What are the 5 types of network management?
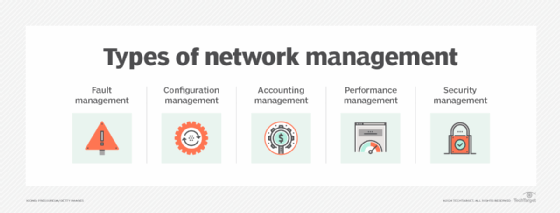
Despite the changes in how organizations optimize network performance, the five foundational elements of network management -- also known as FCAPS -- remain the same.
Network management starts with understanding all the components that constitute a comprehensive IT management strategy. Each network management subdiscipline incorporates several operational elements.
Network management is the process of administering an organization's wired and wireless infrastructure. But it entails more than just ensuring network components work. It is a multifaceted discipline that requires a cohesive effort to provision, configure, secure, optimize and maintain effective enterprise operations.
The ISO outlines five major elements that IT organizations need to address in their network management programs. These operational areas are known as FCAPS and include the following:
- Fault management.
- Configuration management.
- Accounting management.
- Performance management.
- Security management.
Here is a rundown of the different types of network management.
1. Fault management
In many ways, this is the most fundamental area of the ISO network management model. Fault management addresses the ability to maintain operations of the entire network infrastructure. It applies a combination of technology and processes to detect, repair and document errors that interfere with network operations.
This article is part of
What is network management?
Simple Network Management Protocol (SNMP) services identify problems and alert the appropriate IT manager. These tools also report and record issues IT managers can analyze for trends, which can yield important insights into longer-term issues. Network teams can then address those issues to improve performance.
Advances in AI and analytics promise better and faster root cause analysis. Vendors now incorporate both, touting predictive maintenance capabilities to help avoid costly outages.
2. Configuration management
Configuration management is more than just the initial setup of network devices. It also encompasses the ongoing tracking of any configuration changes to the system. Analytics help identify potential misconfigurations and uncover opportunities to improve efficiencies. Because network configuration issues are a major cause of outages, organizations must have effective tools and best practices in place to address every aspect of configuration management.
A crucial part of this process is monitoring and recording any configuration adjustments in both hardware and software. For example, this includes documenting when a new network interface is installed or an OS is refreshed. Although network managers can manually record these changes, it is cumbersome and an inefficient use of resources. Many opt to use configuration management software.
3. Accounting management
Accounting management documents network utilization information. For bookkeeping purposes, accounting management will bill back or track departments or lines of business for usage. For smaller organizations that don't have multiple departments, Chargeback is irrelevant. However, all businesses and government entities must track network use.
This information is essential for cost management. It is also important to recognize trends that indicate inefficiencies caused by configuration issues or other errors. Large enterprises should document which units and users consume bandwidth to justify the relevance of the network to business operations. This type of network management is vital, especially because IT is typically seen as a cost center and under the aegis of the CFO.
Organizations face tightening budgets and are looking for ways to rein in spending. Many rely on analytics tools to identify where to address excessive expenses, such as overprovisioning network services with unwarranted bandwidth.
4. Performance management
Performance management aims to ensure acceptable service levels in the network to support optimal business operations. It collects statistics on network quality of service (QoS) on an ongoing and consistent basis. Network monitoring tools cull performance data on a range of metrics -- either through passive network traffic monitoring or synthetic tests. They then feed that information into performance monitoring applications. These applications compile and analyze statistics on metrics such as link use, packet loss rates and response times.
This data feeds into an SNMP management system, which alerts network managers when service levels drop below or exceed acceptable thresholds. Alert fatigue can be a major issue, and teams might sometimes ignore important fault indicators. Successful performance management requires consistent and accurate monitoring. Network management systems help diminish alert fatigue by correlating network performance data from multiple sources, sometimes associating it with IT data from other aspects of the enterprise, such as application performance data.
Network observability is a big part of performance management. This process applies machine learning, AI and workflow automation to identify QoS issues and elevate operational performance.
5. Security management
Security management is a multilayered discipline within network management. It requires ongoing information collection and analysis. Functions that fall under the security management umbrella include network authentication, authorization and auditing.
Most security management services incorporate foundational capabilities that organizations can use to set and execute security policies, such as the following:
- Network firewall configuration and management.
- Vulnerability management.
- Intrusion detection systems.
- Unified threat management.
Personnel inside and outside the IT organization have come to understand how crucial security is to enterprise operations. Security breaches can lead to data loss and potentially take down an entire network. Security providers use machine learning to expedite threat identification and improve its accuracy. Machine learning distinguishes harmless anomalies from serious security threats, limiting false positives that contribute to management inefficiencies.
Network security management's primary goal is to ensure that only authorized users and devices can access network resources. To do so, it must deflect unauthorized users and devices, malware and other malicious or harmful code. Roles-based components in security management software recognize if users have access to specific resources based on job function.
Recently, thinking has shifted regarding network and security. The shift focuses on tightly coupling security and network services from management and operational perspectives. Vendors are now integrating security services into network gear and services.
The role of FCAPS
By categorizing network management into fault, configuration, accounting, performance and security management, network teams ensure they address every critical aspect of network operations. Altogether, the FCAPS framework provides a structured approach that enterprise network teams can follow to maintain and optimize their networks.
Editor's note: This article has been updated to improve the reader experience.
Amy Larsen DeCarlo has covered the IT industry for more than 30 years, as a journalist, editor and analyst. As a principal analyst at GlobalData, she covers managed security and cloud services.








