What is risk exposure in business?
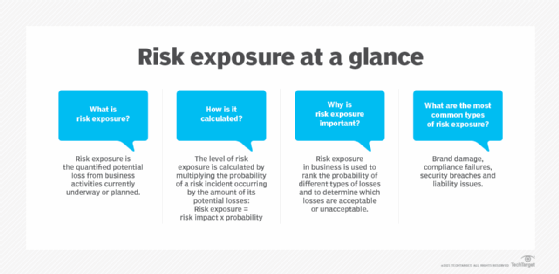
Risk exposure is the quantified potential loss from currently underway or planned business activities. The level of exposure is usually calculated by multiplying the probability of a risk incident occurring by the amount of potential losses.
Risk exposure in business is often used to rank the probability of different types of losses and to determine which losses are acceptable or unacceptable. Losses might include legal liability, property loss or damage, unexpected employee turnover, changes in demand, ransom payment to cybercriminals or other activities that could result in a profit or a loss for the business.
The objective of the risk exposure calculation is to help determine the overall level of risk the organization can tolerate based on the benefits and costs involved. The risk appetite is the level of risk an organization is prepared to accept to achieve its goals.
What are the types of risk exposure?
There are two primary categories of risk exposure: pure risk and speculative risk.
Pure risk exposure is a risk that cannot be wholly foreseen or controlled, such as a natural disaster or global pandemic that impacts an organization's workforce. Most organizations are exposed to at least some pure risks, and preemptive controls and processes can be created that minimize loss, to some degree, in these circumstances.
Speculative risk occurs based on an organization's actions and their subsequent consequences. Examples of speculative risk might be choosing a software platform that is later susceptible to critical vulnerabilities or keeping all backups on-site, which is later infected by ransomware.
There are many different types of risk exposure, but the most common include the following:
- Brand damage. Organizations incur brand damage when events undermine or make their image obsolete. These events range from customer service failures to outages, breaches or cybersecurity issues.
- Compliance failures. Compliance risk is an organization's potential exposure to legal penalties, financial forfeiture and material loss resulting from its failure to act in accordance with industry laws and regulations, internal policies or prescribed best practices.
- Security breaches. Security breaches are significant avenues of risk exposure, especially if sensitive stolen data is posted online for others to access.
- Operational issues. Organizations can be legally liable for operational risks, including cybersecurity issues like breaches, data exposure and other events that disrupt business operations and the failure to meet service-level agreements.
- Financial risks. Financial risks include economic downturns caused by fluctuations in interest rates, stock prices and foreign exchange rates. These market risks are outside the company's control but could affect its bottom-line performance.
How do you calculate risk exposure?
Organizations can calculate their risks using the following four-step process:
- Identify and categorize risks. Determine the risks to the organization in terms of financial, operational, strategic and compliance.
- Estimate the likelihood of each risk occurring. An organization can analyze historical data, use statistical models, or apply expert judgment to assess the likelihood of each risk occurring.
- Evaluate the potential impact of each risk. Estimate the potential effect of each risk in monetary terms, such as system disruptions or damage to the organization's reputation.
- Calculate the expected loss. To calculate risk exposure, analysts often use an equation similar to the following:
Risk exposure = probability of risk occurring x total loss of risk occurrence
The following is an easier way of describing this equation:
Risk exposure = risk impact x probability
Thus, organizations must know the total loss in dollars and a percentage representing the probability of the risk occurring. For example, an organization might have a 50% likelihood of being hit by ransomware (0.5 probability); the impact is determined as $2 million in recovery, consulting and loss of revenue. In a simple risk exposure equation, this would work out to:
Risk exposure = risk impact ($2,000,000) x probability (0.5)
Risk exposure = $1,000,000
This simple equation could serve as a baseline indicator for prioritizing risk in risk mitigation programs. It can help stakeholders understand the effects of various potential threats and better protect their assets.
How do you manage risk exposure?
Organizations commonly use the following techniques and tactics to manage risk exposure:
- Risk avoidance. Organizations can alter choices and decisions to avoid risky activities.
- Risk mitigation. Controls and processes can be implemented to help mitigate and minimize risk in many different areas.
- Risk transfer. Organizations can transfer some risk to outside parties through cybersecurity insurance and third-party service arrangements.
- Risk retention. Organizations can always accept risk and accommodate it as part of ongoing operations.
The benefits of managing risk exposure
Effective risk management offers organizations the following benefits:
- Gain competitive advantage. An organization can gain a competitive edge by mitigating risks more effectively than its competitors.
- Improve resource allocation. Effective risk management helps an organization improve its decision-making, which can, in turn, maximize efficiency and minimize waste.
- Mitigate threats. Managing risk exposure can help organizations ensure business continuity and enhance stakeholder trust.
- Improve adaptability. Organizations that manage their risks can increase their ability to pursue new opportunities and evolve.
Organizations can assess their cyber-risk exposure and quantify it in financial terms using the Factor Analysis and Information Risk -- or FAIR -- methodology.







