
Getty Images/iStockphoto
Business impact analysis vs. risk assessment explained
Do you know the difference between a business impact analysis and risk assessment? Find out how they differ and why you need to perform both here.
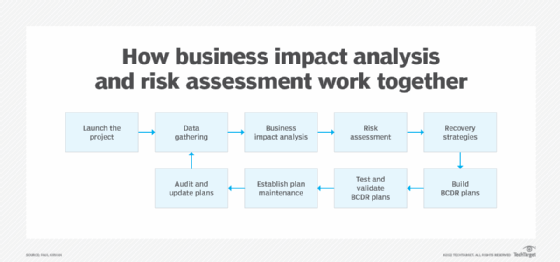
Risk assessments and business impact analyses are two key elements of a DR plan, but they are not interchangeable. For an airtight DR plan, an organization should conduct both a business impact analysis and risk assessment.
At first glance, a BIA and risk assessment might appear to perform a similar purpose. However, each one addresses a different critical aspect of DR planning. A BIA explains the effects of particular disasters and their severity. Risk assessments analyze potential threats and their likelihood of happening.
To understand the differences between a business impact analysis vs. risk assessment, it helps to know the reason behind each process, as well as how and when each is performed.
What is a risk assessment?
A risk assessment identifies situations that might be disruptive to a business. Risk assessments are often done for the business as a whole, but IT-specific risk assessments are also common.
Risk assessments usually identify risks in various areas, including cybersecurity, telecommunications failures and geopolitical incidents. Natural disasters are a common area of concern addressed in risk assessments. For example, an organization in a coastal area might be at risk of experiencing a hurricane. A hurricane could potentially cause a long-term power failure or even flooding of the data center that could disrupt the business.
Risk assessments also commonly include insider-based actions. These risks might be accidental, such as a user deleting a file, or they might be deliberate actions, such as a disgruntled employee who infects the organization with malware.
Sometimes, risk assessments include risks that are not directly tied to the business. For example, a large-scale terrorist attack in the area might prevent a company from doing business for a period, even if the company was not a direct target of the attack. Similarly, ever since the lockdowns that occurred in 2020, many businesses have been planning for disruptions stemming from future pandemics.
What is a business impact analysis?
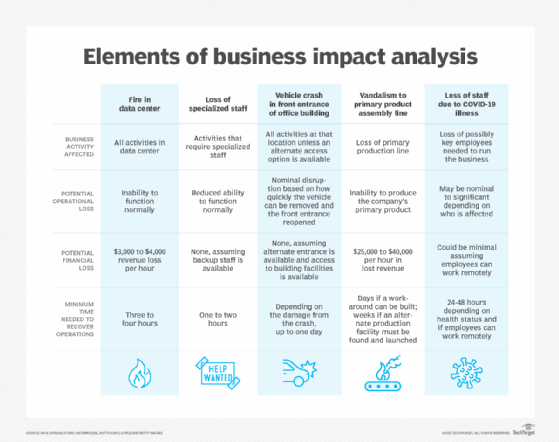
A business impact analysis is a study that seeks to determine how the disruption of key business processes will affect the business.
The contents of the business impact analysis are different for every organization because the report reflects heavily on the nature of the business. For example, one factor that a healthcare organization would likely address in a business impact analysis is HIPAA violations. Such a violation would likely result in hefty fines, though the penalties for major violations could be more severe. In any case, these types of regulatory violations would have an adverse affect on the business.
In contrast, a manufacturing company would not be subject to HIPAA, but the business might have to consider other industry-specific incidents and regulations.
One of the most common factors in a BIA is lost revenue due to the inability to service clients. Another consideration is increased costs due to things such as IT overtime hours, emergency hardware acquisitions or cloud costs. Depending on the incident's nature, the organization might also lose customers who have lost trust in the organization. Additionally, an organization might suffer penalties and legal fees related to a failure to meet its contractual obligations.
Key differences and similarities
A business impact analysis and risk assessment should be considered discrete processes for all practical purposes. Even so, they are far from being unrelated. A BIA is essentially an extension of a risk assessment. Whereas a risk assessment seeks to identify risk factors, a BIA predicts how any identified risks will affect the business if they occur.
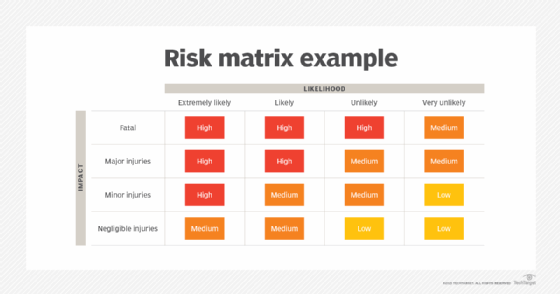
A BIA is like a risk assessment in that both seek to predict how adverse events might affect an organization. A risk assessment seeks to identify risks to the business and the likelihood of the identified events occurring, while a BIA seeks to determine how those events would affect the business.
To put it another way, a risk assessment answers the question, "What risks could potentially harm the organization, and how likely are those risks to occur?" Conversely, a business impact assessment is designed to answer the question, "If any of the identified risks happen, what would it do to the business?"
One key difference between these two types of reports is that a risk assessment examines a broad range of risks, even going so far as to look at risks that might occur outside of the business. For example, a risk assessment looks at internal risks, such as compliance violations, litigation or the loss of key employees, as well as external risks, like natural disasters, supply chain disruptions, wars and market crashes. A BIA focuses on assessing the business's ability to operate after an adverse event.
Ultimately, both reports are intended to help businesses better plan for the future. A risk assessment helps an organization identify the highest-probability risks, with the goal of developing contingency strategies to prevent the risk from occurring or minimize the damage. A business impact analysis can help an organization figure out how to prioritize its resources to be in the best possible position to deal with an adverse event.
Brien Posey is a former 22-time Microsoft MVP and a commercial astronaut candidate. In his more than 30 years in IT, he has served as a lead network engineer for the U.S. Department of Defense and a network administrator for some of the largest insurance companies in America.







