Blockchain security: Everything you should know for safe use
Despite its reputation, blockchain is subject to many of the same vulnerabilities as other software. It helps to have a clear idea of its inherent strengths and weaknesses.
A blockchain is a tamper-resistant, distributed record of transactions. It employs cryptography to ensure its records aren't altered or destroyed, and it doesn't rely on a trusted central authority. Blockchains are most often associated with cryptocurrency and financial transactions, but they're also used to facilitate smart contracts and other digital transactions.
Although blockchains aren't a brand-new concept -- they've been around for nearly 15 years -- they're becoming more widely used and accepted. Many individuals and organizations are already using blockchains, and new uses for blockchains are constantly being tested. Unfortunately, as their popularity has grown, so has attackers' interest in targeting them. If security isn't taken into consideration for blockchains, their money and transactions will be at serious risk of disruption and theft.
How does security work in blockchain technology?
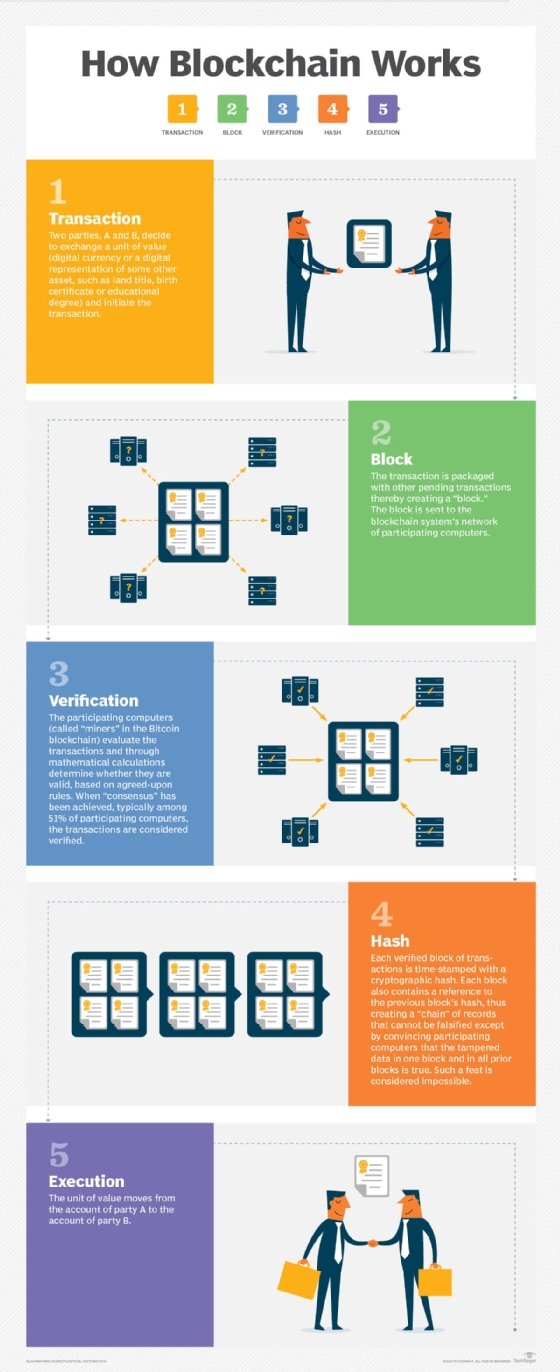
Blockchain technology creates a distributed ledger of transactions that uses cryptography to safeguard its integrity. In a blockchain, data for one or more new transactions is bundled into a block. Blockchain participants perform complex cryptographic calculations (called mining), often competing to be the first to solve the problem. The result is a cryptographic hash for the new block that accounts for the cryptographic hash of the previous block.
Next, the block containing the new hash is provided to the blockchain network's participants. The participants check the block by performing calculations on it. If it's valid, they add it to their copy of the blockchain. Once most participants agree the block is valid, the block is added throughout the blockchain network. No further changes to that block are permitted.
This approach avoids having a central authority that must be trusted in the middle of transactions. It also avoids having a single point of failure for the blockchain. Using the previous block's hash when calculating the new block means that any attempts to change or delete a block are easily detectable by all blockchain participants. This makes blockchains nearly tamper proof.
How secure is blockchain technology?
A common misconception is that all blockchain technology is well secured because it relies on cryptography. While it's true that blockchains all use cryptography, there are two major caveats:
- Fundamentally, blockchains are software code, so they're prone to the same kinds of vulnerabilities that affect other software throughout their lifecycles.
- There can be vast differences in the strength of cryptographic algorithms and key lengths as well as their implementations. Effective cryptographic key management is also important in keeping a blockchain secure.
Blockchain technology is not inherently more or less secure than other technologies.
Explaining the different types of blockchain security
At a high level, the types of blockchains are based on their access control models:
- A public blockchain (also called a permissionless blockchain) has no restrictions on who can access it or publish new blocks. Blockchain participants can be anonymous.
- A private blockchain (also known as a permissioned blockchain) restricts who can publish new blocks. It might also restrict who can access the blockchain. Each user of the blockchain must be identified and authenticated. Such a blockchain can be controlled by a group (a consortium blockchain) or an individual.
- A hybrid blockchain refers to having public and private blockchains that are interoperable, essentially forming a blockchain of blockchains.
Because public blockchains are inherently accessible to everyone and don't perform any user authentication, they are much easier for attackers to target and compromise than private blockchains. The rest of this article focuses primarily on public blockchain security.

Common threats to blockchain security
Public blockchains rely on reaching consensus among their participants. There are numerous consensus models for blockchains, and each has security strengths and weaknesses that make it better suited to certain situations. One common consensus model is called proof-of-work. Participants solve difficult problems requiring significant computing power, and producing the correct solution to the problem is proof that a participant has put forth effort and has essentially earned the right to release the new block.
Unfortunately, because public blockchains let anyone participate, attackers have many ways to disrupt consensus. One common threat, a sybil attack, involves an attacker adding a bunch of bogus participants to a blockchain network. This can give the attacker control of most of the participants. Now the attacker can create fake transactions and have the bogus participants "validate" them. A similar threat, called a 51% attack, involves an attacker or group of attackers banding together to form a mining pool that does more than 50% of the mining for a blockchain.
There are many other threats that generally affect all software:
- Routing attacks, where an attacker tampers with routing configurations so they can intercept unencrypted blockchain network traffic and access or alter it.
- Phishing attacks, where an attacker uses social engineering methods to steal blockchain participants' credentials, such as private keys and passphrases.
- Denial-of-service attacks, such as flooding a blockchain with huge numbers of requests to stop it from functioning.
There are also threats specific to blockchain applications. For example, double spending is when someone tries to spend the same cryptocurrency in two places at the same time. Smart contracts, which are blockchain applications that perform transactions and other processes according to a set of rules defined in their program code, have specific vulnerabilities to guard against.
Best practices to secure blockchain networks
Here are five best practices to secure your blockchain networks:
- Make sure that a blockchain is appropriate for the transactions it would be recording. If records contain personal information or other sensitive information, a blockchain might inadvertently expose it and cause a data breach. Another consideration is whether transactions are truly final once they take place or you need the flexibility to modify or delete previous transactions.
- Remember that blockchains are subject to all the cybersecurity and privacy laws, regulations, and other requirements that any other software must comply with throughout its lifecycle.
- Identity management is important. Even in public blockchain networks, participants still need to know they're communicating with the legitimate network. For private blockchain networks, access management is incredibly important for preventing attackers from gaining unauthorized access to the network.
- Perform regular risk assessments and audits of blockchain technology and related processes, such as key management, and determine how to handle discovered vulnerabilities or other weaknesses.
- Plan for the worst. A major new vulnerability might be found in blockchain code, a private key might be stolen, participants' computers might be compromised -- many things can go wrong. Be ready by having response and recovery processes in place ahead of time. There may also be disputes among participants, so be prepared to resolve those as well to prevent your blockchain from being disrupted.








