two-step verification
What is two-step verification?
Two-step verification is a process that involves two authentication steps performed one after the other to verify that someone or something requesting access is who or what they say they are.
Two-step verification vs. two-factor authentication
Many people use the terms two-step verification and two-factor authentication (2FA) interchangeably. Both involve two steps used for verification. The difference between the two is that the sequential methods in two-step verification can belong to the same category of authentication factors, while the methods used for 2FA aren't necessarily sequential and aren't the same factor.
Authentication factors include the following:
- Knowledge factors -- something you know, such as a username and password.
- Possession factors -- something you have, such as a smart card or security token.
- Inherence factors -- something you are, including biometrics such as fingerprint or iris scans.
Other factors, such as time or location, can also be used.
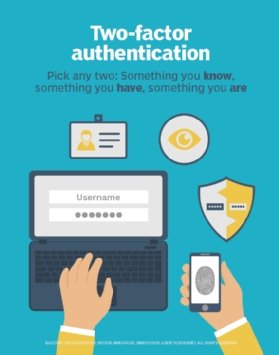
Two-step verification methods include any combination of two knowledge, possession and inherence factors, including repeated factors. Meanwhile, 2FA methods must be two distinct methods -- for example, a username and password as well as a facial recognition.
Furthermore, verification and authentication are not completely synonymous. Verification can be part of a real-world process, such as providing a driver's license as proof of identity. Authentication is an adaptation of verification processes designed to protect access to data and systems.
Many two-step verification products and services are also 2FA. Google's 2-Step Verification service, for example, involves a username and password as well as a code sent to the user's device. Many other user authentication systems described as two-step verification also qualify as 2FA.
Today, multifactor authentication is touted as more secure than two-step verification and 2FA.
Editor's note: This article was originally written by Ivy Wigmore. It was updated to improve the reader experience.







