Planning the journey from SD-WAN to SASE
Enterprises need integrated security and networking frameworks to manage distributed IT environments and are looking to SD-WAN and security options like SASE to get the job done.
Modern IT environments are highly distributed, with applications spread across private data centers, multiple public clouds and numerous edge locations. Simultaneously, hybrid work initiatives are here to stay and employees are distributed between corporate, home and remote locations. Plus, IoT and industrial IoT mean more connected devices across virtually any location.
The key to making these complex environments work effectively is to ensure all the applications, employees and devices are securely connected to each other. This is easier said than done. Legacy network and security architectures -- hub and spoke topologies and castle and moat models, for example -- forced all traffic through the data center security stack. This provided a high level of security but created performance issues, especially when connecting to cloud-based apps.
To overcome those issues, SD-WAN technology emerged, enabling organizations to bypass data center security stacks and provide direct internet access from remote locations. Though SD-WAN technology provided a measure of security in that it could segment traffic, over time its security posture evolved: Providers built out ecosystems with security vendors to enable single-click integration with cloud or on-premises deployments.
Today, organizations are working toward creating a more robust framework of integrated security and networking technologies referred to as Secure Access Service Edge (SASE). This is essentially a combination of SD-WAN and other networking technologies and security services, with the latter now referred to as security service edge (SSE). SSE encompasses a number of security functions to provide the requisite levels of secure connectivity with functionality such as zero-trust network access (ZTNA), data loss prevention (DLP), cloud access security brokers and more.
Moving forward, network and security vendors are working to deliver tighter integration with third parties or provide a fully integrated product with both SD-WAN and SSE. Because of SD-WAN's rapid adoption to support direct internet access, organizations can leverage existing products to serve as a foundation for their SASE implementations. This would be true for both do-it-yourself as well as managed services implementations.
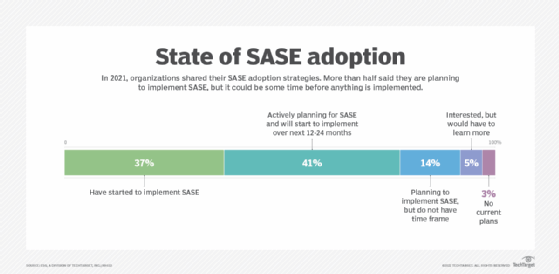
If you are still in the planning stages for an integrated SASE deployment, you aren't alone. Last year, just a little over one-third of respondents to an Enterprise Strategy Group (ESG) survey stated that they had begun to implement a SASE framework and products. A little more than half (55%) indicated that they are planning for SASE, but it could be some time before anything is implemented.
Starting with SD-WAN for network-first approach
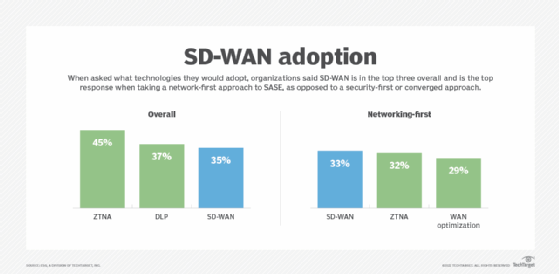
Why do we think SD-WAN makes a good starting point? When ESG asked organizations about the technologies they would adopt, SD-WAN was in the top three choices overall and was the top response for organizations taking a network-first approach to SASE, as opposed to a security-first or converged approach.
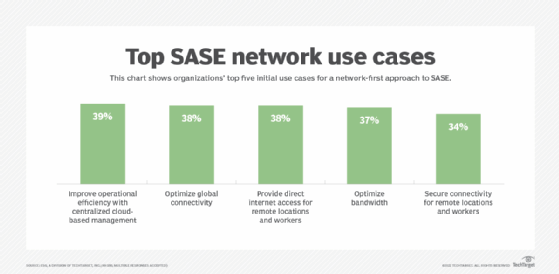
SD-WAN ranking in the top three also makes sense when you consider the top five initial networking use cases. Given the complexity of these environments, it isn't a surprise to see improving operational efficiency with centralized cloud-based management as the top response, followed closely by optimizing global connectivity, providing direct internet access for remote locations and workers, and optimizing available bandwidth. Note that more than one-third of respondents indicated they will leverage the technology to enable secure connectivity for remote workers and locations.
SD-WAN as SASE foundation
SD-WAN can also provide great value for organizations that are not quite ready to go all-in on the cloud for security. Organizations opting to take a hybrid approach to SASE -- based on the needs of each location and existing security technology -- can leverage SD-WAN hardware to host third-party or same-vendor products while still providing operational efficiencies and reduced costs. This still enables organizations to migrate to the cloud when ready while maintaining an optimized security posture.
Managed service providers (MSPs) and telecom providers are also looking to extend their value to organizations that already consume managed SD-WAN services; combing through those additional security functions is a great path to deliver additional value and implement a SASE framework. Given their experience with universal customer premises equipment, these providers should be well positioned to extend the value of SASE through either a hybrid or cloud-based approach and easily migrate between the two.
SD-WAN can be the foundation for a building a SASE framework. Yet, it will be imperative for organizations to understand what network and security functionality their chosen SD-WAN vendors or MSPs have today (third party or internal) and will have in the future to enable a seamless transition to a full SASE implementation. This would include evaluating how all these technologies will integrate and whether a multivendor approach or a fully converged approach is more desirable for the organization.
Ultimately, this is about providing secure connectivity in a highly distributed, modern IT environment. Given the increased complexity and the need to converge security and networking operational teams, organizations will have to work diligently to overcome cultural and procedural challenges to ensure operational efficiency and ultimately positive customer experiences, regardless of where applications or users are located. In the end, SD-WAN should enable organizations to deploy a robust SASE framework that works best for their environment.
SD-WAN is an easy first step toward improving security and experiences to all remote sites. Organizations need to understand that SD-WAN and SASE aren't either-or propositions. It is important, however, to adopt an SD-WAN platform that enables the seamless deployment of a SASE framework. SD-WAN should be a facilitator, not a barrier, and it is an easy first step to an organization's SASE journey.
ESG is a division of TechTarget.





