network access control (NAC)
What is network access control (NAC)?
Network access control, also called network admission control, is a method to bolster the security, visibility and access management of a proprietary network. It restricts the availability of network resources to endpoint devices and users that comply with a defined security policy.
The NAC can also provide endpoint security protection such as antivirus software, firewall, and vulnerability assessment with security enforcement policies and system authentication methods.
What is the importance of network access control?
NAC is critical for modern businesses because it allows organizations to monitor the devices and users -- authorized and unauthorized -- trying to access the network.
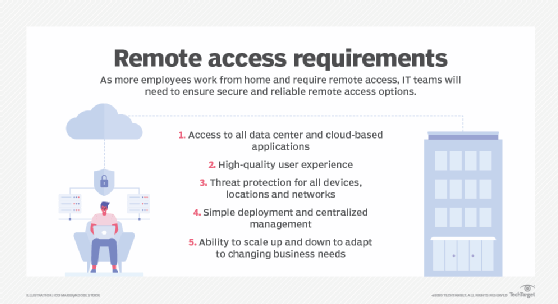
Unauthorized users include cybercriminals, hackers and data thieves, and other bad actors that an organization must keep out. But businesses must also be gatekeepers for authorized users. This particularly applies to organizations that allow remote access to the enterprise network from non-corporate devices like mobile phones, laptops and tablets, or companies that allow employees working in the office to use personal devices. Both scenarios create security risks demanding organizations to address network security.
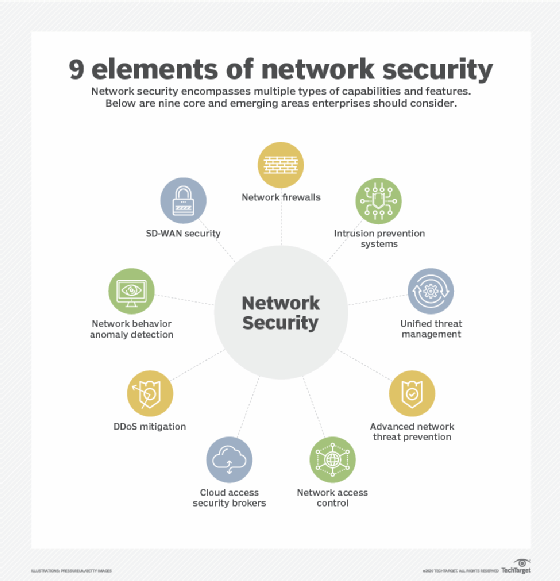
NAC is one aspect of network security. It provides visibility into the devices and users trying to access the enterprise network. And it controls who can access the network, including denying access to those users and devices that don’t comply with security policies. NAC solutions and tools help companies control network access, ensure compliance and strengthen their IT infrastructure.
What are the types of network access control?
There are two types of NAC, including the following:
- Pre-admission: evaluates access attempts and only allows entry to authorized devices and users.
- Post-admission: re-authenticates users trying to enter a different part of the network; also restricts lateral movement to limit the damage from cyber attacks.
What is a network access server?
Many NAC functions are performed by a network access server. A traditional network access server is a server that performs authentication and Authorization functions by verifying user logon information. Also known as a media access gateway or remote access server, a network access server handles remote logins, establishes point-to-point protocol connections and ensures that authorized users can access the resources they need.
A network access server can function in several ways, such as the following:
- Internet service provider: enables authorized customers to access the internet.
- Virtual private network (VPN): gives remote users access to a private enterprise network and resources.
- Voice over Internet Protocol: allows users to access communication applications over the internet.
A network access server can also support the following:
- Network load balancing to distribute traffic and improve reliability and performance;
- Network resource management to manage and allocate resources for networking processes; and
- Network user sessions to track users, store their data and persist their specific state.
What are the common use cases for network access control?
NAC tools are proactive and designed to stop unauthorized access before it happens. They protect an organization’s network perimeter including the physical infrastructure, devices, software, applications and cloud-based assets.
There are many use cases for NAC:
- Bring Your Own Device: Protects from vulnerabilities created when employees use their own devices or use company devices from remote locations.
- Network access for non-employees (vendors or partners): NAC with VPN allows external users to access the corporate network (or specific parts of it) through a secure self-service portal.
- Internet of things (IoT): Prevents cybercriminals from exploiting IoT devices connected to the enterprise network but often overlooked in terms of security and monitoring.
- Incident response: Identifies compromised devices and automatically disables access to prevent an attack from spreading across the network.
NAC tools are also useful for security and authentication in specific industrial use cases, such as medical devices and healthcare systems.
What are the capabilities and goals of network access control?
NAC devices enforce security policies across all users and devices on a network through multiple capabilities, such as the following:
- Limit network access to users and specific network areas;
- Prevent data access by unauthorized employees and cybercriminals;
- Block access from endpoint devices (e.g., mobile phones) that don’t comply with enterprise security policies;
- Manage policy lifecycle for multiple operating scenarios;
- Recognize and profile users and devices to protect them from malicious code; and
- Integrate with other security solutions through application program interfaces.
How to choose a network access control product
NAC offerings cover a broad range of capabilities and use cases. To find the right one, consider these factors:
- security strategy maturity
- budget, price and upfront investment
- native integration with existing software
- type of proactive tools provided
NAC may not work for every organization. In some cases, it may not -- for example -- be compatible with existing security controls. However, it is ideal for businesses where the user environment can be controlled, as it provides strong protection for valuable or sensitive network assets.






