bluesnarfing
What is bluesnarfing?
Bluesnarfing is a hacking technique in which a hacker accesses a wireless device through a Bluetooth connection. It happens without the device user's permission and often results in the theft of information or some other kind of damage to the device (and user).
What makes Bluetooth vulnerable
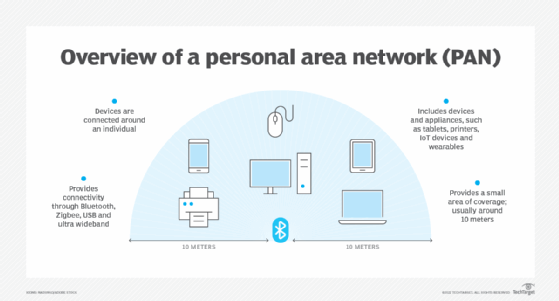
Bluetooth is a high-speed wireless technology for exchanging data between different devices over a short distance. Most Bluetooth-enabled devices have a maximum connectivity range of about 30 feet. The range reduces further when obstacles (such as walls) are present between the devices.
Bluetooth-connected devices are generally safe from hacking because Bluetooth waves are constantly switching frequencies, sometimes hundreds of times per second. This phenomenon is known as frequency-hopping spread spectrum (FHSS). That said, Bluetooth is not completely hacker-safe and Bluetooth-enabled devices are vulnerable to many kinds of attacks, including bluesnarfing. Threat actors stage bluesnarfing attacks by exploiting vulnerabilities in the Object Exchange (OBEX) application-oriented transfer protocol.
The OBEX protocol facilitates the exchange of binary objects or files between Bluetooth-enabled devices. Simply put, these devices use OBEX to communicate with each other. OBEX is used as a push or pull application wherein the push command uploads files to the device, while the pull command downloads them. Since the protocol is "open," there are no authentication policies in place to ask a user for a PIN or for a pairing request. This makes the protocol vulnerable to hacking, particularly via bluesnarfing attacks.
Why bluesnarfing poses a serious threat
Bluesnarfing is one of the most serious threats to Bluetooth-enabled devices. Although Bluetooth has a very limited operating range, some attackers can conduct bluesnarfing attacks from as far as 300 feet away from an unsuspecting victim.
These attacks are directed to devices such as laptops, mobile phones and tablets, whose owners have left the Bluetooth connection open. An open Bluetooth connection makes the device discoverable, which allows hackers to access the device without the user's permission. The attacker can then grab data off the device such as text or email messages, calendar items, contact lists and even potentially sensitive information such as passwords and personal media files.
By exploiting a vulnerability in the way Bluetooth is implemented on a mobile device, an attacker can access information without leaving any evidence of the attack. Operating in invisible mode protects some devices, but only to a limited extent. Devices are vulnerable to bluesnarfing as long as Bluetooth is enabled and left open.
Bluesnarfing attacks can be active or passive. In an active attack, the attacker tries to pair their device with the victim's device without the latter's permission. Passive bluesnarfing or bluesniffing occurs when the attacker only listens to the victim's Bluetooth connection, allowing them to gather data from the device.
When bluesnarfing was first detected
Bluesnarfing is one of the earliest Bluetooth vulnerabilities, reported as early as 2003. In November of that year, security expert Adam Laurie verified what Marcel Holtmann, a Bluetooth developer, had revealed just a few months prior -- that Bluetooth devices have a serious security flaw that could allow them to be compromised.
Laurie released a vulnerability disclosure detailing the vulnerabilities in the authentication and data transfer mechanisms of Bluetooth-enabled devices. He revealed that data could be obtained anonymously without the owner's knowledge or consent and that previously-paired devices could access the complete memory contents of some devices (even after the devices are removed from the list of paired devices with the original device).
Researcher Martin Herfurt discovered another vulnerability. He revealed that attackers could potentially access data, voice and messaging services by compromising a mobile device via a bluesnarfing attack.
How a bluesnarfing attack works
A bluesnarfing attack can compromise any device when its Bluetooth function is turned on and is set to be discoverable by other devices within range. Attackers usually target crowded places like train stations and malls to launch bluesnarfing attacks. In the past, they would scan for discoverable Bluetooth devices, then they would pair with the device and attempt to establish access to it. If successful, they would be able access information on the device.
Today, most attackers use software to exploit the vulnerabilities in Bluetooth-enabled devices. One such application is bluediving, which scans and identifies Bluetooth-enabled devices with a vulnerability in their OBEX protocol. After the attacker pairs with the vulnerable device via Bluetooth, bluediving exploits the vulnerabilities, allowing the attacker to access the compromised device and download data without the victim's knowledge or notice.
The potential impact of bluesnarfing attacks
The main purpose of bluesnarfing is to covertly retrieve information from the target device. Hackers often sell this information to other criminals, usually on the dark web. In some cases, they may use cyberextortion, demanding a ransom from the victim in exchange for returning the information.
In addition to stealing the victim's data, some skilled hackers may also hijack a device to access its messaging and calling capabilities. The device might then be used to make intimidating calls such as bomb threats, or to conceal their identity while committing other crimes.
Bluesnarfing attacks may also be used to do the following:
- Download data from the compromised device to their own device (thus creating an exact copy of the device).
- Install malware on the device.
- Use the sensitive data to defraud other victims (e.g., by posing as the first victim).
- Commit identity theft.
- Damage the victim's reputation by making their private information public.
Bluesnarfing attacks can also impact businesses. Any Bluetooth-enabled device that is paired to a business network creates opportunities for hackers to hack into other connected devices. Once a successful attack is achieved targeting one device, the attacker can potentially gain access to all the other devices on the network that the original device is connected to (via Bluetooth).
How to prevent bluesnarfing attacks
One of the safest and easiest ways to prevent a bluesnarfing attack is to turn off Bluetooth on mobile devices when it's not in use. Other useful prevention strategies include the following:
- Switch off the device's Bluetooth discoverability option to prevent other devices from pairing with it.
- Secure the device with two-factor authentication (2FA).
- Avoid Bluetooth pairing (accepting pairing requests) with unfamiliar or unknown devices.
- Avoid pairing or sharing information over Bluetooth over public or free Wi-Fi networks.
- Keep the device updated with security upgrades and patches.
- Protect the device with a strong PIN.
- Limit the number of apps that have access to the device's Bluetooth connection.
Bluesnarfing vs. bluejacking
Bluejacking is another Bluetooth hacking technique. With bluejacking, a threat actor sends unsolicited SMS messages using unsecured Bluetooth connections. However, the attack is mainly intended to send unauthorized messages or data to a Bluetooth device, rather than stealing information as with bluesnarfing. Thus, bluejacking is considered a low-level threat compared to bluesnarfing.
That said, many attackers leverage bluejacking as a core part of their bluesnarfing strategy. The unauthorized bluejacking messages can find vulnerabilities in the OBEX protocol of Bluetooth-enabled devices, which may then allow an attacker to initiate a bluesnarfing attack.
Learn 7 mobile device security best practices for businesses and see 10 Tips to Keep Personal Data Safe and Secure.







