What is the Common Information Model (CIM)?
The Common Information Model (CIM) is a computer industry standard that defines device and application characteristics so system administrators and management programs can control devices and applications from different manufacturers. CIM was developed and is managed by the Distributed Management Task Force (DMTF), a consortium of hardware and software manufacturers that creates open manageability standards for diverse IT infrastructures, both emerging and traditional. The CIM standard includes a specification, management schema and metamodel, which together provide a common definition of management information for systems, networks, applications and services.
How does the Common Information Model work?
The CIM standard is divided into the CIM Specification, CIM Management Schema and CIM Metamodel.
CIM Specification
The CIM Specification defines the way that management models from different manufacturers can communicate with each other. Simply put, it provides standardized definitions for structuring and interpreting CIM models and integrating them with other management models. By clarifying the organization and structure of CIM, the specification ensures that all CIM applications and extensions comply with a common, universally accepted standard. This ensures interoperability across different systems and platforms.
The specification also organizes information, such as legal statement types, syntax and expressions, for performing various tasks. This enables disparate groups of people to manage common aspects of an information model.
CIM Management Schema
Management platforms and applications for device configuration, performance management and change management all require management schemas to function. The CIM standard structures managed environments as a collection of interrelated systems, with the Management Schema providing the actual model descriptions. According to this standard, each system in the environment is composed of discrete elements.
This article is part of
What is desktop management and how does it work?
The schema provides a set of classes, such as computer and networking systems, middleware, databases, operating systems (OSes), routers, hard disk drives, services and user-defined technologies. Each class contains properties that describe it with attributes such as network name, serial number or error codes, as well as associations that link different parts of the model together.
While DMTF defines the standard schema under CIM, major manufacturers, such as IBM, HP or Dell, provide Extension Schemas that include their products. In addition, other organizations can extend the schema to build custom applications. This is because CIM enables vendor extensions and includes a distinct layer called extension schemas. These schemas are the technology-specific extensions to the common model.
The CIM Schema also includes two other distinct layers called core model and common model.
The common model is a basic set of classes in CIM that define various technology-independent areas, like systems, applications, devices and networks, while the core model represents a smaller set of classes for analyzing and describing managed systems and for extending the common schema.
CIM Metamodel
The CIM Metamodel defines how to construct new models, regardless of domains or applications. To enable such constructions, it provides standardized rules, foundational constructs and semantics. It also provides constraints that govern various relationships and properties, as well as a schema that represents those models.
Qualifiers can adapt and extend the metamodel and enhance its capability. The metamodel enables the addition of new classes, attributes or associations in a manner consistent with its established rules and definitions. Such consistency facilities the metamodel's extension and ensures that existing structures or semantics do not break. It also enables interoperability with a wide range of systems and platforms.
CIM Management Schema and classes
The CIM Management Schema provides a standardized, easily understood conceptual framework for information models in specific domains. This framework consists of numerous classes that create the building blocks of a modeled domain and represent entities or objects in that domain. Each class has various properties -- also known as attributes -- that store information about an entity within the domain. In addition, associations in the CIM Schema define the relationships between classes and determine how they interact.
The CIM common model includes a set of base classes that define various technology-independent areas. These classes provide a detailed view of a domain to help with program design and implementation. The CIM core model provides a smaller set of classes for describing managed systems and for extending the common schema.
Creating CIM classes with Microsoft Windows Management Instrumentation
Microsoft defines a CIM class as an "object-oriented abstraction of the entity being managed through a [CIM Object Manager (CIMOM)] infrastructure," such as Microsoft Windows Management Instrumentation. Users can use WMI to create classes that represent hard disk drives, applications, network routers and so on in CIM. These objects are then identified by a class name, such as device, and attributes in the CIM Schema.
This information can be accessed by common programming languages and queried for information. A disk drive manufacturer, for example, can provide information about its disks in the schema, and developers then can build applications to access information such as capacity, specifications, monitoring and error reporting.
Microsoft defines numerous WMI system classes. These predefined classes are based on CIM and include objects that support WMI activities, such as event registration, event notification, provider registration and security. WMI creates a set of system classes when a new WMI namespace is created, represented by the system class _Namespace. Managed Object Format (MOF) files contain the schema class definitions from providers. However, the WMI system classes are not declared in a MOF file.
Some common WMI system classes are the following:
- __AbsoluteTimerInstruction, which generates an event on a specific date at a specific time.
- __CacheControl, which determines when WMI should release a Component Object Model object.
- _Event, which represents the parent class for intrinsic and extrinsic events.
- _IndicationRelated, which is the parent class for all event-related classes.
- _NotifyStatus, the parent class for provider-defined error classes.
- _SystemSecurity, which provides a way to access and modify the security settings of a namespace.
Some common classes are the following:
- CIM_ComputerSystem, the computer host.
- CIM_DataFile, the computer file.
- CIM_Directory, the files directory.
- CIM_DiskPartition, the disk partition.
- CIM_FIFOPipeFile, named pipes.
- CIM_OperatingSystem, the OS.
- CIM_Process, the computer process.
- CIM_SqlTable, the database table.
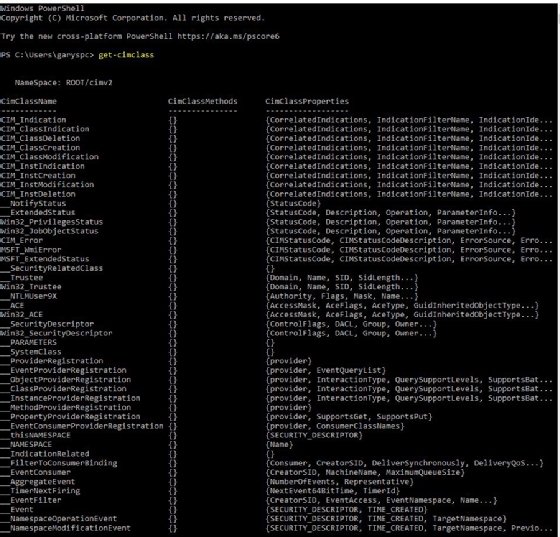
Users can expose the CIM classes for Windows with a PowerShell cmdlet.
>get-cimclass
The MOF files that contain the schema class definitions are available on the DMTF site in zip archives for each schema version.
Figure 1 shows a partial output of the command.
What are the advantages of using CIM?
CIM provides a common framework to define management information, representing said information consistently across a broad range of platforms, systems and applications. Such consistency facilitates smooth data exchange and minimizes data conflicts between different parts of an organization. It also helps to streamline data management and data-related operations, which can enhance organizational decision-making.
Additionally, CIM provides various classes that enable managers to easily control the different devices, applications and technologies used in the organization. Managers can distinguish between different management environments and link different parts of the enterprise model, simplifying the management of systems, networks, applications and services.
CIM is flexible and extensible and can easily adapt to new domains and applications, facilitating interoperability without breaking existing structures.
The CIM standard provides a method to develop software, particularly management and console interfaces, and to monitor key components, such as system and device performance, system information and network status. Without CIM, cross-device communication would be difficult and, in some cases, even impossible. CIM interfaces come already built into most OSes.
Examples of the Common Information Model
CIM-based devices and applications use CIM's repository and, via Web-Based Enterprise Management (WBEM), can query devices and software for attributes. They can also help build applications to exchange or gather information from disparate systems.
Some examples of different information CIM can access are the following:
- System management applications that retrieve information from devices, regardless of manufacturer or developer.
- Error handling and reporting functions, such as Windows event logs.
- Device information monitoring, such as disk free space and hardware serial number.
- Backup information, such as the last backup made on each system.
- Performance information, such as CPU utilization, number of processors and memory utilization.
- Notifications of failed logins and password expirations.
CIM integrates closely with both native OS and third-party applications. Every manufacturer of computer devices has management interfaces that use CIM and the related WBEM infrastructure. Thus, CIM provides a widespread instrumentation base throughout the IT industry that permits hardware and software to query and report information required by users and applications alike. The CIM Schema is extensible and adaptable to new devices and technologies.
What is WBEM?
WBEM is a set of specifications that define how objects may be discovered, accessed and manipulated across disparate systems. WBEM can take a request -- from a graphical user interface, for example -- and construct and send that request to the WBEM server. The WBEM server then interprets the request using the CIM Schema definitions, passes it to the provider of the hardware being queried and returns the status of the device or whatever the query asked for to the operator.
Windows, Linux OSes, IBM and even VMware provide CIMOM with their own management interface to achieve a well-defined, managed environment. They also extend the CIM Schema for their purposes. Microsoft provides its CIMOM interface via WMI, which uses CIM Schema definitions for devices and software and then stores it in the WMI repository. WMI is an extension of Windows Driver Model and enables scripted access to hardware and software using common scripting languages, including VBScript, PowerShell and a special command-line interface called WMI command line (WMIC).
WMIC can be used to query for information on a Windows client or server. For example, open a command prompt, and enter the following command.
>WMIC
At the WMIC prompt, enter /? for a list of switches to the command.
Find the computer name and Windows version for that computer by then using the following WMIC commands:
>WMIC get name
>WMIC os get version
Once administrators learn the basics of PowerShell, they can start writing scripts. This tutorial is designed for beginners and helps them complete tasks efficiently.





