aiming to improve supply chain visibility, anticipate disruptions and maintain data integrity, as these tools offer actionable insights for improved risk management.
- Collaborate with stakeholders. Organizations should encourage communication and cooperation among key stakeholders, such as vendors, clients and business associates, as this can help them recognize possible hazards and take appropriate actions. SCRM requires collaboration and coordination among an organization's sales, marketing, production, development, procurement, finance and IT departments.
- Foster a culture of risk awareness. Organizations should cultivate a culture where all employees are aware of supply chain risks and their role in mitigation. Regular training should be provided, and open communication regarding potential threats and vulnerabilities should be encouraged.
- Continuously improve and adapt. SCRM is an ongoing process that requires continuous improvement and adaptation. Organizations should stay current on industry trends, regulatory changes and emerging risks that could affect their supply chain through continuous monitoring, participation in industry forums and engagement with relevant experts.
Challenges with supply chain risk management
Supply chain risk management presents several challenges due to the complexity and interconnected nature of global supply networks. Key difficulties include the following:
- Lack of visibility. Many companies struggle to track risks beyond their immediate suppliers, making fourth-party risk and deeper-tier vulnerabilities difficult to identify. This is because dependencies on indirect vendors introduce hidden vulnerabilities.
- Data security risks. Cyberthreats, such as data breaches and ransomware attacks, can compromise critical supply chain information and disrupt operations.
- Geopolitical and regulatory uncertainties. Trade policies, tariffs and shifting regulations can suddenly alter supply chain dynamics, creating compliance risks and financial instability.
- Supplier reliability issues. Vendor insolvencies, operational failures and ethical concerns, such as labor violations, can introduce unexpected liabilities.
- Natural disasters and pandemics. Events, including earthquakes, extreme weather and disease outbreaks, can halt production and disrupt global logistics.
- Balancing cost and risk. Companies often prioritize cost efficiency, potentially overlooking risk mitigation, which can leave them vulnerable to disruptions.
- Integration with risk frameworks. Aligning supply chain risk strategies with broader enterprise risk management and regulatory standards, such as Basel III, requires careful coordination.
SCRM tools and software considerations
Various tools are available for efficient control of supply chain risks. According to independent research by Informa TechTarget, tools for SCRM include the following categories and specific tools.
Tools for supply chain mapping
These tools aid in the visualization and mapping of the complete supply chain, encompassing vendors, producers, retailers and end users. They give businesses a thorough understanding of the supply chain network, making it possible to spot dependencies, weak points and possible risks. Tools used for supply chain mapping include value stream mapping, as well as vendor tools. The following are examples of supply chain mapping tools:
- AnyLogic. This multimethod simulation modeling tool is designed to simulate complex systems across various industries. It supports agent-based, discrete event and system dynamics simulation methodologies, letting users model and analyze systems for versatile and interactive analysis.
- Creately. This supply chain mapping tool is a visual platform designed for businesses to map, analyze and optimize their supply chain processes through customizable diagrams and real-time collaboration.
- Microsoft Power BI. Power BI lets users visualize and analyze their supply chain data geographically, such as tracking logistics flows and identifying geographical patterns.
- Tableau. This spatial data analysis feature lets users visualize and analyze supply chain data using maps, flow diagrams and other visual elements.
Tools for risk assessment
These tools aid in the identification, assessment and prioritization of hazards in the supply chain ecosystem. They help organizations evaluate the possibility and effect of various hazards through the use of algorithms and data analysis techniques. The following are some examples:
- Avetta. The Avetta supply chain risk assessment tool helps organizations identify, assess and manage risks associated with their suppliers and contractors. This tool focuses on safety, sustainability, compliance and business-related factors.
- Everstream Analytics. This AI-powered supply chain risk management platform provides businesses with real-time monitoring, predictive analytics, risk analytics and supply chain mapping to anticipate disruptions and build more resilient supply chains.
- Kodiak Hub. This is an AI-powered supply chain risk management platform that offers real-time risk scoring and workflow automation.
- Resilinc. This tool offers supplier risk assessment, real-time monitoring and risk mitigation planning. It also provides detailed analytics and insights to help businesses manage risks effectively and enhance supply chain resilience.
Tools for supplier relationship management
Supplier relationship management (SRM) tools offer a consolidated platform for performance tracking, communication and collaboration, aiding in managing relationships with suppliers. Organizations can monitor supplier performance, assess compliance, and oversee contracts and agreements with the help of these technologies. Common examples of SRM tools are the following:
- Coupa. This cloud-based spend management platform focuses on supplier collaboration and risk mitigation. It offers supplier performance benchmarking, compliance tracking and AI-driven insights.
- GEP SMART. This AI-driven procurement platform has integrated SRM functionalities and provides supplier onboarding, performance monitoring and collaborative portals.
- Ivalua. This tool provides supplier risk and performance tracking, compliance monitoring and real-time analytics. It's ideal for businesses requiring customizable SRM options.
- Jaggaer. This is an end-to-end procurement suite that offers supplier collaboration tools, spend analytics and compliance management. It's ideal for companies in regulated industries that require comprehensive supplier oversight.
- SAP Ariba. This cloud-based spend management software suite helps businesses streamline and automate their entire procurement process, including sourcing, contracts, purchasing, invoicing and supplier management. SAP Ariba also provides a platform for buyers and suppliers to connect and collaborate on a global business network.
Tools for demand forecasting
These tools make predictions about future demand for goods and services based on market patterns, historical data and statistical models. Reducing supply chain interruptions, increasing customer happiness and optimizing inventory levels are all facilitated by accurate demand forecasting for businesses. Machine learning and various types of AI algorithms are increasingly being used for demand forecasting in the supply chain.
The following are examples of demand forecasting tools:
- Blue Yonder. This tool integrates machine learning to deliver precise demand forecasts and includes a comprehensive suite of tools for demand planning, inventory management and replenishment. Blue Yonder is ideal for businesses looking for an all-in-one supply chain management option.
- FutureMargin. This tool enables better decision-making through what-if scenario analysis. It also offers self-service visualizations for communicating insights and is ideal for organizations integrating demand planning with financial and operational strategies.
- GEP NEXXE. This is an AI-powered supply chain platform offering advanced demand planning and forecasting capabilities. Its key features include consensus planning for collaborative forecasting, demand sensing using real-time data and integration of AI technology for precise forecasting.
- IBM Planning Analytics with Watson. This tool uses AI and machine learning to provide multidimensional modeling for in-depth analysis. It offers what-if scenario analysis for better decision-making, as well as self-service visualizations for clear communication of insights.
- Pipedrive. This demand forecasting tool helps sales teams predict revenue and streamline processes with a visual pipeline, customizable forecasts, AI insights and real-time reporting.
Tools for code verification
Vulnerabilities caused by third-party code integrated into a proprietary system pose one of the biggest hazards in a digital supply chain. The following are examples of tools that scan all third-party code for verification and integrity before letting it get near the internal systems:
- Checkmarx One. This application security platform offers software composition analysis, software bill of materials generation and malicious package protection to identify and mitigate risks from open source components.
- CodeSonar. This is a static code analysis tool that performs whole-program analysis on source and binary code, identifying security vulnerabilities and providing detailed trace information.
- MathWorks Polyspace. This static code analysis tool uses abstract interpretation to detect or prove the absence of certain runtime errors in C, C++ and Ada code.
- SonarQube. This open source platform performs continuous inspection of code quality, detecting bugs and security vulnerabilities across multiple programming languages.
Tools for incident management
These tools help companies properly respond to and handle problems or disturbances in the supply chain. They aim to minimize interruptions by coordinating response activities and providing procedures, communication channels and documentation capabilities. The following are some examples:
- COMET. This suite of tools provides incident reporting, root cause analysis and corrective action tracking. It integrates with existing environmental, health and safety platforms, and it provides real-time monitoring to enhance supply chain efficiency.
- ServiceNow. This comprehensive platform includes incident management modules that can be adapted for supply chain disruptions. ServiceNow offers collaboration features, reporting and workflow automation.
- TraceLink. This platform enables organizations to capture, analyze and resolve supply chain incidents by coordinating cross-functional teams. It offers real-time dashboards, audit trails and configurable workflows to enhance collaboration and reduce risks.
- Trustwell. This tool, formerly known as Genesis Food and FoodLogiQ, offers a suite of cloud-based tools focused on the food and beverage industry to help manage various aspects of the supply chain. It puts a strong emphasis on food safety, compliance, transparency and quality.
Tools for collaboration and communication
These tools help supply chain stakeholders collaborate and communicate effectively. They help with real-time information sharing, document collaboration and coordination among supply chain teams and partners:
- Chanty. This intuitive collaboration platform combines chat and task management. It offers built-in task management with a Kanban view, enabling teams to organize work visually and efficiently. It integrates seamlessly with tools such as Google Drive and Trello, enabling smooth collaboration across platforms.
- Infor Nexus. This is a cloud-based platform offering real-time visibility and collaboration across global supply chains. Its key features include AI-driven supply chain visibility, seamless supplier collaboration and advanced risk management tools.
- Oracle Cloud SCM. This is a comprehensive suite that covers procurement, logistics and order management. It offers real-time demand and supply planning, supplier collaboration tools and AI-powered demand forecasting.
Effective risk management is crucial for every aspect of a business. Explore the essential skills risk managers require to excel in their roles.
