managed IT service
What is a managed IT service?
A managed IT service is an information technology (IT) task provided by a third-party contractor and delivered to a customer.
In a managed service arrangement, the managed service provider retains responsibility for the functionality of the IT service and equipment, and the customer typically pays a monthly fee for receipt of the service. There are many different types of managed IT service offerings, but the idea behind all of them is to transfer the burden of maintaining IT from the customer to a service provider. In an effective managed services relationship, a customer benefits from predictable pricing and the ability to focus on core business concerns rather than IT management chores.
What services are most commonly used?
The remote monitoring and management of servers, desktops and mobile devices is a common type of managed IT service. Remote monitoring and management is often a basic, foundational service for a managed services provider. And since many managed services provider firms offer this service, there's heavy competition and pressure on profit margins.
The commoditization of basic managed services has compelled managed services providers to differentiate their offerings. One popular direction is managed security services. Customers increasingly demand IT security assistance from their service providers. Accordingly, services providers are developing managed security services practices or partnering with security vendors to provide cybersecurity services.
With the advent of cloud computing, managed IT services have also evolved to include cloud services. Service providers, for example, may focus on infrastructure as a service (IaaS), providing managed public cloud services in conjunction with cloud providers such as Amazon Web Services (AWS), Google and Microsoft. Service providers may also market managed platform as a service (PaaS) offerings or partner with software as a service (SaaS) vendors such as Salesforce in the CRM space and ServiceNow in the service management market.
A provider of managed IT services may also seek differentiation in the communications arena. Examples include managed IP telephony services in which a managed services provider assumes responsibility for voice services within a customer account.
Managed IT service contracts
A master services agreement often sets the terms and conditions under which a managed services provider works with customers. Another important document when offering a managed IT service is the service-level agreement (SLA), which identifies what services the provider will furnish and how successful delivery of services will be measured.
The SLA may be incorporated into a service provider's master services agreement.
MSP pricing
A service provider can charge for a managed IT service in a number of ways. Per-device, per-user and all-inclusive pricing are among the typical pricing models.
A remote monitoring and management service, for example, may be billed on a per-device basis, with the service provider charging a flat fee for each device it manages. A service provider may adjust its pricing to a per-user model if a customer's users work with multiple devices -- laptops, tablets and smartphones, for instance.
All-inclusive pricing, meanwhile, establishes a flat fee for all of the managed IT service offerings a service provider delivers to its client.
Managed IT services are typically billed on a regularly scheduled basis, with monthly fees a common approach. A flat fee billed on a consistent schedule provides customers with predictable pricing and gives the service provider the stability of a monthly recurring revenue stream.
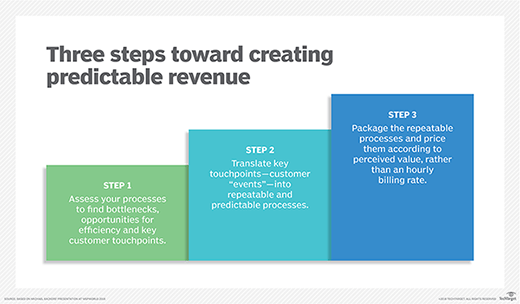
Channel partners historically dependent on an hourly billing rate face a challenging transition when they begin offering managed IT services for a flat fee billed monthly. But aspiring service providers can make a stepwise progression toward a managed services pricing model, taking care to cultivate predictable and repeatable processes.
History of managed IT service providers
The origins of managed IT service providers date back to the 1990s and the advent of application service providers (ASP), which offered remote application hosting services. ASPs set the stage for companies that would provide remote support, versus on-site support, for customers' IT infrastructure.







