10 tips to keep personal data safe and secure
Security should always be a concern when online. Whether at a larger organizational level or at an individual level, you should have at least some way to keep your data safe.
Security should always be on your mind when online. Whether at a larger organizational level or at an individual one, you should always have at least some way to keep your data safe. And the more data you must protect, the more important the act of data protection becomes. You should be asking yourself how you can keep that data safe and secure, especially if that information can be used against you by hackers, scammers or other threat actors.
Personal data normally refers to data that can identify a person, such as credit card information, bank account information, Social Security number (SSN) or other sensitive data. Data protection includes safeguarding important information from corruption, compromise or loss. A large part of data protection is ensuring data can be restored quickly after situations such as data loss and corruption. Other key components of data protection include protecting and safeguarding data from compromise in the first place.
To accomplish this, you should always know who you're sharing information with, maintain the appropriate security on your devices, and know how to appropriately dispose of your data once you no longer need it.
Tips for protecting against data security threats
Data security can take many forms when defending against seemingly limitless threats. Often, the answer to how to protect personal information from data breaches comes down to common sense; however, some technical concepts around security may be harder to understand. Here are 10 tips that can help you gain a better understanding of some basic and more complicated approaches you can take to personal information security.
1. Passwords
Weak passwords can be guessed, and even strong passwords can be figured out through methods such as brute force attacks. Creating a strong password will at least make it harder for a hacker to guess it. However, you should have a different password set for each application you use, and you should not write those passwords down. A password manager may be able to help you remember them and create strong, unique passwords for each site.
Ways to prevent something like a brute-force attack are mostly on the developer side. Approaches such as limiting failed login attempts, using CAPTCHA, or monitoring server logs can help avoid these attacks. Likewise, some websites and apps use multifactor authentication, which is recommended for users to set up. Although it is not 100% unbreakable, it can significantly increase security.
2. App privacy settings
Even though application security can apply to desktop devices, the term is used mostly in reference to mobile apps. Some apps request more privileges than they really need in the name of data collection. These permissions allow them to access numerous data sources on the device, possibly including contacts, browsing history and geolocation. If you want to limit this access, you should be able to do so in your phone settings.
Likewise, some phones might record and share usage analytics with the manufacturer to improve their function; users should make sure to turn these off. For example, iPhones might share iPhone analytics and Siri usage data with Apple.
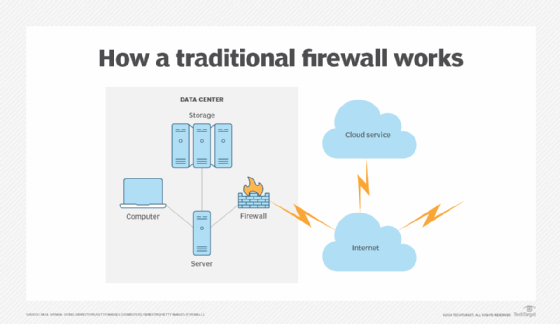
3. Firewalls and antivirus
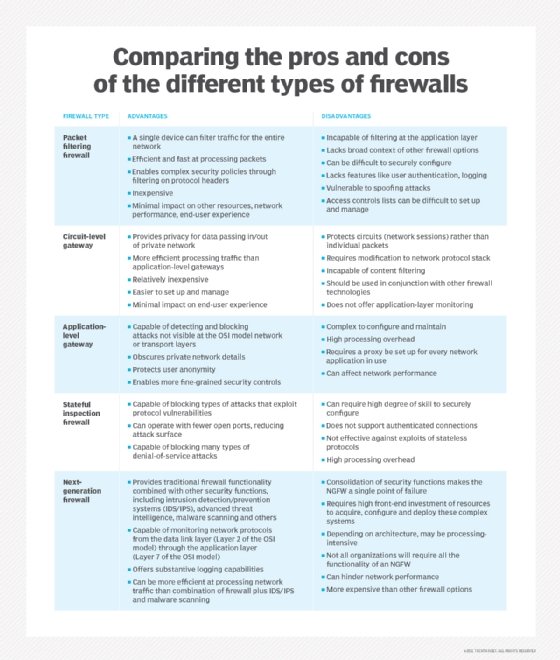
A firewall is a software or firmware that prevents unauthorized access to a network. Many devices come with one built in and are widely considered an essential component of network security. A firewall helps keep personal data secure by inspecting incoming and outgoing traffic, using a set of rules to identify and block threats. Firewalls are used both in personal and enterprise settings. Firewalls also perform important logging and audit functions to keep a record of events. Different types of firewalls include packet-filtering, stateful inspection, proxy and next-generation firewalls.
Antivirus software is a security software program designed to prevent, detect and remove malware infections. Antivirus software can be used on individual computing devices, networks and IT systems to protect personal data. Originally, antivirus software was designed to detect and remove viruses from computers, but it can also protect against a wide variety of threats, such as spyware, botnets, ransomware, keyloggers and other malicious software.
4. Backup data
Backing up your data refers to copying the physical and virtual files or databases to a secondary location for preservation in case of equipment failure or attack. Backing up data is considered pivotal to disaster recovery plans. Additionally, it's the best option for recovering from ransomware attacks or from major data losses. Personal data that is important should be backed up to a separate drive, device or location. Individuals can even follow the 3-2-1 backup rule, where you keep three copies of your data on two types of storage media, and one copy offsite.
Backups essentially capture and synchronize a point in time that you can use to return data to its previous state. If you have personal data that regularly changes, then you should regularly back up devices that have the personal data on them.
5. Anti-theft
Anti-theft refers to data protection and theft prevention when data is in transit or at rest -- when it's in use or not. Protecting data that's at rest normally involves just managing who has access to that data, along with basic security protections such as the use of firewalls, encryption and threat monitoring. Protecting data in use or transit can involve basic security precautions and more complicated precautions. Anti-theft, antimalware and encryption tools are more commonly used in enterprise scenarios.
Some examples of anti-theft tools for personal use include McAfee Total Protection or Absolute Home & Office.
6. Bluetooth vulnerabilities
Bluetooth devices can also leave personal data vulnerable. Personal data could be accessed through Bluetooth in several ways. Bluesnarfing is when a hacker pairs with a Bluetooth device without the user's knowledge to compromise personal data. Hackers could also eavesdrop on calls by accessing the mobile device or a Bluetooth headset in use. Denial of service attacks can also be a worry when it comes to Bluetooth devices. It's recommended to keep Bluetooth off when not in use to avoid compromising personal data. In addition, users shouldn't accept pairing requests from unknown devices.
7. Updates
You should always keep your devices and applications updated to ensure they have the latest performance and security updates. This goes for the operating system on a desktop or the OS on a mobile device. Mobile device OSes tend to get updated often, so it's important to check every so often for those updates.
Security patches for software can also help to close known vulnerabilities exploited by attackers.
8. Public Wi-Fi
Even though it may be hard while traveling, you shouldn't connect to unsecured Wi-Fi networks. Aside from public Wi-Fi networks lacking security in most cases, some of them may not even be real. If you go to a public spot and see "Free Public Wi-Fi" or "Guest Wi-Fi" show up on your phone, the unsecured wireless network may be from a nearby laptop or smartphone that is attempting to connect to other devices to steal personal information. Ideally, you should only connect to known, trusted SSIDs and authenticated access points. Use 5G, 4G or LTE on your device when you can, if you're out and about -- or even a Wi-Fi hotspot aggregator.
9. Secure personal information offline
One of the simplest ways to secure personal information is to secure personal data on a device that doesn't connect to the internet. For example, physical data can be kept in a location out of view in your home or in a safe. If it's digitalized data, then keeping that data in a separate external hard drive will keep it offline when it is not actively connected to a computer, at least. You can then store that hard drive in a secure physical location of your choosing.
10. Stay alert to hoaxes and impersonators
There's no shortage of scams and impersonators, especially on the internet. For example, a virus hoax can give you a false warning about a computer virus. In this example, a warning may arrive in an email with a message about a virus, prompting you to click a link that takes you to a website that will end up harming your computer. Other scams may try to steal enough of your personal information so they can steal your identity, which can affect numerous things, such as your credit report.
Sometimes an entity may pose as someone they're not to phish for your personal information. These impersonators compose an official-looking email from a company, then state that you have been charged for something you have not bought or have signed in from another location -- among other things -- then bring you to a fake site to sign in so they can gain your username and password information.
One easy way to tell if an email is a phishing scheme is by the sender. Smartphones may simplify the email to just say something like "Amazon," for example, but when you tap on the email address itself, it will show a different email address, often something unreadable. To keep your online privacy and data safe, it's best not to respond to emails like this or to simply delete them.
You should also limit the sharing of your personal data on social media or other locations. That information could be used to guess passwords or security questions or in social engineering and phishing attacks.
Where does personal data exist?
Your personal data can exist offline in physical spaces such as personal financial documents and records, or online in a digital context. Keeping offline personal data safe is relatively simple and comes down to common sense a lot of the time. For example, you'd want to keep documents, or anything with personal information on it, locked somewhere safe and out of view. Keep your wallet or purse in a safe place at work. Don't keep your SSN in your wallet or purse. Before giving your information out to anyone, ask why they need it and how it will be kept safe. Shred anything with personal data on it that you don't need anymore, like insurance forms, checks or bank statements. Keeping offline personal data safe relates to being mindful of where your personal information is and how you share it.
Online personal information can be a little more complicated when it comes to keeping it safe. Digital personal information could exist on smartphones, desktops, laptops, IoT devices, other online devices and cloud services. You may have granted businesses access to your data, so they could be holding personal information on a server on-premises or on a remote server in a cloud storage service. In these cases, it is good to inquire how they secure your data, since it will differ per company. In addition, regulations such as GDPR and the California Consumer Privacy Act have made it easier to request to see what personal data an organization holds about you, and to request the deletion of said data.
How to safely dispose of personal data
Deleting a file does not remove it from storage media -- in most cases, at least. It marks that piece of storage space as available to write over. One of the most time-tested methods for dealing with unwanted personal data is by overwriting that data with meaningless binary. This process should be relatively easy, but it's not 100% secure either. With the right tools, data can still be retrieved from an overwritten disk.
You could also physically destroy the device the data is on. This method is effective, but you have to be sure you're safe while doing it. You could also give your device to a data destruction service that will go through the process of data destruction for you. Disk wipes are yet another option. You can wipe all the data on a disk with a free disk wiping software.
Wiping SSDs is different from wiping an HDD. If the manufacturer's secure erase tool is available, you should use it to ensure proper data erasure on SSDs.
Data protection can be a difficult process, but there are actions to address it. Learn about six different data privacy challenges and how to fix them.
Alexander S. Gillis is a technical writer for WhatIs. He holds a bachelor's degree in professional writing from Fitchburg State University.






