Federal Information Security Modernization Act (FISMA)
What is FISMA?
The Federal Information Security Modernization Act (FISMA) is United States legislation that defines a framework of guidelines and security standards to protect government information technology operations from cyberthreats. This risk management framework and its metrics were signed into law as part of the Electronic Government Act of 2002, later updated and amended in 2014.
Since 2002, FISMA's scope was widened to apply to state agencies that administer federal programs as well as private businesses and service providers that hold a contract with the U.S. government. Reduced federal funding or other penalties may result from noncompliance.
The Electronic Government Act was introduced to improve the management and security of electronic government services and processes. It was also intended to help manage federal spending around information security. FISMA was one of the more important regulations in the Electronic Government Act because it provided a method to reduce federal data security risks with a set of information security policies while emphasizing cost-effectiveness.
What does FISMA require?
FISMA requires federal agencies, and the other organizations it applies to, to develop, document and implement agencywide information security programs. These programs should be able to protect sensitive and confidential information. The act also describes responsibilities of the National Institute of Standards and Technology (NIST) and the Office of Management and Budget (OMB).
The 2014 version of the law has OMB and the Department of Homeland Security's Cybersecurity and Infrastructure Security Agency sharing oversight of federal cybersecurity programs. An update to FISMA was proposed in 2023 but hasn't passed by Congress. Among its proposals is a requirement for federal agencies to report all cybersecurity incidents and regularly performing standardized cybersecurity activities.
Under FISMA, chief information officers (CIOs) inspectors general and other agency officials must conduct annual reviews of an agency's information security program and report those reviews to OMB. That agency issues an annual FISMA guidance document, titled Fiscal Year 2024 Guidance on Federal Information Security and Privacy Management Requirements, which covers requirements for agency cybersecurity reporting. Another supplemental document, titled Fiscal Year 2024 FISMA CIO Metrics, provides the questions agencies are required to answer under FISMA Guidance.
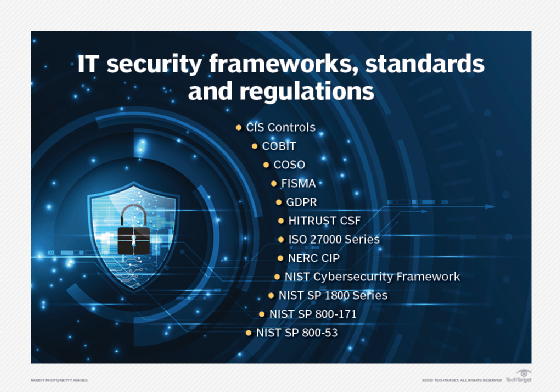
NIST develops standards and guidelines, such as minimum security requirements and controls needed for FISMA compliance. NIST SP 800-53 Rev. 5: Security and Privacy Controls for Information Systems and Organizations defines the controls needed for FISMA compliance.
How does FISMA compliance work?
FISMA assigns responsibilities to various agencies to ensure the security of data in the federal government. The federal law requires program officials and the head of each agency to conduct annual reviews of information security programs, with the intent of keeping risks at or below specified acceptable levels in a cost-effective, timely and efficient manner.
NIST outlines steps required for FISMA compliance as follows:
- Categorize risks. Information systems should be categorized based on objectives that provide an appropriate level of security. Categorization must done by order of risk level, where sensitive information has a high level of security.
- Select minimum baseline controls. Federal systems must meet minimum security requirements. Not every security control has to be met, just ones most relevant to the specific organization and the systems they use.
- Document the controls. An inventory of all the information and systems used as well as the interfaces between systems and networks should be kept. Documentation on the baseline controls used to protect these systems should also be kept. Security controls should then be implemented on appropriate information systems.
- Refine controls using a risk assessment procedure. Risk assessments must be done to validate security controls and determine if any others are needed. Organizations assess the effectiveness of the security controls once they have been implemented.
- Review annually. Annual security reviews must be conducted by program officials and agency heads to obtain a certification. Certification proves a system is accredited. Certification and accreditation are defined in NIST SP 800-37: Risk Management Framework for Information Systems and Organizations.
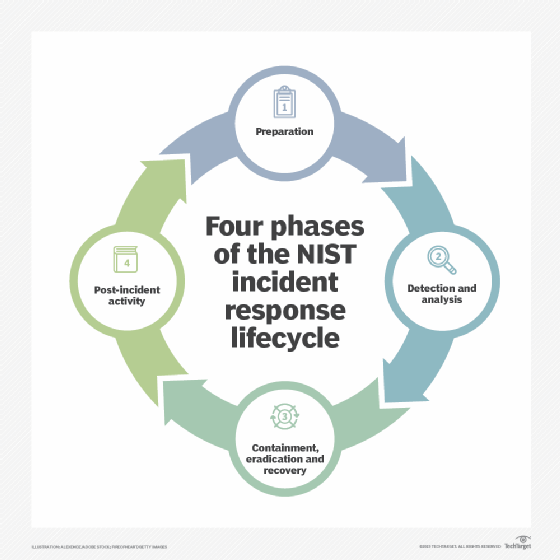
- Continually monitor the security controls. Accredited systems are required to monitor systems. This helps organizations respond quickly to security incidents or data breach.
- Update documentation when changes are made. Updates should include status reporting, configuration management and security controls, and any changes made to a system.
FISMA compliance best practices
Some useful approaches to ensuring FISMA compliance and maintaining evidence for audits include the following:
- Stay up to date with all new FISMA standards and NIST guidelines, such as the NIST Cybersecurity Framework.
- Keep detailed records of FISMA compliance activities, such as steps taken to maintain compliance.
- Classify data based on its level of sensitivity when it was created. This will ensure sensitive information is treated securely.
- Encrypt sensitive data. A tool can be used to do this automatically based on classification levels.
Penalties for FISMA noncompliance
Agencies that don't comply with FISMA requirements must submit reports to the OMB describing why they aren't compliant. They also must explain what corrective actions they're taking and provide a corrective action plan to achieve compliance.
Private contractors working with federal and state agencies can lose funding if they're deemed noncompliant. They can also be restricted from obtaining future contracts.
Pros and cons of FISMA
FISMA is a good starting point for implementing security measures. It provides the following advantages:
- Increased information security for both federal and state agencies.
- Better security policies within the private sector businesses that work with federal and state agencies.
- More baseline controls and security plans.
- A better ability to respond to vulnerabilities.
- Continuous monitoring to ensure a minimum level of security and threat responsiveness is maintained.
- Flexibility in implementation.
However, there are concerns about FISMA:
- Sharing cybersecurity information among agencies can be difficult.
- FISMA updates don't always keep up with new threats.
- FISMA measures security planning as opposed to actual information security.
- Controls can be confusing and are easy to confuse with one another.
For most organizations, FISMA is best used as a starting point for implementing security measures and a security program.
Learn all about data security -- including what's required, the tools and technologies to use, and the best practices to follow -- in our comprehensive guide.




