Optimize data protection as a service with these essential tips
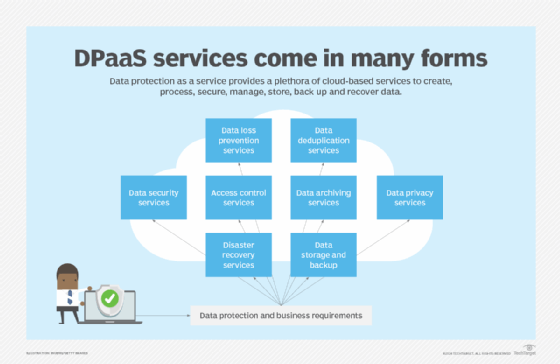
As a one-stop shop, DPaaS and its array of data management and protective cloud services provide security, access control, backup and recovery to safeguard mission-critical data.
`Consider all the activities associated with creating, processing, securing, managing, storing, backing up and recovering data. Then consider packaging them into a managed service supported by cloud-based resources. As a one-stop shop, data protection as a service can provide an important option for data storage managers and CIOs.
DPaaS can improve all aspects of data protection with an array of data management and protective services available at the touch of a button. Cloud service providers (CSPs) and managed service providers (MSPs) offer data protection services. The challenge is to decide which services are needed now and in the future.
DPaaS benefits and risks
Regardless of the size or type of organization, every business creates enormous amounts of data daily. Businesses glean and apply this data to all aspects of their operations. Smaller companies might not have the data protection and management requirements of much larger organizations, but they still need to ensure their data is secure and available when needed.
DPaaS organizes all data protection activities under one roof. CSPs and MSPs that specialize in backup, data management and disaster recovery typically have resources available to address most or all data protection activities. Additional benefits of using cloud- or MSP-based data protection services include less need for physical equipment and floor space, reduced capital expenditures for data protection systems, and the ability to deploy services faster compared with an on-site arrangement.
DPaaS also makes sense for companies managing compliance and undergoing audits, especially if the CSP or MSP providing DPaaS resources can demonstrate compliance with various data protection requirements. Key compliance regulations include the EU's GDPR, the U.S.'s Consumer Credit Protection Act and Right to Financial Privacy Act, and the U.K.'s Data Protection Act, as well as state-level data protection regulations. Access to experienced data protection resources can help businesses demonstrate their ability and commitment to protect their data.
In addition, balancing on-site data storage and protection resources with cloud-based data protection services can increase the security and availability of mission-critical and sensitive data. Hybrid cloud configurations can also enable companies to test MSP offerings before they make a large investment.
Still, organizations must weigh the risks of working with a single DPaaS vendor. Aligning with one vendor could make it difficult to switch to another vendor and possibly lead to unplanned expenses. And MSPs or CSPs that store all of an organization's data could raise security concerns. Ideally, vendors should be able to encrypt data in transit and at rest as part of their DPaaS services.
Service-level agreements (SLAs) are especially important when working with an outside firm that's storing mission-critical data and systems. Vendors that refuse to honor an SLA should not be considered. If they offer their own SLA, companies should have it carefully reviewed by their internal legal department.
Planning and deploying data protection as a service
Businesses must know their requirements at the outset so that they can identify which components of a DPaaS offering are most appropriate. The flexibility and scalability of cloud services can simplify any changes to the services being used as business needs change. Consider the following tips when planning and deploying DPaaS resources:
- Fully understand the business data storage and protection requirements to better justify the investment in DPaaS.
- Determine what constitutes "data protection" in the organization, such as data backup, disaster recovery, data privacy, archiving or replication.
- Examine data protection activities in the context of current and future business requirements, and identify how an expanded data protection regimen will benefit the organization.
- Determine short-, medium- and long-term storage requirements, and identify business activities that could affect data storage, such as a corporate merger or acquisition.
- Assess current in-house data backup and recovery capabilities to determine whether DPaaS can improve the organization's ability to recover from a disruptive event and return to business as usual.
- Perform a risk assessment to identify potential DPaaS risks, threats and vulnerabilities.
- Determine governance, risk and compliance needs for data protection as a service, specifically how DPaaS can improve governance, reduce the risk of data loss or corruption, and ensure compliance with standards and regulations.
- Review and update business continuity and technology disaster recovery plans to incorporate DPaaS.
- Consider a phased implementation, starting with DPaaS as a secondary data backup and protection resource, and expand its applications in other ways, such as deduplication, to improve overall data protection.
- If DPaaS comes with an AI component, use the offering with restraint until its capabilities and value can be measured.
- Periodically conduct tests of DPaaS resources to ensure the protected data remains secure and available.
- Review and update data protection policies and procedures based on the increased use of CSP- and MSP-provided DPaaS offerings.
- If an SLA is in play, periodically review DPaaS performance against SLA specifications.
- Be prepared to consider and reevaluate data protection strategies, including on-site, single-cloud, multi-cloud and hybrid cloud infrastructures.
Loss of critical data from cyberattacks can seriously damage an organization's reputation as well as its ability to function. DPaaS provides IT managers and senior leadership with more options to ensure the protection and availability of data. But services available from CSPs and MSPs must be carefully evaluated and tested before implementation.
Editor's note: This article was updated to expand on the current benefits and risks of data protection as a service as well as include additional tips for planning and deploying DPaaS.
Paul Kirvan is an independent consultant, IT auditor, technical writer, editor and educator. He has more than 25 years of experience in business continuity, disaster recovery, security, enterprise risk management, telecom and IT auditing.








