What is Desktop Management Interface (DMI)?
The Desktop Management Interface (DMI) is a standard industry framework for managing and tracking components on one or more personal computers, laptops or servers, usually from a centralized console. DMI collects information about various system components -- both hardware and software -- which then enables system administrators to track and manage the system using management software.
DMI, the first ever desktop management standard, was developed by the DMTF, formerly the Distributed Management Task Force, an organization that creates open management standards spanning a range of IT infrastructure, including cloud, virtualization, networks, servers, storage, plus desktops and mobile devices.
Is DMI still used?
The initial DMI standard was defined by the DMTF in 1998. As a standalone standard, the DMI persisted until March 31, 2005, when it reached its end-of-life status. It is no longer widely used. Since then, other DMTF technologies emerged and DMI has been supplanted by newer DMTF standards such as the Common Information Model (CIM).
Importance of DMI
Prior to the DMI, there was no standardized framework or common language for inventorying system components or managing those systems. Without such a language, it was difficult for system admins to capture component information and manage those components. Also, lacking a standardized system for managing and tracking system components, they had to understand complex encoding mechanisms and foreign registration schemes.
This article is part of
What is desktop management and how does it work?
Development of the DMI was an attempt to mitigate these issues. It provided a standardized format for describing the management information of various components: processor, memory, storage devices, and so on. All the manageable descriptions are defined in the Management Information Format (MIF) language.
Each component of a desktop, laptop or server has its own MIF file. This file is added to the MIF database when that component is initially installed in the system. The database stores details about all the hardware and software components that constitute a computing system. System management software can access the MIF files to configure, monitor and manage the overall system.
DMI is not dependent on hardware and operating systems (OSes) so system admins can work with diverse hardware and software configurations. The included Management Interface (MI) is a remote interface that can be used by applications that manage system components with one of the DMI's supported Remote Procedure Calls (RPCs). Moreover, DMI's standardized set of interfaces make it easy to develop management applications that can seamlessly interact with and monitor a variety of computing systems.
In addition to providing a standard format for describing management information, DMI provides a set of services to facilitate remote communication, as well as two sets of application programming interfaces (APIs). One API set enables interactions between service providers and management applications, while the other facilitates interactions between service providers and system components.
Characteristics of DMI
Since DMI is hardware- and OS-independent, it is a good option for managing many kinds of computing systems. The standard is also independent of specific management protocols, each of which have a different way to describe how a device interacts and communicates with a management system. DMI's protocol-independence simplifies device monitoring and management.
Another characteristic of DMI is that it can be used both locally and remotely. When used locally, no network is required. To use DMI remotely, any of the following RPCs can be used:
- DCE/RPC: Distributed Computing Environment/Remote Procedure Call.
- ONC/RPC: Open Network Computing Remote Procedure Call.
- TI/RPC: Transport-independent Remote Procedure Call.
Lastly, DMI can be easily adopted by vendors since they don't have to learn the details of management protocols or worry about complex encoding styles or management registration information.
Benefits of DMI
Shortly after its introduction, DMI emerged as a widely adopted industry standard to manage system components because it provides a uniform and easy-to-understand way to collect and present system information. Its standardized BIOS and OS interfaces enable system admins to efficiently manage systems, regardless of individual systems' configurations.
DMI also simplifies issue diagnosis and troubleshooting. Admins can access the information available in component MIF files using management software (which is designed to interact with the DMI framework). This information allows them to identify and clarify potential issues. They can then proactively address those issues before they escalate, thus expediting resolution.
Some of the other benefits of DMI include the following:
- Provides an easy way to maintain an accurate inventory of hardware components.
- Makes it easy to track hardware changes.
- Enables admins to remotely monitor systems and track performance/health metrics.
- Promotes proactive system maintenance.
- Helps with the planning and implementation of security measures.
- Facilitates capacity planning and energy management by providing insights into hardware components, usage and power profiles.
- Helps with system updates, upgrades and replacements.
- Aids developers in optimizing software applications for various system configurations, thus minimizing compatibility issues and enhancing user experiences.
Post the DMI's end-of-life, the DMTF also developed Desktop and Mobile Architecture for System Hardware (DASH). DASH is a large collection of specifications for secure out-of-band and remote management of desktop and mobile client systems.
All major hardware vendors support DASH, including processor vendors like AMD and Intel. Virtually all major management consoles, including Microsoft, and numerous open source environments, including KVM and VNX, SolarWinds, Jira, Citrix, VMware and others, support DASH or provide DASH plugins for their runtime environments.
DASH development history
In March 2007, the DMTF's Desktop and Mobile Working Group (DMWG) unveiled the DASH Initiative that would deliver standards-based platform management for desktop and mobile systems. The goal was to create a framework that would provide standardized syntax, models, mechanisms, semantics, profiles, interfaces and protocols needed to efficiently and easily manage such systems -- regardless of machine state, OS or vendor.
In December 2007, the DMTF published details about the DASH systems management framework for mobile and desktop hardware.
Then in 2011, the WS-Management CIM Binding Specification was published by the DMTF. The WS-Management Specification enables interoperability between management applications and managed resources, while the WS-Management CIM Binding Specification describes how to use the WS-Management protocol to communicate with resources modeled with CIM. The CIM, which is developed and maintained by the CIM Forum, provides a standardized and common definition of management information for systems, networks, applications and services. It is a key aspect of the DMTF approach to systems management. Another important DMTF document, DSP0232 (DASH Implementation Requirements), covers the conformance requirements for implementing DASH.
DASH profiles
There are dozens of DMTF profiles related to DASH that cover a wide range of system characteristics, including OS status, software updates, BIOS management, system memory, CPU and power state management. These profiles provide all the required classes, instances, properties and methods to manage and control desktop and mobile systems.
DASH also offers a range of advanced capabilities that provide comprehensive end-to-end management. These include boot control, record log, software inventory, battery and IP interface.
The SMF working group maintains these profiles.
How does modern desktop management work with DASH?
DASH uses the WS-Management specification and the DMTF's CIM to collect, monitor and manage desktop and mobile systems using some or all the data that the more than three dozen DASH-related DMTF profiles cover. DASH covers architectural semantics for desktop and mobile devices. It also uses industry standard protocols and its profiles to standardize management mobile and desktop system management irrespective of machine state, OS, or other vendor specifics.
DASH allows the same tools, syntax, semantics and interfaces to work across most computing systems, including traditional desktops, mobile and laptop PCs, bladed PCs, virtual machines, thin clients, and mobile devices, such as smartphones and tablets. The DASH Protocol Stack supports the various layers needed to support management applications through the WS-Management protocol using standard IP-based protocols and networked communications.
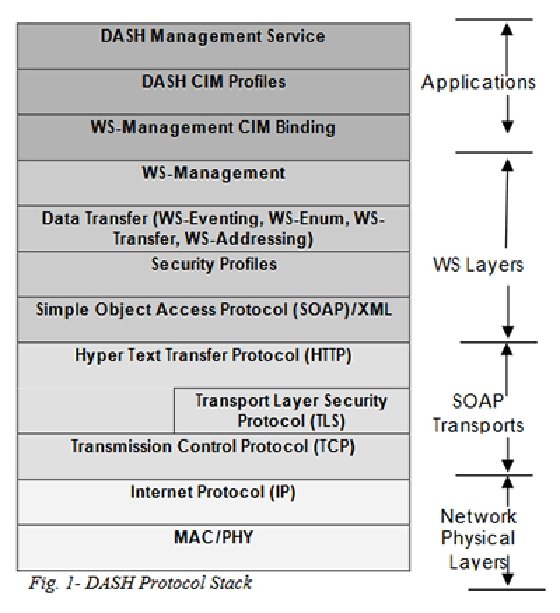
DASH comes into play through a related CIM profile and its DASH Management service, atop a standard collection of Web services and networking layers.
The stack rests on Simple Object Access Protocol (SOAP) messages that move Extensible Markup Language (XML) content between communicating parties. Above that layer, WS-Management provides event handling, enumeration, data transfer and device and service addressing capabilities. This allows DASH to employ industry-standard network and transport layer mechanisms, including encryption, authorization and authentication, and to manage roles, authorization and accounts using standard profiles. Further, DASH provides access control over all its managed resources and operations using role-based access controls such as read-only user, operator and administrator to define different access levels and update and control capability.
Compare desktop management software options for business, see how to build a plan for PC and desktop lifecycle management, gain an understanding of remote desktop connection management tools and explore PC lifecycle management best practices.