Google Authenticator
What is Google Authenticator?
Google Authenticator is a mobile security application that provides a second type of confirmation for websites and online services that use two-factor authentication (2FA) to verify a user's identity before granting him or her access to secure resources. An authenticator is considered to be a more secure approach to 2FA than using Short Message Service (SMS), i.e., text messages, as the second form of verification. Text messages can be monitored and intercepted, and hackers can trick carriers into switching phone numbers to new devices.
The importance of two-factor authentication
In general, 2FA is considered a better option than single-factor authentication (SFA), which typically involves a username and password. Two-factor authentication reduces the likelihood that an intruder can masquerade as an authorized user.
The importance of 2FA came to light in a February 2022 blog post by Guemmy Kim, then-director of account security and safety at Google. Google had automatically enrolled users in 2FA the previous year, according to Kim. After over 150 million people were set up with 2FA, Google saw a 50% decrease in the number of accounts being compromised.
Two-factor authentication requires a user to provide two types of verification when logging onto a website or online service. For example, a username/password login would represent one type, and a passcode texted to the user would represent the second type. These authentication types -- referred to as factors -- help verify that the user trying to connect to a secure site or service is who they claim to be.
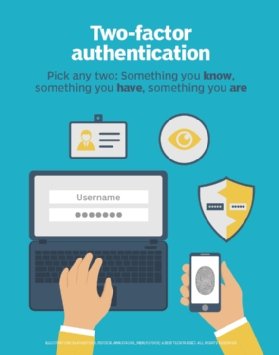
There are three categories of authentication factors:
- Knowledge factors. Credentials that the user knows, typically a username and password.
- Possession factors. Things that the user has, typically a smartphone.
- Inherence factors. Things that the user is, typically a biometric characteristic such as a fingerprint or iris pattern.
The use of knowledge factors has been a common practice since the early days of the web, with many sites and services requiring a username and password. In most cases, only the password represents the secure component. A username might be as simple as an email address, which is often publicly known or easily acquired. The password must always remain secret and secure to protect resources. If it is compromised, those resources can be put at risk.
Unfortunately, passwords can often be a weak link in network and data protection, especially when combined with poor password practices. A website or online service that requires only a username and password uses single-factor authentication because it relies only on knowledge factors to authenticate users. However, with the sophistication of cyber attacks, usernames and passwords alone are not enough to fully protect resources, and many online systems now require 2FA or at least offer it as an option.
Today, most implementations of two-factor authentication use the username/password logon combination as the first factor, and the second factor is a temporary passcode that the user must enter along with the logon information. The user receives the passcode on his or her device, either as a text message or through an authenticator app such as Google Authenticator. The passcode is good for a limited amount of time. The device that receives the text represents something that the user possesses, typically a smartphone, which qualifies as a possession factor in 2FA.
How does Google Authenticator work?
Most organizations are aware that passwords are easily compromised and have implemented 2FA on their sites or services. They often include support for an authenticator app such as Google Authenticator, which runs on the user's iOS or Android device. Because the majority of exploits are conducted via the internet, it is unlikely that the hacker can also access the user's physical device.
Today, Google Authenticator is used extensively for websites and online services that have enabled 2FA. The app generates a one-time passcode (OTP) for each site or service that the user has registered with the authenticator. The passcodes are six-digit numbers that are refreshed every 30 seconds.
Here's how to use Google Authenticator to sign into a site or service that has implemented 2FA:
- Install Google Authenticator on the user's iOS or Android device. This step is only necessary once.
- Enable 2FA on the user account associated with the target site or service. The user will be provided with a QR code, setup key or both. The QR code is usually easier to work with.
- Open Google Authenticator on the mobile device and tap the plus sign in the lower right corner to add the target site or service. The user is presented with two options:
- Scan a quick response code (QR code). Select the option and aim the device at the QR code to capture its image.
- Enter a setup key. Select this option, type a name for the login, and then type the setup key.
- Google Authenticator will create the login and display its first OTP.
- Return to the target site or service and complete the process of setting up 2FA, following the provided instructions. As part of this process, the user will need to enter the passcode that the authenticator generated.
After setting up the login on Google Authenticator, the user can use the authenticator to retrieve the latest passcode each time he or she logs into the site or service. It will be used in addition to a username and password. The site or service uses these three pieces of information to verify the identity of the person entering the login data. The authentication process works under the assumption that the user is in possession of the device on which Google Authenticator is installed.

The Google Authenticator app is based on the time-based one-time password algorithm specified in the Internet Engineering Task Force's (IETF) RFC 6238. The TOTP algorithm generates a six-digit passcode that factors in the current time of day to ensure that each passcode is unique. Passcodes are changed at regular intervals. The RFC recommends a default interval of 30 seconds.
See how to secure one-time passwords are from attacks and learn the difference between two-step verification and 2FA. Read about the most common digital authentication methods.







