
freshidea - Fotolia
Risk assessment analysis and BIA data in BC plans
Examine how BIA and RA data are used to formulate business continuity strategies. It's common to bypass these steps, but the data can result in more precise and focused BC plans.
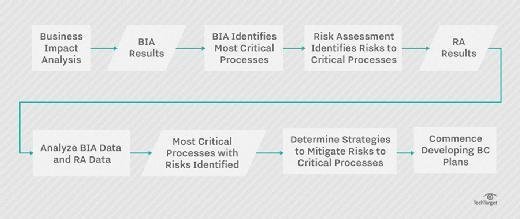
The process of developing business continuity and disaster recovery plans has several stages, but the initial discovery activities include a business impact analysis and risk assessment analysis. The next step is to formulate strategies to deal with the various risks and threats to critical business processes identified in the BIA and RA. The result is a completed business continuity plan.
This article explains the relationship between business impact analysis and risk assessment analysis findings, and then briefly describes how to develop business continuity/disaster recovery strategies and build BC/DR plans.
Business impact analysis data
The results of a BIA identify a number of key areas:
- The most critical business functions and processes to be recovered and restored in the aftermath of a disruptive event.
- Resources the organization needs to support those key operations, such as email, a suite of office applications, databases, laptop computers, Internet access, remote access and phones.
- Key internal and external dependencies, as well as vital records and other documentation whose loss could impact the recovery of critical procedures.
Once the organization has identified the critical business processes and related assets and resources, the next step is to identify and assess the risks and threats that could disrupt the continued business performance.

Risk assessment analysis data
It's important to determine external risks and threats as well as the vulnerabilities within the organization -- such as having only one data center or using legacy systems.
Use a risk assessment process that identifies the following:
- Risks and threats.
- The likelihood that risks and threats could occur.
- The potential damage if they occur.
- The financial implications of the threat occurring.
These risk factors are typically mapped to the critical processes identified in the BIA.
By mapping business impact analysis and risk assessment analysis data, you can zero in on the most critical business processes and the risks and threats that could disrupt them. This data is then used to determine the best ways to mitigate the potential damage to critical business operations if the identified risk or threats actually occur.
Identify business continuity strategies
The next step in the BC planning process is identifying business continuity strategies.
The three-step process of performing a business impact analysis, mapping the risk assessment analysis to the BIA and then defining a strategy ultimately generates the data organizations will use to prepare their BC plans. These results identify and prioritize the most critical business activities and resources, and define how a potential disruption can be mitigated or managed.
Examples of business impact analysis and risk assessment strategies that can be used to overcome disruptions include:
- Data replication to ensure data is current and readily available.
- Alternate work areas in case the main location is unavailable.
- Remote access to corporate systems and applications so people can continue to work during a disruption.
- Use of remotely hosted systems and applications that reduce the chance of a disruption as compared to when systems are locally hosted.







