ITGC audit checklist: 6 controls you need to address
Assess the risks to your IT operations and company infrastructure with an IT general controls audit. Explore six controls to audit and key steps with this free checklist.
Audits are a regular part of corporate life. Given the importance of IT resources to business continuity, audits ensure they're functioning as they should.
Among the audit metrics used to measure IT performance are the Control Objectives for Information and Related Technologies framework developed by ISACA, NIST Special Publication 800-34 Contingency Planning Guide for Federal Information Systems, and ITIL standards and practices for IT service management.
Without periodic audits, senior IT leadership might not have the information or confidence needed to manage an organization's ever-growing business requirements. One of the most effective ways to ensure IT organizations properly manage their critical infrastructure is to conduct an IT General Controls (ITGC) audit.
What is the purpose of an ITGC audit?
Audits are often performed with a focus on risk. Specifically, an ITGC audit identifies potential risks, threats and vulnerabilities to IT operations, data integrity, internal controls, automated controls, and application controls. Whether performed by internal auditors or an external audit firm, IT audit procedures are designed, executed and focused on the risk and operating effectiveness of the controls.
Most of the controls listed in the following sections can help prevent threats to data center and IT infrastructure operations and identify areas for improvement. Results of the ITGC audit provide a useful risk assessment of the IT infrastructure and how it supports business operations. Post-audit, senior IT management will be better able to identify where resources should be used to improve IT performance.
ITGC audit checklist
The table below provides a sample checklist to use as a starting point for planning, scheduling and conducting an ITGC audit. Identifying controls to examine is among the first items to prepare in an audit.
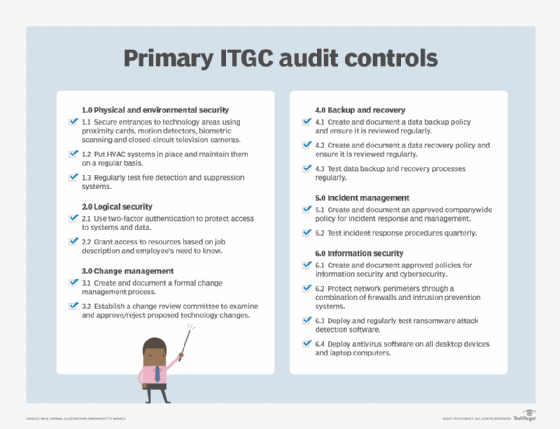
The following sections provide additional details on the ITGC audit checklist above.
Control 1. Physical and environmental security
Data centers, whether large, free-standing buildings or small rooms, must be protected from unauthorized access and unplanned environmental events that could compromise their operations.
Proximity cards, keypad access or biometric access technologies often control data center access. These approaches provide single-factor and -- in more cases -- two-factor authentication to minimize the likelihood of unauthorized personnel entering the data center. Closed-circuit television cameras, typically part of a companywide physical security monitoring system, provide another layer of protection from unauthorized access.
HVAC systems provide a suitable environment for employees working in a data center. They prevent damage to electronic components by controlling the temperature and relative humidity in the data center. Any significant changes in either of these two metrics should be identified and reported to data center managers.
Fire protection systems that detect smoke, excessive heat and fire can activate audible, visual and electronic alerts of the situation and activate chemical-based fire suppression systems, such as FM-200. Overhead sprinkler systems, typically using dry pipe or wet pipe technologies, can also be activated by fire protection systems.
Examples of additional data center controls include the following:
- Limiting the number of employees with card access to the server room.
- Testing access control systems to ensure they are working properly.
- Verifying environmental considerations.
- Installing raised floors with water detectors underneath.
- Checking the server room fire extinguishers quarterly.
Control 2. Logical security
Access to IT systems and services is generally provided to all employees, but not all employees need access to all resources. Access privileges are usually coordinated by HR and IT based on job responsibilities.
System resource access is granted using single-factor -- an employee ID -- or, in most cases, two-factor authentication, such as an ID and a unique password. Biometric authentication -- using a thumbprint reader, for example -- is another effective way to verify users. Multifactor authentication is increasingly the norm for access control, requiring users to provide two or more independent credentials before being granted access.
Examples of additional logical security controls include the following:
- Providing access to system resources for new employees after HR approval and an email noting that approval has been received by IT.
- Conducting periodic tests of user access controls to identify potential threat actors.
- Deleting access credentials for terminated employees within 15 minutes of notification by HR.
- Changing passwords every 90 days.
Control 3. Change management
A well-structured change management function, which often includes a change review committee, ensures all IT infrastructure changes are examined, tested, documented and approved before entering production. Lack of change management can result in the deployment of a system that damages the company's reputation and potentially puts the entire organization at risk. This is especially true with patch management, which must be carefully controlled so patches perform as expected and are monitored and regularly reviewed.
Examples of additional change management controls include the following:
- Segregating test and production environments, using the test environment to validate changes and patches.
- Establishing a change management committee that reviews and approves/denies all change requests.
Control 4. Backup and recovery
Considering the amount of data created daily, backup and recovery have become increasingly important as they protect business processes, data, databases, applications and VMs. Options for backing up and recovering data are numerous and can be locally managed using storage servers and SANs, or remotely configured using managed services or a hybrid of the two. Specialized technologies, such as data deduplication, help make sure that vast quantities of data can be effectively stored.
Backup and recovery are key components of technology disaster recovery (DR) plans, which are essential for business continuity (BC) management and achieving organizational resilience. Admins can use numerous audit controls for backup and recovery, such as the types of data backed up, the frequency and speed of backups, recovery point objectives and speed of recovery in an emergency.
Examples of additional backup and recovery controls include the following:
- Testing data backup procedures monthly.
- Facilitating tests of third-party storage and recovery services.
- Testing recovery procedures quarterly.
- Testing DR plans annually.
Control 5. Incident management
Rarely does a day go by without an event that affects IT operations. Along with the growing risk of cyber attacks, an organization’s physical security can be compromised by environmental incidents such as fires and natural disasters. Senior IT leadership and department heads must be prepared for these events, as they could disrupt IT operations. When such events occur, organizations must identify the event, assess it and decide on its mitigation and resolution. Incident response procedures are especially important with the growing threat from cybersecurity events.
Regardless of the event, incident response procedures and incident management plans must be documented and regularly exercised so that incidents can be quickly addressed and remediated.
Examples of additional incident management controls include the following:
- Creating an incident management team that provides the first response to an incident.
- Training the team regularly on incident response.
- Producing daily incident activity reports for IT management.
Control 6. Information security
Information security is perhaps the most important IT general control because there are so many ways security can be breached. The media regularly reports on significant cybersecurity events, particularly involving theft of individual data records or ransomware attacks that block access to systems.
Senior IT leaders and security teams constantly face the challenge that, as new security remedies emerge, threat actors introduce more powerful attack vectors. Among the control areas most often addressed are an organization's network perimeter, desktop systems and nontechnology security issues, such as social engineering. Cybersecurity events can evolve into BC events, with the attacked organization fighting to protect its customers, business operations and reputation.
Examples of additional information security controls include the following:
- Using intrusion detection and intrusion prevention systems to protect the network perimeter.
- Regularly reviewing and updating firewall rules.
- Deploying antivirus software on all desktop devices and company laptops.
- Threat hunting to identify hackers before they inflict damage.
- Performing penetration testing twice a year to check for vulnerabilities.
- Prohibiting the use of personal laptop devices, unless suitably modified by IT.
Performing the ITGC audit
To get started with an ITGC audit, conduct a kickoff meeting to establish ground rules and a schedule of activities. Access to key subject matter experts is often the biggest challenge in any audit, so discuss that issue with senior management when reviewing the audit plan and schedule.
ITGC audits follow typical audit procedures, such as the following:
- Determine the need for an audit; review with management.
- Secure management approval for the audit.
- Gather an audit team using internal and/or external auditors.
- Prepare an audit plan and secure its approval.
- Identify controls to be audited.
- Obtain evidence -- such as policies, procedures and screenshots of specific activities -- for examination.
- Identify interview candidates; schedule and conduct interviews.
- Schedule and conduct physical examinations of IT activities, such as a data center walkabout.
- Prepare and conduct tests of the identified controls.
- Analyze the evidence and conduct follow-up research, if needed.
- Document audit findings and recommendations in a report.
- Present the audit report to management.
- Invite senior leadership to participate in the post-report analysis to ensure they are in sync with findings and recommendations.
- Prepare a plan to respond to the audit report and provide estimated dates when findings can be remediated.
Throughout the audit, schedule periodic checkpoints with sponsors to brief them on the audit's progress and identify issues that might be hampering it. Carefully document all audit findings from interviews, physical examinations and review of evidence. Report any unusual and potentially negative findings to the sponsors as soon as possible.
Auditors should have a specific work area to conduct interviews, examine evidence and write their reports. Guest access to internet services and a telephone should also be made available to the audit team.
Careful planning and good project management will ensure the audit is completed on time and within budget.
Paul Kirvan, FBCI, CISA, is an independent consultant and technical writer with more than 35 years of experience in business continuity, disaster recovery, resilience, cybersecurity, GRC, telecom and technical writing.







