
Wolfilser - Fotolia
Cybersecurity budget breakdown and best practices
Once budget is secured, CISOs must figure out where it should be allocated -- as well as how to justify the costs. Get the lowdown on a cybersecurity budget breakdown here.
The need for adding cybersecurity to an organization's annual budget is abundantly clear to most enterprises. But how a CISO allocates and justifies that budget is never quite as straightforward.
Unlike marketing, sales, engineering and support -- where ROI can be more easily explained -- the math of cybersecurity's ROI is not simple. However, with the costs and occurrences of data breaches rising by the minute, securing budget and ensuring it is spent appropriately are more critical for today's CISO than ever before.
Creating a cybersecurity budget breakdown
The amount of money businesses spend on cybersecurity relative to their total budgets varies widely by industry and from organization to organization. As such, it's difficult to prescribe an amount or percentage CISOs should request.
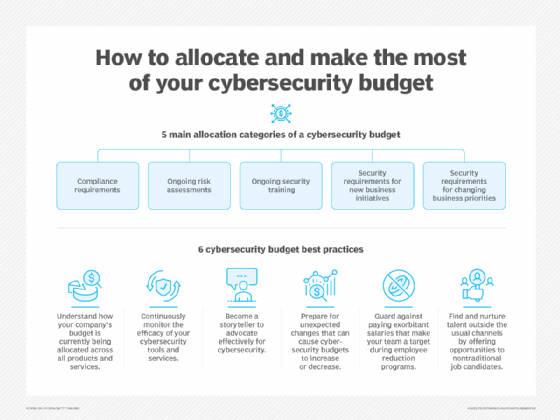
There are, however, generally five main categories all organizations should consider when allocating their cybersecurity budgets:
- Compliance. Certain compliance regulations dictate security budget allocations. In the healthcare sector, for example, HIPAA defines data privacy and security requirements to protect individuals' medical records and other personal health information. To meet these requirements and avoid potentially hefty fines, CISOs must spend budget on particular tools and technologies. In the HIPAA example, this includes data classification, encryption and lifecycle management.
- Ongoing existing risk assessments. Proactive CISOs must continually monitor the efficacy of security controls in their environments and calibrate that against prevalent attack vectors. If risks go above the previously agreed thresholds, CISOs will need to evaluate the threat and either discuss the risks with management to seek further budget or reallocate budget -- or agree to accept the higher risk levels. Tools and services to budget for in this category include cyber insurance, penetration testing, bug bounty initiatives and incident response.
- Ongoing security training. Security training is no longer an event on an annual mandatory compliance checklist. It is imperative that every employee and contractor is included in making this an ongoing effort. Using public shaming or fear to motivate employees is not effective. Instead, cybersecurity training needs to be memorable and even fun. Forward-looking CISOs partner with their business-line counterparts to make this a frictionless yet impactful exercise.
- New business initiatives. Any sort of new business initiative adopted across a CISO's company must be assessed and have security budget applied to it, if applicable, to ensure that the company and its new customers remain secure. For example, marketing departments may outsource content creation to a third-party provider overseas, or customer support may decide to store all customer support cases in a cloud storage platform. Both of these scenarios present additional risks, which must be addressed by CISOs and security teams prior to implementation.
- Business priority shifts. This could be related to people, technology or monetization. From a people perspective, an example of a business priority shift is the hybrid or, in some cases, permanent work-from-home model and the ongoing adaptations required to maintain cybersecurity best practices. From employee onboarding -- and offboarding -- to employee use of shared home routers, local offline data storage, personal devices and home privacy needs in video conferences, all require security adaptations and budget reallocation. Examples of technology shifts include moving to cloud or going hybrid from a single provider or outsourcing engineering; each shift demands reassessment and budget reallocations.
How much is allocated to each category depends on a variety of factors. For instance, new compliance rules could increase spending in that category for that year. An example is the rising cost of data privacy driven by CCPA, which went into effect on Jan. 1, 2020, with enforcement going into effect on July 1, 2020. Additionally, a new investor or new CEO could alter the company's risk appetite, causing a corresponding increase or decrease in what the organization spends on security and thus on how much the CISO allocates to individual security categories.
6 cybersecurity budget best practices
Understanding the present and planning for future needs are key to managing information security budgets more effectively. The following six steps should give CISOs a good handle on budget allocation and justification:
- Understand how budget is being allocated currently. Create a complete inventory of existing products and services, along with the daily, monthly and annual spend for each. Before the advent of cloud and the subscription-based model, this was a more straightforward exercise. Nowadays, with on-demand procurement and commissioning, this task takes much more effort. And this needs to be done periodically -- not at the annual renewal event where vendors will want you to sign the contract with the renewal deadline looming.
- Monitor, monitor, monitor. After conducting a complete inventory, put procedures in place to constantly monitor the efficacy of tools and cybersecurity services, along with processes to fine-tune, reconfigure or even turn them off if needed. Note that product value and renewal cannot be based solely on activity or lack thereof. Products like phishing protection tools, for example, may be battle-tested every day, so their need is obviously justified, whereas other products, such as DDoS or ransomware attack defense systems, may not see use for months, if ever. Rather than base a decision solely on activity, however, look at industry statistics and competitors that have been targets for help in deciding whether a product or service is worth turning off. This step is also an opportunity to assess newer and more cost-effective products or services -- when there is no activity, a swap-out may be less risky.
- Become a storyteller, advocate and confidant. As fellow colleagues across lines of businesses and functions seek to drive efficiency and drive revenue and engagement, the CISO can be an invaluable resource. For example, CISOs could run a full risk report on current products and services used in a particular department and use that as a stimulus to have their colleagues not only understand the effects of a potential cyber attack on those products or services, but also show them how to reduce those potential risk effects. This exercise also makes for a more cost-efficient and forward-thinking approach for CISOs and their colleagues alike.
- Prepare for the unexpected. Unexpected events can cause budgets to expand or shrink. For example, the Log4j vulnerability suddenly expanded the CISO's realm of responsibilities to encompass libraries being used across the organization and the security impact of that. This kind of event can cause cybersecurity budgets to increase. Conversely, CISOs who are not actively advocating for how and why their budget is being spent can quickly become a target when there is an organization-wide budget reduction.
- Manage salary impacts. In the hot cybersecurity job market, where qualified professionals are hard to find -- see the following step for one way to address this -- there could be a tendency to pay high salaries to attract talent. However, this can have a direct negative consequence when there is a need for head-count reduction. When there are Opex reduction targets to be met and head-count reduction is needed, most companies want to keep the number of people impacted to a minimum. And, if fewer people can be impacted by focusing on a handful of highly overpaid cybersecurity personnel, your team becomes an obvious target.
- Find and nurture talent. One demonstrable way to both recruit and retain talent at a reasonable cost point is to invest in communities that may be eager to join the workforce but may not be provided with the requisite opportunity. For instance, veteran communities, local community colleges, career switchers etc. Investing in these groups takes time, budget and effort, but the payout could be meaningful and long lasting.
Will cybersecurity budgets increase or decrease?
The answer to the big question -- will cybersecurity budgets increase, decrease or stay the same? -- is, of course: It depends. A few triggers that could have an impact on budgets include the following:
- The pandemic effect. One of the biggest impacts of the COVID-19 pandemic is permanent remote working at some organizations or an even more challenging constantly changing hybrid model. Another trend is the Great Resignation, as well as the ongoing economic turmoil and, with it, the constant challenge of security issues with disgruntled employees. These challenges usually result in an uptick in security budget as the reputational and the financial damage they could inflict is substantial.
- Automation to replace or augment human beings. Coinciding with the perceived talent shortage is our rising ability to collect, mine and create effective AI-based prediction models. But it starts with collecting data to make the models effective. For example, threat hunting and bug bounty programs are expensive, and returns are not predictable. AI-based models can be built to last, and the budgets can be gradually increased as their effectiveness to highlight and remediate issues proves out.
- CISOs continue to be effective storytellers and provide context. CISOs who have been successful at strategically and thoughtfully obtaining budget increases are adept at adapting their security narratives to the audience. For instance, in presenting to a diverse board representing different industries, it might be effective to provide each member with a storyline that ties back to their industry lineage and weave in the business issue they can relate to. In doing this, you pave the way for a more fruitful conversation when there is a breach that needs to be explained or a new initiative requiring cybersecurity investment.
- Economic downturn. This new reality could have an immediate and sizable negative impact on any security budget. Preparing for an economic downturn and having a priority list of what to cut down on when there is a need make for a much more prepared outcome than slashing costs under duress.
In short, there are myriad factors in today's world that can have an impact on the cybersecurity budget. Being aware of and prepared for the variables -- from new cyber threats and economic turmoil to technology breakthroughs -- ensures better outcomes for the business and for your cybersecurity organization.







