Public-Key Cryptography Standards (PKCS)
What are Public-Key Cryptography Standards (PKCS)?
Public-Key Cryptography Standards (PKCS) are a set of standard protocols, numbered from 1 to 15. These standards were developed to enable secure information exchange on the internet by using a public key infrastructure (PKI).
Over the past three decades, PKCS specifications have made a significant impact on the real-world and practical uses of public key encryption.
Public-Key Cryptography Standards explained
PKCS are a set of nonvendor-dependent standards first initiated in the early 1990s. RSA Laboratories devised and published the standards in collaboration with security developers and industry partners from around the world.
PKCS specifications are defined for both binary and American Standard Code for Information Interchange data types. They standardize message syntax and specific algorithms, which can be viewed as different levels of abstraction that are independent of each other. However, the specifications only describe message syntax in an abstract manner without specifying the representation format.
These standards cover the following:
- Rivest-Shamir-Adleman (RSA) encryption
- RSA signature
- password-based encryption
- encrypted or cryptographic message syntax
- private key information syntax
- selected object category and attribute type
- certification or authentication request syntax
- encryption or cryptographic token interface
- personal information exchange syntax
- encrypted or cryptographic token information syntax
A primary goal of developing PKCS was to make different applications from different vendors interoperable. However, security developers also had other aims, namely, to accelerate the deployment of public key cryptography by vendors, foster more secure communications through extensive cryptography and avoid the errors in typical schemes.
RSA Laboratories also published these standards to promote use of its patented cryptography techniques, such as the RSA algorithm and Schnorr signature algorithm.
Public-Key Cryptography Standards evolution and applicability
Initially, PKCS did not become industry standards because RSA Laboratories retained control over them. The company still has exclusive power to decide, control or change any aspect of the PKCS specifications.
But, over time, several other working groups, such as the Internet Engineering Task Force (IETF) and PKI X.509, adapted some of the standards. Today, these standards are periodically updated, widely implemented in practice and ubiquitously implemented in public key cryptography. They have become the basis for many other de facto standards, such as the following:
- Secure/Multipurpose Internet Mail Extensions
- American National Standards Institute (ANSI) X9 documents
- IETF documents
- Secure Sockets Layer/Transport Layer Security
In addition, many kinds of applications, including web browsers and secure email clients, rely on PKCS to interoperate with each other.
PKCS #1 to PKCS #15
Here's a summary of the PKCS standards.
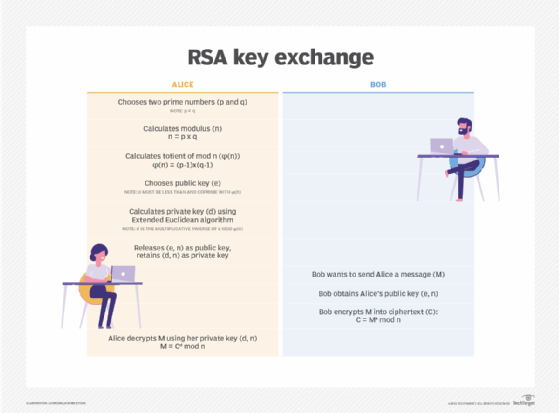
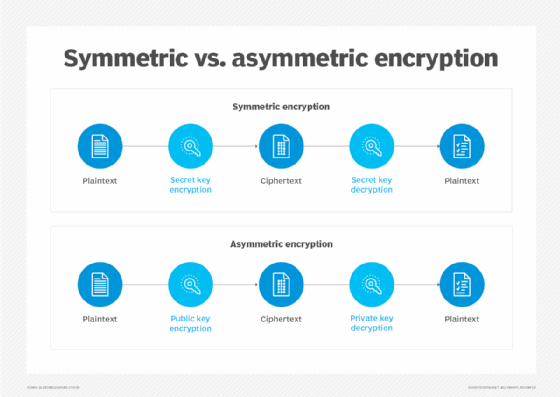
PKCS #1: RSA Cryptography Standard. This standard defines mechanisms to encrypt and sign data using the RSA public key system.
PKCS #2 and #4: Incorporated into PKCS #1 (no longer exist). These standards covered RSA encryption of message digests. They were merged into PKCS #1 and are no longer active.
PKCS #3: Diffie-Hellman Key Agreement Standard. The standard defines the Diffie-Hellman key agreement protocol that enables two parties to agree on a secret key known only to them. PKCS #3 was superseded by modern key establishment schemes specified in IEEE 1363a, ANSI X9.42, ANSI X9.44, ANSI X9.63, etc.
PKCS #5: Password-based Cryptography Standard. This standard applies pseudo random functions -- hash-based message authentication code, cipher or hash -- to the input password, along with a salt value, to produce a derived key that can be used as a cryptographic key. The standard involves additional computation that makes password cracking more difficult, thus providing more enhanced security for password-based cryptographic primitives.
PKCS #6: Extended-Certificate Syntax Standard. Since the introduction of X.509 v3, PKCS #6 is being phased out.
PKCS #7: Cryptographic Message Syntax Standard. This standard defines a generic syntax for cryptographic messages. It is superseded by Request for Comments 3369 for Cryptographic Message Syntax.
PKCS #8: Private-Key Information Syntax Standard. PKCS #8 defines a method to store private key information, including a private key for some public key algorithms. It also includes the syntax for encrypted private key information.
PKCS #9: Selected Object Classes and Attribution Types. This standard defines the selected attribute types for use in other PKCS standards. It defines two auxiliary object classes. PKCS attributes can be packaged into these object classes and exported to other environments, such as Lightweight Directory Access Protocol systems.
PKCS #10: Certification Request Syntax Standard. PKCS #10 defines the syntax for certification requests. When an entity needs a public key certificate, it constructs a certification request and sends it to the certification authority (CA), which transforms the request into an X.509 public key certificate. The standard does not specify the form in which the CA returns the new certificate.
PKCS #11: Cryptographic Token Interface Standard (Cryptoki). Cryptoki defines a technology-independent application programming interface for devices that hold cryptographic information and perform cryptographic functions. It acts as an interface between applications and portable cryptographic devices, like smart cards. Cryptoki presents a standard model of the cryptographic device, known as a cryptographic token, to the application.
PKCS #12: Personal Information Exchange Syntax Standard. PKCS #12 defines the transfer syntax for the storage and transportation of personal identity information, such as user private keys, certificates and extensions. It builds on PKCS #8 by adding essential information and improving security through public key privacy and integrity modes.
PKCS #13: Elliptic Curve Cryptography Standard. This standard defines mechanisms to encrypt and sign data with elliptic curve cryptography. It has never been published.
PKCS #14: Pseudo-random Number Generation. This standard defines the syntax to generate pseudo-random numbers. Like PKCS #13, it has not been published.
PKCS #15: Cryptographic Token Information Format Standard. PKCS #15 defines the format of cryptographic credentials stored on cryptographic tokens, such as integrated circuit cards. Lack of interoperability proves a major challenge to use these tokens for authentication and authorization purposes. This standard aims to address this lacuna.
Open issues in Public-Key Cryptography Standards
To provide PKCS users with more flexibility, PKCS developers have left some open issues across several standards.
| PKCS Standards | Open Issues |
| PKCS #1 | Range of lengths of the RSA modulus |
| PKCS #3 | Range of lengths of Diffie-Hellman modulus |
| PKCS #5 | Range of length of passwords |
| PKCS #5 | Structural requirements of the password |
| All standards | Sources of pseudo-random bits and maximum length of certificate chain |
Learn why experts warn cryptography techniques must keep pace with threats and about the importance of security and data encryption in the cloud. Also, explore what quantum computers mean for cryptography and using cryptographic entropy for more secure keys.








